Api Authentication Explained Keys Tokens Oauth
Api Authentication Methods Explained Api Keys Oauth Jwt Hmac Understand api authentication: api keys, oauth 2.0, jwt tokens, basic auth, and bearer tokens. when to use each method, security trade offs, and implementation examples. Learn how api authentication works in practice, from basic auth and api keys to bearer tokens and oauth 2.0, and when to use each method in your apis.

Api Keys Vs Oauth Discover Best Practices To Secure Your Apis Api authentication is how you prove your identity when making api requests. this beginner friendly guide explains different authentication methods, when to use each, and how to implement them. According to workos, oauth 2.0 is a framework that provides a structured approach to token based authorization, often paired with oidc for identity. it's the "gold standard" because it separates the person who owns the data from the app trying to use it. A beginner friendly guide to api authentication. learn oauth flows, jwt tokens, scopes, and claims used to secure modern apis. Understand when to use api keys, oauth tokens, and jwt for different api types. learn about their security implications and how they impact user experience.
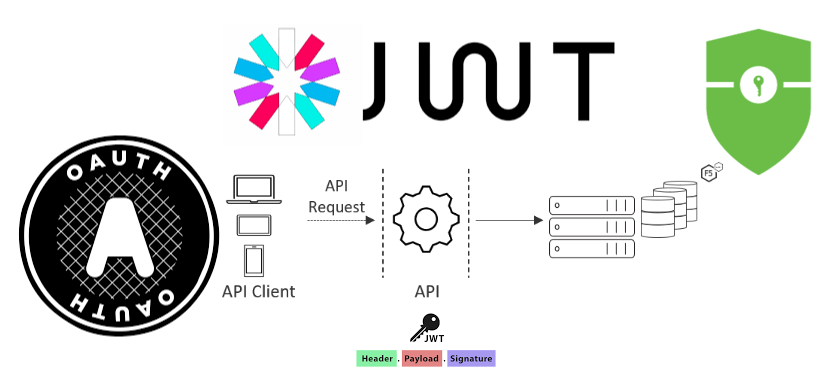
Api Authentication Demystified Mastering Oauth Api Keys And Jwt Like A beginner friendly guide to api authentication. learn oauth flows, jwt tokens, scopes, and claims used to secure modern apis. Understand when to use api keys, oauth tokens, and jwt for different api types. learn about their security implications and how they impact user experience. This article provides an overview of api authentication methods, explaining how tokens, api keys, and oauth work and when to use them. understanding these methods helps developers secure their apis effectively and choose the right approach for different application needs. In this comprehensive guide, we’ll explore the four most common api authentication methods: basic authentication, api keys, hmac (hash based message authentication code), and jwt with oauth 2.0. This article will take you through the api authentication approaches, such as oauth 2.0, api keys, jwt (json web tokens), basic authentication, tls authentication, and openid connect (oidc). 🔑 api authentication explained: api keys, jwt, and oauth (without the boring jargon) have you ever wondered how websites and apps confirm that it is really you, and not some random.
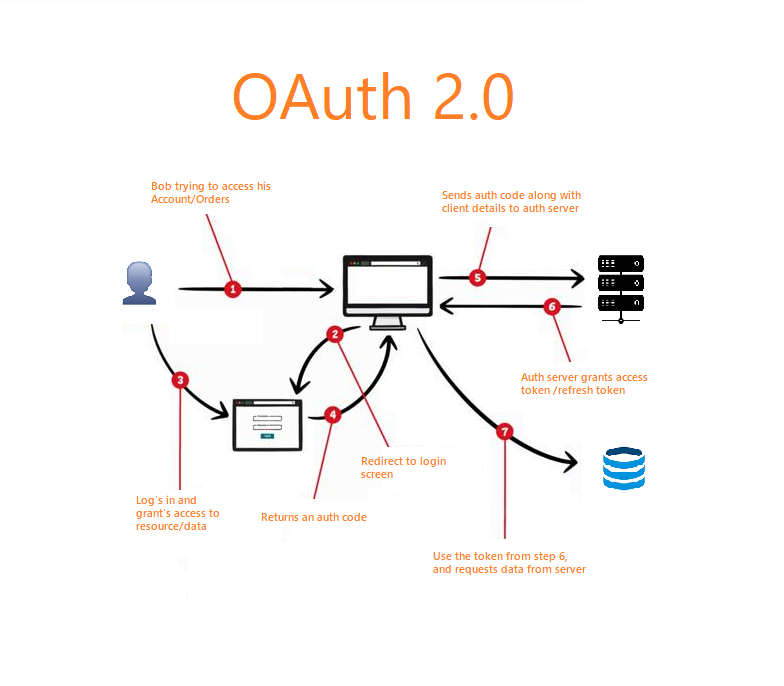
Api Authentication Demystified Mastering Oauth Api Keys And Jwt Like This article provides an overview of api authentication methods, explaining how tokens, api keys, and oauth work and when to use them. understanding these methods helps developers secure their apis effectively and choose the right approach for different application needs. In this comprehensive guide, we’ll explore the four most common api authentication methods: basic authentication, api keys, hmac (hash based message authentication code), and jwt with oauth 2.0. This article will take you through the api authentication approaches, such as oauth 2.0, api keys, jwt (json web tokens), basic authentication, tls authentication, and openid connect (oidc). 🔑 api authentication explained: api keys, jwt, and oauth (without the boring jargon) have you ever wondered how websites and apps confirm that it is really you, and not some random.
Comments are closed.