Android Root Detection Ssl Pinning Bypass Using Frida Complete Frida Setup Tutorial 2025
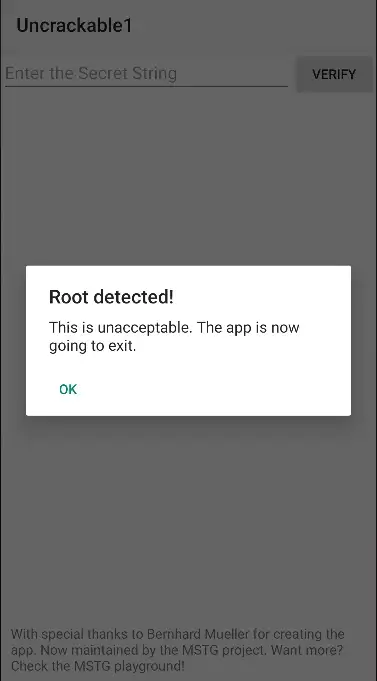
Android Root Detection Bypass Using Frida 1 Pentest Limited It blocks suspicious behavior like file existence checks and shell command execution, helping evade detection in apps using both standard and advanced root checks. This page provides a practical workflow to regain dynamic analysis against android apps that detect root‑block instrumentation or enforce tls pinning. it focuses on fast triage, common detections, and copy‑pasteable hooks tactics to bypass them without repacking when possible.

Android Root Detection Bypass Using Frida 1 Pentest Limited This snippet intercepts java crypto api in android application, prints a symmetric key, algorithm spec, and a plain data right before the final encryption (as well as a cipher data right before the decryption). In this video, we will learn how to bypass android root detection and ssl pinning using frida step by step. By following these steps, you can bypass ssl pinning in a target application, allowing you to inspect and manipulate https traffic during security testing. this method leverages frida’s powerful dynamic instrumentation capabilities and the shared script from frida codeshare to simplify the process. Learn how to intercept and analyze https traffic from android apps using frida, even when they use ssl pinning. as an android security researcher or penetration tester, you’ve probably.
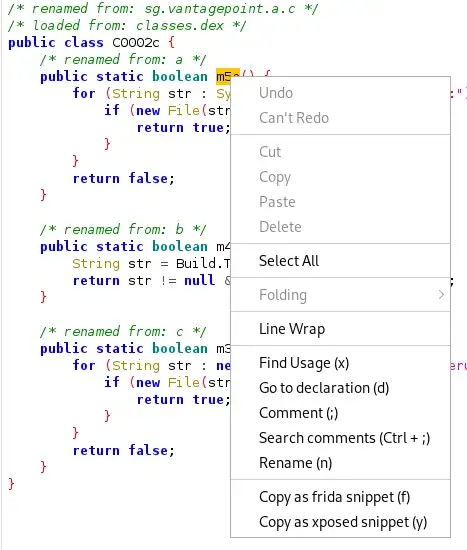
Android Root Detection Bypass Using Frida 1 Pentest Limited By following these steps, you can bypass ssl pinning in a target application, allowing you to inspect and manipulate https traffic during security testing. this method leverages frida’s powerful dynamic instrumentation capabilities and the shared script from frida codeshare to simplify the process. Learn how to intercept and analyze https traffic from android apps using frida, even when they use ssl pinning. as an android security researcher or penetration tester, you’ve probably. This guide walks through the complete process of bypassing ssl pinning on android using frida, one of the most powerful dynamic instrumentation toolkits available. In this blog, we will discuss our recent experience in bypassing ssl certificate pinning on a finance sector mobile application. the blog focuses on the bypass technique used on the android platform. The lab setup instructions cover the installation of python and frida tools, the configuration of the nox emulator with a proxy, and the installation of a ca certificate. the article also provides a step by step guide on using frida to bypass root detection, complete with commands and screenshots. This documentation provides detailed instructions for setting up and using frida to bypass root detection and certificate pinning on an android emulator. it includes steps for installing necessary tools, configuring the environment, and running specific commands to test and bypass security mechanisms in mobile applications.
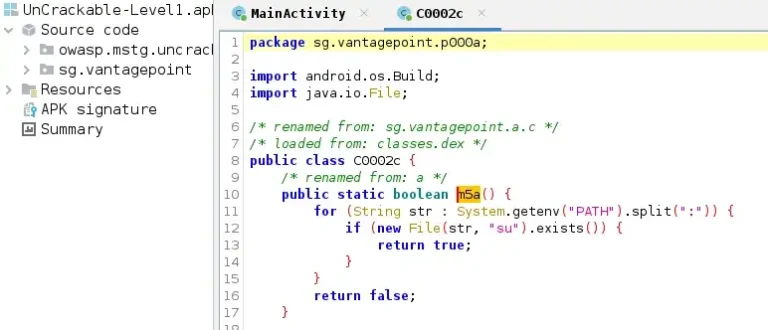
Android Root Detection Bypass Using Frida 1 Pentest Limited This guide walks through the complete process of bypassing ssl pinning on android using frida, one of the most powerful dynamic instrumentation toolkits available. In this blog, we will discuss our recent experience in bypassing ssl certificate pinning on a finance sector mobile application. the blog focuses on the bypass technique used on the android platform. The lab setup instructions cover the installation of python and frida tools, the configuration of the nox emulator with a proxy, and the installation of a ca certificate. the article also provides a step by step guide on using frida to bypass root detection, complete with commands and screenshots. This documentation provides detailed instructions for setting up and using frida to bypass root detection and certificate pinning on an android emulator. it includes steps for installing necessary tools, configuring the environment, and running specific commands to test and bypass security mechanisms in mobile applications.

Android Root Detection Bypass Using Frida 1 Pentest Limited The lab setup instructions cover the installation of python and frida tools, the configuration of the nox emulator with a proxy, and the installation of a ca certificate. the article also provides a step by step guide on using frida to bypass root detection, complete with commands and screenshots. This documentation provides detailed instructions for setting up and using frida to bypass root detection and certificate pinning on an android emulator. it includes steps for installing necessary tools, configuring the environment, and running specific commands to test and bypass security mechanisms in mobile applications.
Comments are closed.