Api Security Trends
Api Security Trends This research report provides the most in depth and authoritative look at emerging api security trends and vulnerabilities. Looking ahead to 2025, organizations must prioritize api security to safeguard their systems and unlock the full potential of apis as the key driver of business transformation.

Api Security Trends Explore the top api security trends for 2025, including ai, auditable authorization, passwordless authentication, zero trust, and much more. From broken authentication to shadow apis — the 10 most exploited api vulnerabilities in 2026, with real breach examples and detection steps. The q1 2025 state of api security report offers essential insights into the challenges and priorities in api development and security, and gives insight into how organizations are adjusting their strategies in response to the evolving landscape. Learn everything about api security in 2025 key risks, standards, tools, and strategies to secure your apis against modern threats.

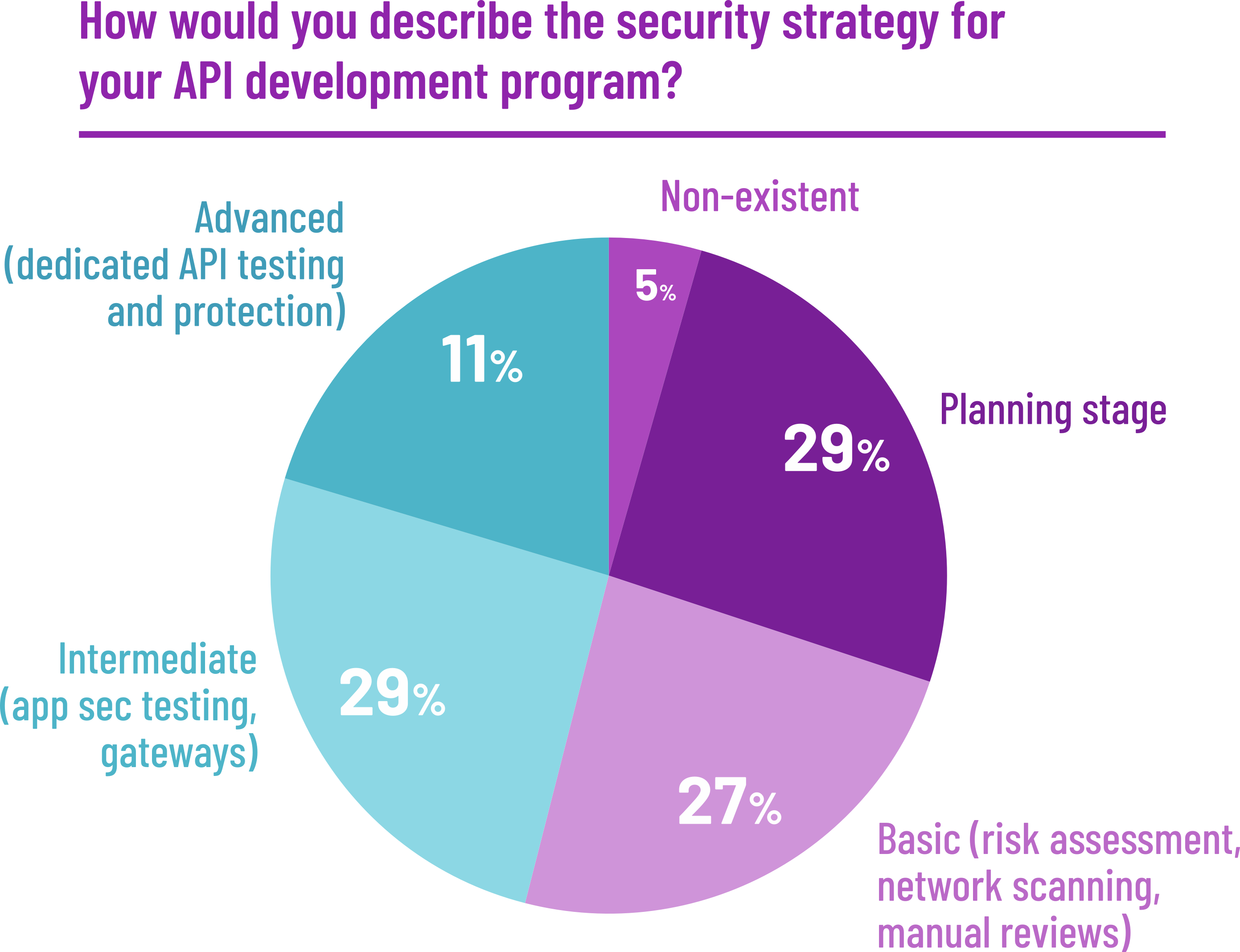
Api Security Trends The q1 2025 state of api security report offers essential insights into the challenges and priorities in api development and security, and gives insight into how organizations are adjusting their strategies in response to the evolving landscape. Learn everything about api security in 2025 key risks, standards, tools, and strategies to secure your apis against modern threats. Explore api security breach statistics to uncover threats, key risks, and real data insights that help you protect systems and stay ahead. Traceable conducts this annual research to provide organizations with an objective assessment of api security risks and trends. Shift left testing, ai threat detection, zero trust, and sbom driven supply chain security trends shaping api security in 2026. Learn api security best practices, owasp api top 10 risks, and how to protect apis from attacks, breaches, and misuse in 2026.
Comments are closed.