Api Security And Authentication Api Newbies

Api Security And Authentication Api Newbies Learn basic concepts of api security and authentication and explore authentication patterns that you'll likely encounter when using rest apis. In this comprehensive guide, you’ll learn what api authentication is, why it matters, the most effective methods, best practices, and how to implement authentication in real world scenarios.

Api Security Fundamentals Apisec University Understanding api authentication is essential for protecting your api from misuse and limiting unauthorized access. by implementing basic authentication, api keys, and token based authorization, you can safeguard your api and ensure it’s used responsibly. Understand api authentication: api keys, oauth 2.0, jwt tokens, basic auth, and bearer tokens. when to use each method, security trade offs, and implementation examples. When it comes to securing apis, different authentication methods work better in different scenarios. below, we compare three commonly used methods: oauth 2.0, jwt, and api keys. for user facing applications, oauth 2.0 is preferred, especially when dealing with third party integrations. Learn how to implement robust api authentication security measures with best practices and example solutions.
Authentication Api Developer Guide When it comes to securing apis, different authentication methods work better in different scenarios. below, we compare three commonly used methods: oauth 2.0, jwt, and api keys. for user facing applications, oauth 2.0 is preferred, especially when dealing with third party integrations. Learn how to implement robust api authentication security measures with best practices and example solutions. A comprehensive guide to securing apis through proper authentication and authorization mechanisms. learn about api keys, oauth 2.0, jwt, rbac, abac, and implementation best practices with practical code examples. Explore api security best practices to protect data, ensure compliance, and boost performance with authentication and zero trust systems. This course provides a comprehensive understanding of various authentication mechanisms and protocols used to secure apis. you will learn about the principles of api security, explore different authentication strategies, and understand how to implement them effectively in real world scenarios. Api2:2023 broken authentication authentication mechanisms are often implemented incorrectly, allowing attackers to compromise authentication tokens or to exploit implementation flaws to assume other user’s identities temporarily or permanently. compromising a system’s ability to identify the client user, compromises api security overall.
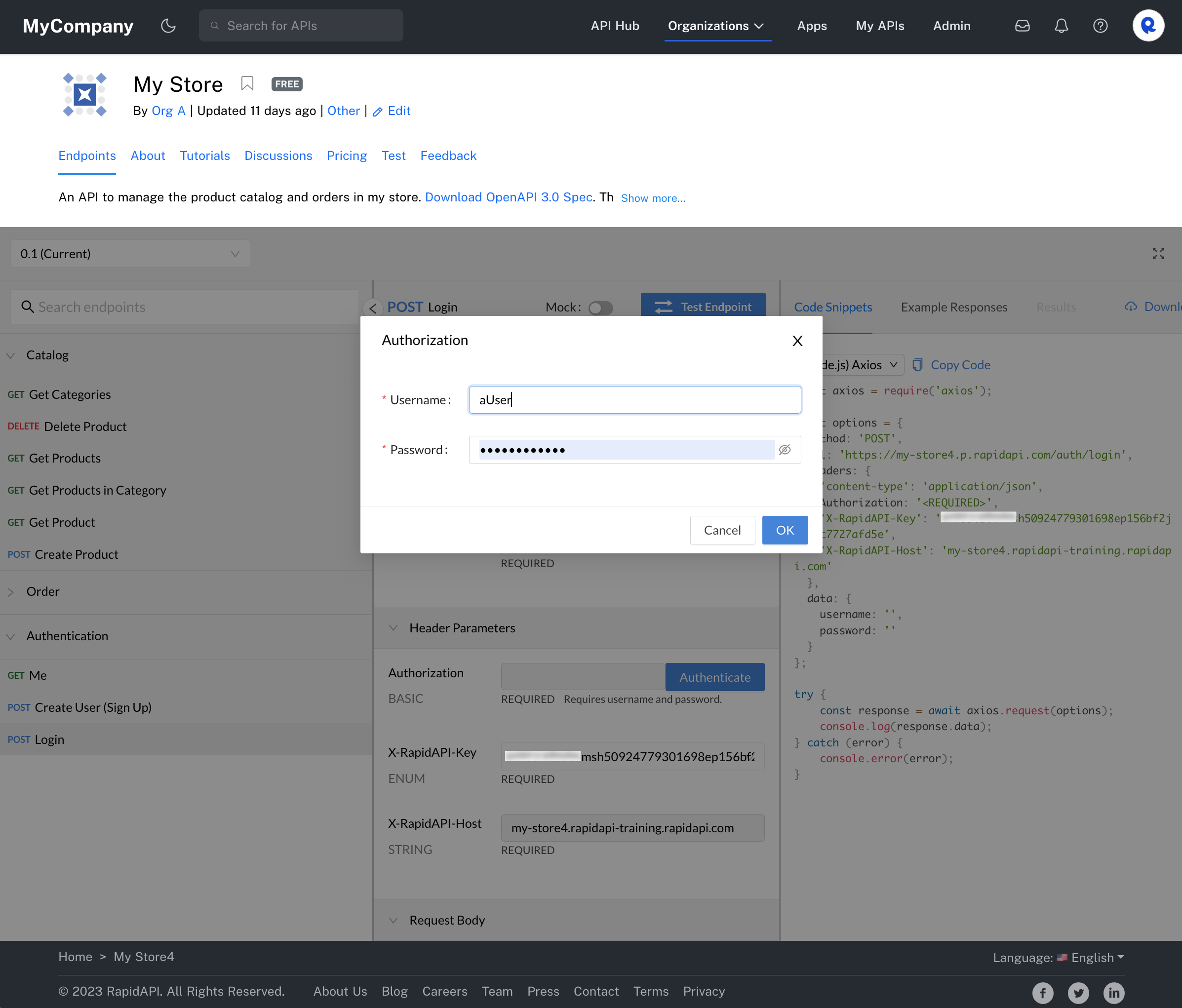
Configuring Api Security A comprehensive guide to securing apis through proper authentication and authorization mechanisms. learn about api keys, oauth 2.0, jwt, rbac, abac, and implementation best practices with practical code examples. Explore api security best practices to protect data, ensure compliance, and boost performance with authentication and zero trust systems. This course provides a comprehensive understanding of various authentication mechanisms and protocols used to secure apis. you will learn about the principles of api security, explore different authentication strategies, and understand how to implement them effectively in real world scenarios. Api2:2023 broken authentication authentication mechanisms are often implemented incorrectly, allowing attackers to compromise authentication tokens or to exploit implementation flaws to assume other user’s identities temporarily or permanently. compromising a system’s ability to identify the client user, compromises api security overall.
