Android Root Detection Ssl Pinning Bypass Using Frida

Android Root Detection Bypass Using Frida 1 Pentest Limited Learn how to bypass ssl pinning on android apps using frida with step by step commands, real world techniques, and expert insights for penetration testers and security researchers. This snippet intercepts java crypto api in android application, prints a symmetric key, algorithm spec, and a plain data right before the final encryption (as well as a cipher data right before the decryption).

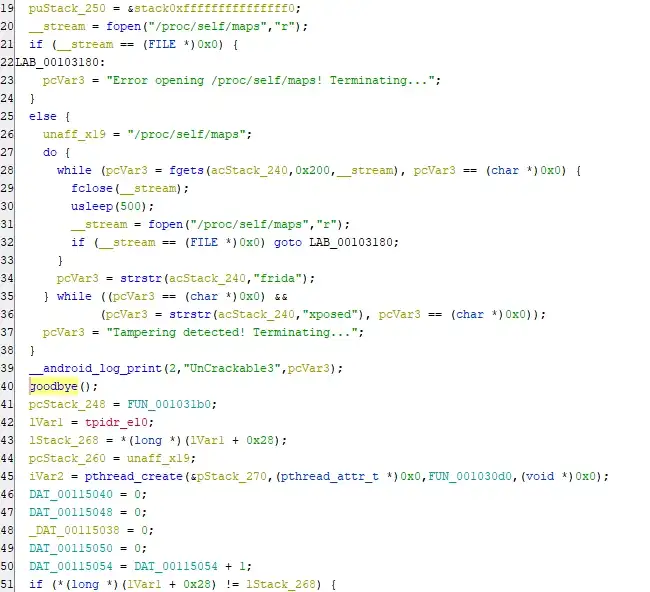
Android Root Detection Bypass Using Frida 3 Pentest This page provides a practical workflow to regain dynamic analysis against android apps that detect root‑block instrumentation or enforce tls pinning. it focuses on fast triage, common detections, and copy‑pasteable hooks tactics to bypass them without repacking when possible. Android universal anti bypass framework root, ssl pinning, emulator & debug detection bypass okankurtuluss fridabypasskit. Learn how to intercept and analyze https traffic from android apps using frida, even when they use ssl pinning. as an android security researcher or penetration tester, you’ve probably. By following these steps, you can bypass ssl pinning in a target application, allowing you to inspect and manipulate https traffic during security testing. this method leverages frida’s powerful dynamic instrumentation capabilities and the shared script from frida codeshare to simplify the process.

Android Root Detection Bypass Using Frida 3 Pentest Learn how to intercept and analyze https traffic from android apps using frida, even when they use ssl pinning. as an android security researcher or penetration tester, you’ve probably. By following these steps, you can bypass ssl pinning in a target application, allowing you to inspect and manipulate https traffic during security testing. this method leverages frida’s powerful dynamic instrumentation capabilities and the shared script from frida codeshare to simplify the process. This documentation provides detailed instructions for setting up and using frida to bypass root detection and certificate pinning on an android emulator. it includes steps for installing necessary tools, configuring the environment, and running specific commands to test and bypass security mechanisms in mobile applications. Learn how to bypass root detection using frida tools and objection and perform various android pentesting tasks such as data storage check. There are a lot of different things that you can do with frida, but one of the most common uses for frida is to bypass ssl pinning. this can be done for both android and ios applications, but i’m just going to go over how to do it with an android device in this blog post. When performing mobile application penetration testing, one of the most common obstacles is ssl pinning. even after installing burp’s certificate, traffic still doesn’t appear – because the application explicitly validates the server certificate.
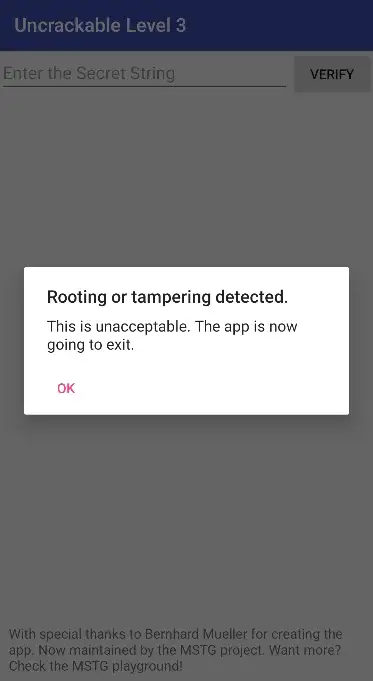
Android Root Detection Bypass Using Frida 3 Pentest This documentation provides detailed instructions for setting up and using frida to bypass root detection and certificate pinning on an android emulator. it includes steps for installing necessary tools, configuring the environment, and running specific commands to test and bypass security mechanisms in mobile applications. Learn how to bypass root detection using frida tools and objection and perform various android pentesting tasks such as data storage check. There are a lot of different things that you can do with frida, but one of the most common uses for frida is to bypass ssl pinning. this can be done for both android and ios applications, but i’m just going to go over how to do it with an android device in this blog post. When performing mobile application penetration testing, one of the most common obstacles is ssl pinning. even after installing burp’s certificate, traffic still doesn’t appear – because the application explicitly validates the server certificate.
Android Root Detection Bypass Using Frida 3 Pentest There are a lot of different things that you can do with frida, but one of the most common uses for frida is to bypass ssl pinning. this can be done for both android and ios applications, but i’m just going to go over how to do it with an android device in this blog post. When performing mobile application penetration testing, one of the most common obstacles is ssl pinning. even after installing burp’s certificate, traffic still doesn’t appear – because the application explicitly validates the server certificate.
Comments are closed.