Android Ransomware Attack Ethicalhackingtutorial Cybersecurity
Techvansh Android Hacking Course Do you want to learn ethical hacking techniques to test and secure android applications? welcome to the ultimate android hacking & security course, designed by whitesec cybersecurity consultancy for beginners who want to explore the world of ethical hacking. Sara (simple android ransomware attack) is an educational security research tool designed to demonstrate android malware creation techniques. this tool allows security researchers and students to understand how android trojans and ransomware operate.

Android Ransomware Attack Download Scientific Diagram Android malware analysis is a critical aspect of cybersecurity focused on understanding, identifying, and mitigating malicious software specifically designed for android operating systems. In this video, we break down how android ransomware works step by step, how attackers disguise it as a legitimate app, how lock screen ransomware activates instantly, and—most importantly—how. Start with basic concepts of cybersecurity, including ethical hacking principles, security models, cryptography, and networking fundamentals required to understand how systems are protected from cyber threats. You’ll also gain practical knowledge of key security tools and protocols, positioning yourself for roles in cybersecurity and mobile security. in this course, you’ll learn about android os architecture, the android debug bridge, and how to perform ethical hacking on mobile platforms.
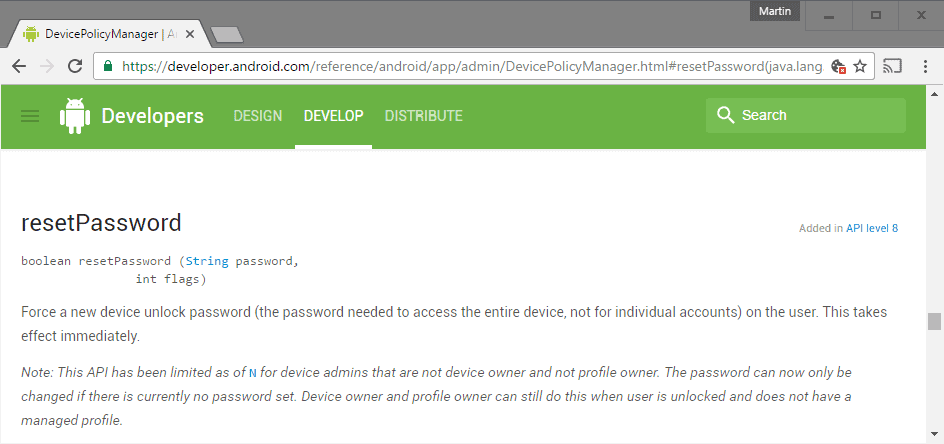
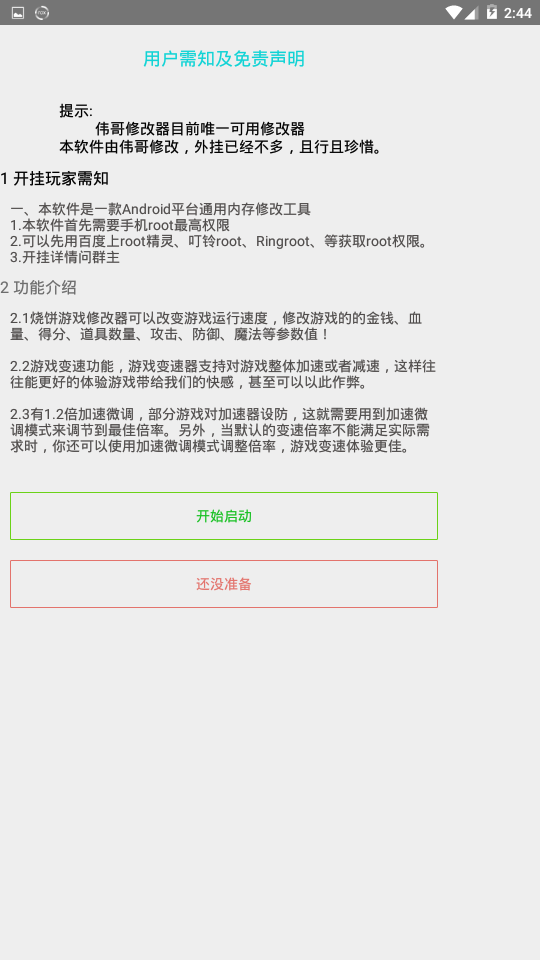
Android N Plugs One Ransomware Attack Vector Ghacks Tech News Start with basic concepts of cybersecurity, including ethical hacking principles, security models, cryptography, and networking fundamentals required to understand how systems are protected from cyber threats. You’ll also gain practical knowledge of key security tools and protocols, positioning yourself for roles in cybersecurity and mobile security. in this course, you’ll learn about android os architecture, the android debug bridge, and how to perform ethical hacking on mobile platforms. This course is perfect for