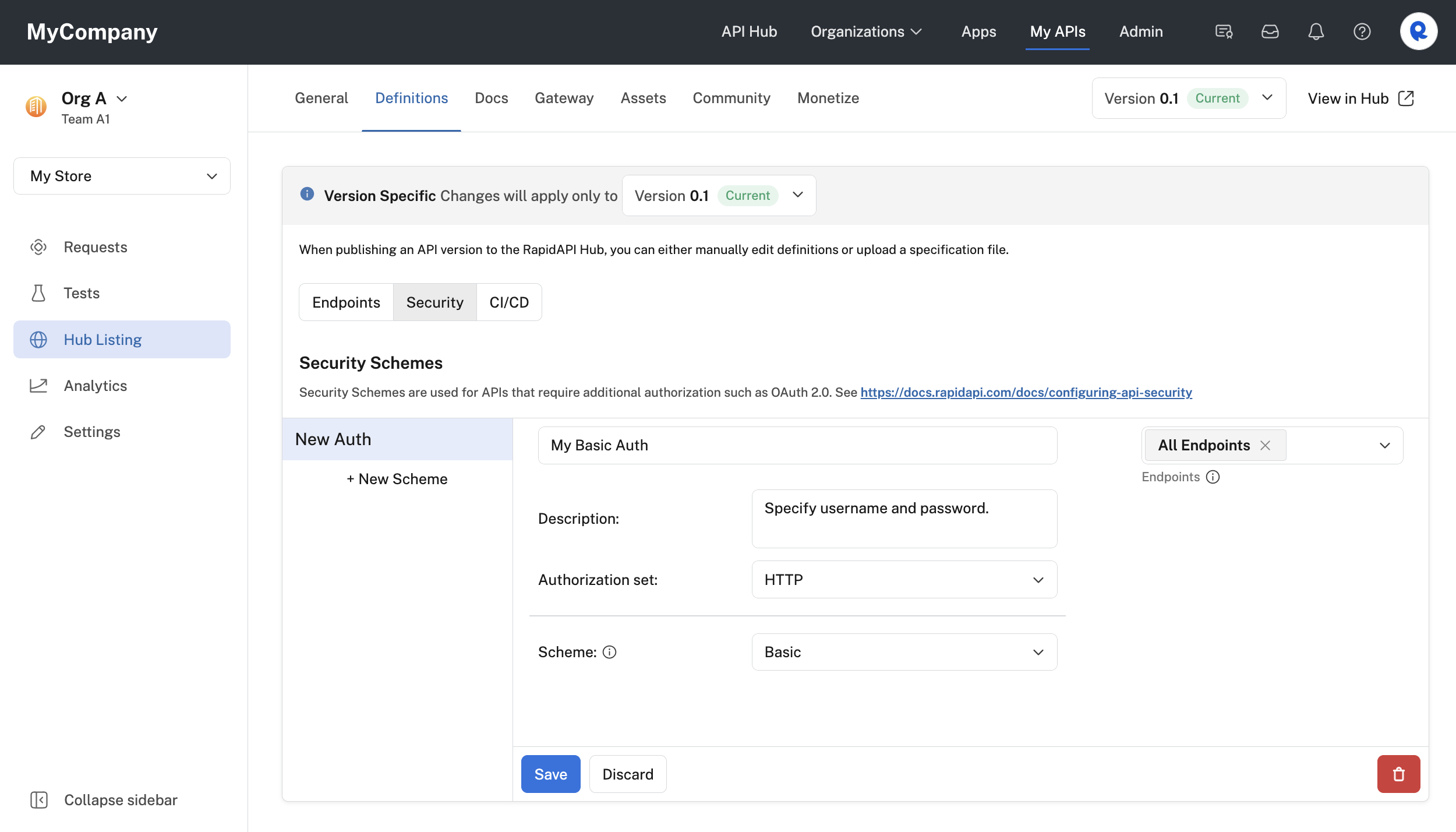
Configuring Api Security This course provides a comprehensive understanding of various authentication mechanisms and protocols used to secure apis. you will learn about the principles of api security, explore different authentication strategies, and understand how to implement them effectively in real world scenarios. Api2:2023 broken authentication authentication mechanisms are often implemented incorrectly, allowing attackers to compromise authentication tokens or to exploit implementation flaws to assume other user’s identities temporarily or permanently. compromising a system’s ability to identify the client user, compromises api security overall.
Comments are closed.