Api Security Workflow Api Design Principles Protocols
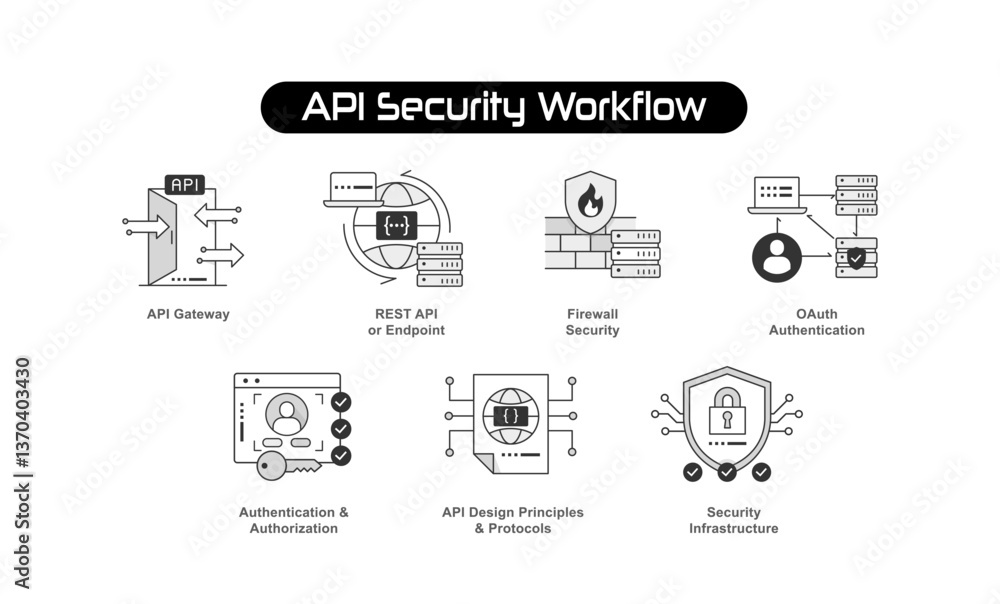
Api Security Workflow Api Design Principles Protocols This article highlights key design principles and best practices to secure your rest api. In this article, you’ll learn the ins and outs of secure api design. we’ll cover core api security principles, essential controls, and how to prioritize security at each stage of the api lifecycle.
Api Design Principles Api Template Pack Many api security problems come down to coding errors or misconfigured infrastructure, but this guide focuses more on the foundational api design decisions that effect the security of an api from day one. That’s why security cannot be an afterthought it must be a core part of your api integration strategy. this blog explores key protocols, best practices, and strategies to help businesses safeguard their apis effectively while supporting seamless operations. Win by treating api security as a lifecycle: design with least privilege, test like an attacker, validate request and response schemas at runtime, enforce policy at edge and service, monitor drift and mttr, and prove outcomes with evidence. use the templates, code, policies, and tests below. In this article, we shall consider the 7 best practices that combine detailed explanations with concise bullet points to sustain robust api shielding against shifting dangers, hence protecting internet assets and improving trust by users. what is api security and why does it matters?.
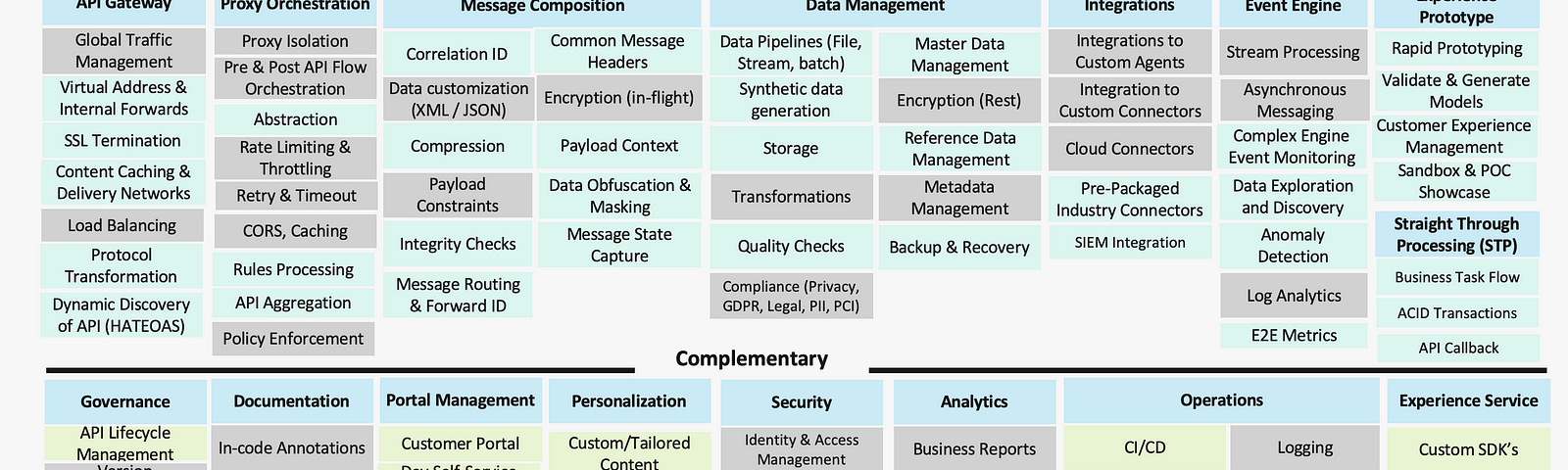
Api Design Principles And Best Practices Medium Win by treating api security as a lifecycle: design with least privilege, test like an attacker, validate request and response schemas at runtime, enforce policy at edge and service, monitor drift and mttr, and prove outcomes with evidence. use the templates, code, policies, and tests below. In this article, we shall consider the 7 best practices that combine detailed explanations with concise bullet points to sustain robust api shielding against shifting dangers, hence protecting internet assets and improving trust by users. what is api security and why does it matters?. Here are 9 essential security principles to embed into your api design process, ensuring your systems stay robust against evolving threats. The design process itself usually follows one of three patterns. top down (start from user workflows), bottom up (start from the data model), or contract first (define the request response shapes before writing code). Api security standards and protocols are sets of rules and guidelines designed to protect the integrity, confidentiality, and availability of data exchanged between different systems through apis. Secure your apis by design. explore architecture strategies, security patterns, and best practices to prevent threats and ensure safe, scalable integrations.

Api Protocols By Wallarm Api Security Leader The Cyber Security Here are 9 essential security principles to embed into your api design process, ensuring your systems stay robust against evolving threats. The design process itself usually follows one of three patterns. top down (start from user workflows), bottom up (start from the data model), or contract first (define the request response shapes before writing code). Api security standards and protocols are sets of rules and guidelines designed to protect the integrity, confidentiality, and availability of data exchanged between different systems through apis. Secure your apis by design. explore architecture strategies, security patterns, and best practices to prevent threats and ensure safe, scalable integrations.

30 Api Design Principles Royalty Free Images Stock Photos Pictures Api security standards and protocols are sets of rules and guidelines designed to protect the integrity, confidentiality, and availability of data exchanged between different systems through apis. Secure your apis by design. explore architecture strategies, security patterns, and best practices to prevent threats and ensure safe, scalable integrations.
Comments are closed.