Apis Apisecurity Documentation Devsecops Applicationsecurity
Devsecops Yi S Blog Within minutes, apisec pulls down every applicable api from the api gateway and analyzes each api to generate thousands of api specific attack playbooks covering every major attack type, including owasp top 10, abac, rbac, bola, and over one hundred others. This blog post is your no fluff, defense first roadmap to securing apis in real world devsecops environments. whether you're building or protecting apis, these tips will help you reduce risk, outsmart bots, and improve your appsec hygiene.

Akto The Leading Api Security Solution Developers tend to trust data received from third party apis more than user input, and so tend to adopt weaker security standards. in order to compromise apis, attackers go after integrated third party services instead of trying to compromise the target api directly. continue reading. licensing the owasp api security project documents are free. A technical guide for developers on api security implementation. learn to find shadow apis, prevent bola attacks with secure code examples (oauth 2.0, jwt), and implement the owasp top 10. Secure api documentation: ensure that your api documentation provides clear and up to date security guidelines, including authentication methods, required headers, and data formats. Learn api security best practices, owasp api top 10 risks, and how to protect apis from attacks, breaches, and misuse in 2026.
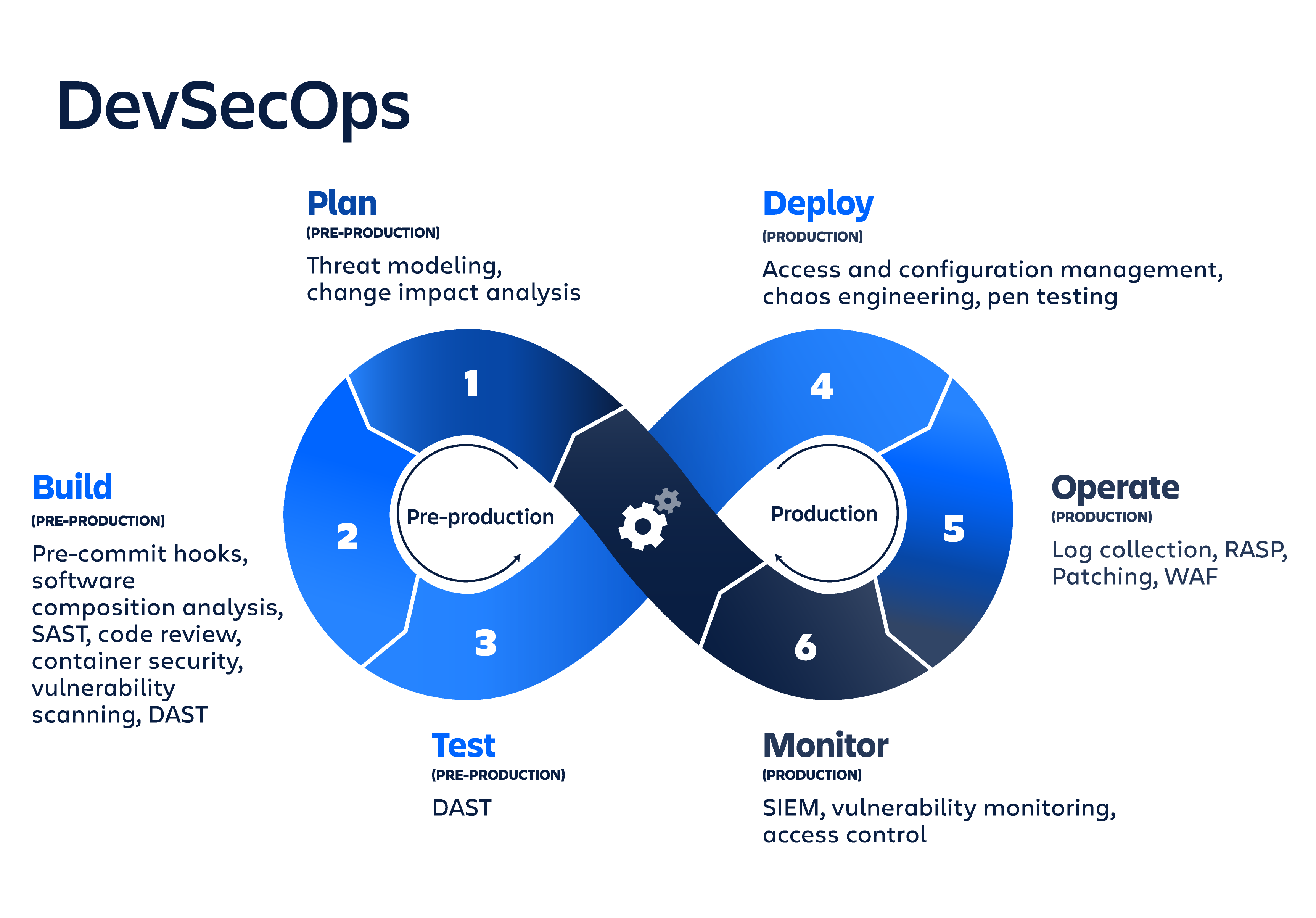
Practical Api Security Discover Defend And Secure Apis From Code To Secure api documentation: ensure that your api documentation provides clear and up to date security guidelines, including authentication methods, required headers, and data formats. Learn api security best practices, owasp api top 10 risks, and how to protect apis from attacks, breaches, and misuse in 2026. Api security is critical in modern devsecops pipelines, where continuous integration and delivery demand proactive vulnerability management. this guide explores essential techniques to secure apis across development, deployment, and runtime stages, addressing owasp api top 10 risks. Ensure your endpoint protection with the definitive api security checklist. authentication, authorization, encryption, and monitoring controls at the edge. This blog explores best practices and considerations for securing apis in a devsecops environment, empowering organizations to mitigate the risks associated with api vulnerabilities and protect sensitive data. understanding api security in devsecops. We’ll dive into the risks apis face, best practices for securing them, and how you can integrate api security into your workflows in a way that scales.
What Is Api Devsecops Dreamfactory Api security is critical in modern devsecops pipelines, where continuous integration and delivery demand proactive vulnerability management. this guide explores essential techniques to secure apis across development, deployment, and runtime stages, addressing owasp api top 10 risks. Ensure your endpoint protection with the definitive api security checklist. authentication, authorization, encryption, and monitoring controls at the edge. This blog explores best practices and considerations for securing apis in a devsecops environment, empowering organizations to mitigate the risks associated with api vulnerabilities and protect sensitive data. understanding api security in devsecops. We’ll dive into the risks apis face, best practices for securing them, and how you can integrate api security into your workflows in a way that scales.

Apis Cybersecurity Devsecops Apisecuritytraining Certified Api This blog explores best practices and considerations for securing apis in a devsecops environment, empowering organizations to mitigate the risks associated with api vulnerabilities and protect sensitive data. understanding api security in devsecops. We’ll dive into the risks apis face, best practices for securing them, and how you can integrate api security into your workflows in a way that scales.
Comments are closed.