cybersecurity enthusiasts, penetration testers, and ethical hackers who want to understand android vulnerabilities, test security loopholes, and learn real world attack techniques used by hackers. This research sets a new benchmark for android ransomware detection, offering a robust, scalable, and highly accurate solution that enhances the security and resilience of mobile networks against evolving cyber threats. We're going to transform your android device into a pocket sized security powerhouse! by the end of this guide, you'll have a solid foundation and be well on your way to exploring the world of ethical hacking. "i tested malware against smartphones | android ransomware explained" in this step by step ethical hacking tutorial, i’ll show you how hackers create android ransomware using sara.
Github Fullpenetrationtesting Android Ransomware пёџa High Speed This course is perfect for cybersecurity enthusiasts, penetration testers, and ethical hackers who want to understand android vulnerabilities, test security loopholes, and learn real world attack techniques used by hackers. This research sets a new benchmark for android ransomware detection, offering a robust, scalable, and highly accurate solution that enhances the security and resilience of mobile networks against evolving cyber threats. We're going to transform your android device into a pocket sized security powerhouse! by the end of this guide, you'll have a solid foundation and be well on your way to exploring the world of ethical hacking. "i tested malware against smartphones | android ransomware explained" in this step by step ethical hacking tutorial, i’ll show you how hackers create android ransomware using sara.
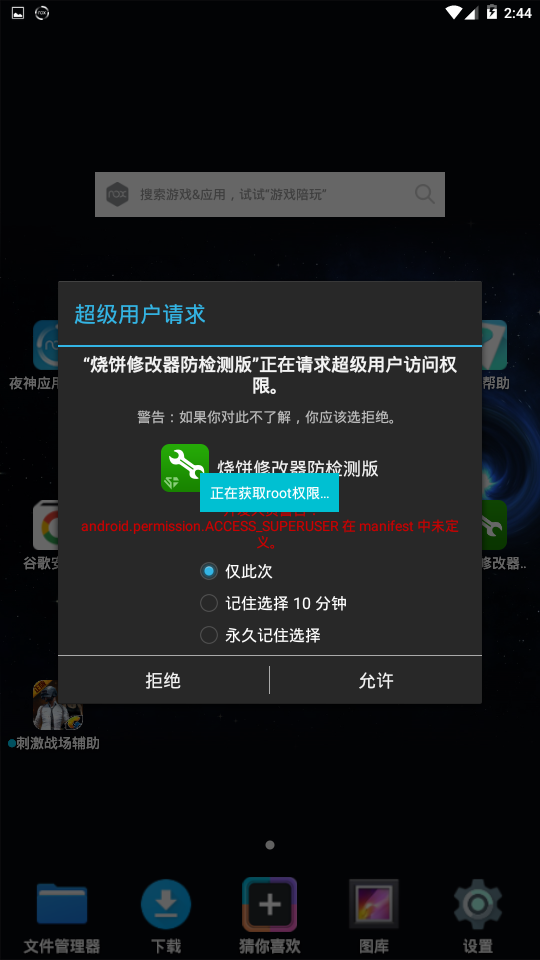
Android Ransomware Research We're going to transform your android device into a pocket sized security powerhouse! by the end of this guide, you'll have a solid foundation and be well on your way to exploring the world of ethical hacking. "i tested malware against smartphones | android ransomware explained" in this step by step ethical hacking tutorial, i’ll show you how hackers create android ransomware using sara.
Android Ransomware Research
Comments are closed.