Android Pen Testing Malware Analysis Static
Android App Pentesting Static Analysis Pentestguy Mobsf can be used for a variety of use cases such as mobile application security, penetration testing, malware analysis, and privacy analysis. the static analyzer supports popular mobile app binaries like apk, ipa, appx and source code. Mobile security framework (mobsf) is an intelligent, all in one open source mobile application (android ios windows) automated pen testing framework capable of performing static and dynamic analysis.

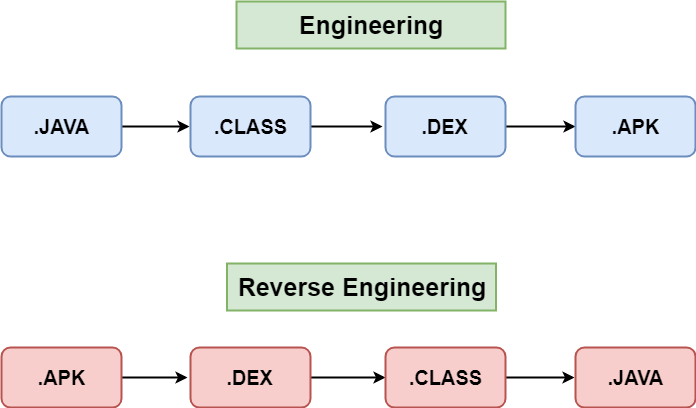
Android Malware Detection Using Static Analysis Download Scientific Android pentesting has become an important process to identify vulnerabilities within android applications. in this article, i will discuss the tools used for static mobile pentest. In this post, we are going to see some of the popular tools which help in static testing and how to use it in android application security testing (static testing). Mobsf can be used for a variety of use cases such as mobile application security, penetration testing, malware analysis, and privacy analysis. the static analyzer supports popular mobile app binaries like apk, ipa, appx and source code. Static analysis is a technique used to examine and evaluate the source code of a mobile application without executing it. this method is instrumental in identifying potential security vulnerabilities, coding errors, and compliance issues.

Android Malware Static Analysis Tools And Support Download Scientific Mobsf can be used for a variety of use cases such as mobile application security, penetration testing, malware analysis, and privacy analysis. the static analyzer supports popular mobile app binaries like apk, ipa, appx and source code. Static analysis is a technique used to examine and evaluate the source code of a mobile application without executing it. this method is instrumental in identifying potential security vulnerabilities, coding errors, and compliance issues. We analyze feature extraction techniques across static, dynamic, hybrid, and graph based methods, highlighting their respective trade offs. Mobile security framework (mobsf) is an automated, all in one mobile application (android ios windows) pen testing, malware analysis and security assessment framework capable of performing static and dynamic analysis. The goal of this research is to examine the effectiveness of static analysis to detect android malware by using permission based features. this study proposes machine learning with different sets of classifiers was used to evaluate android malware detection. It provides robust tools for static and dynamic analysis, allowing security professionals to perform penetration testing, malware detection, privacy analysis, and runtime monitoring.
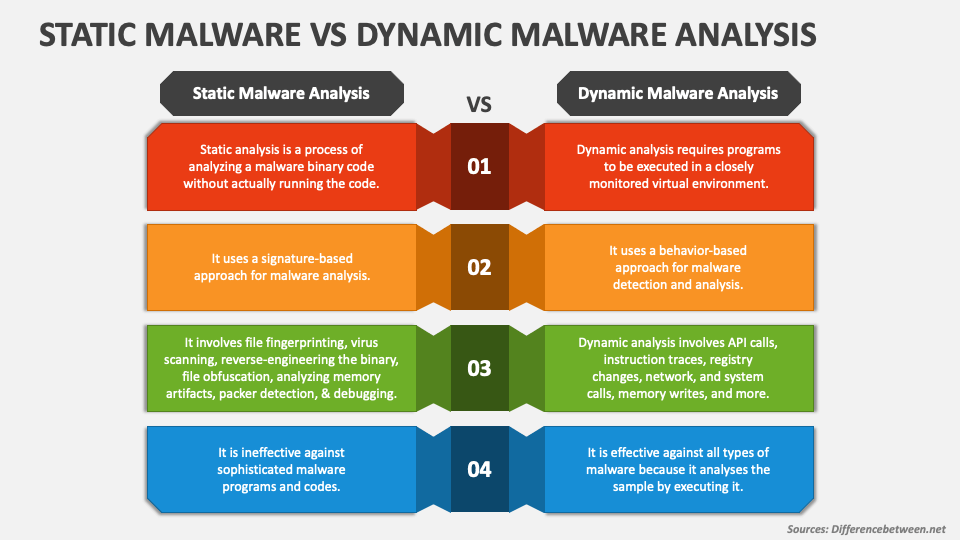
Static Malware Vs Dynamic Malware Analysis Powerpoint Presentation We analyze feature extraction techniques across static, dynamic, hybrid, and graph based methods, highlighting their respective trade offs. Mobile security framework (mobsf) is an automated, all in one mobile application (android ios windows) pen testing, malware analysis and security assessment framework capable of performing static and dynamic analysis. The goal of this research is to examine the effectiveness of static analysis to detect android malware by using permission based features. this study proposes machine learning with different sets of classifiers was used to evaluate android malware detection. It provides robust tools for static and dynamic analysis, allowing security professionals to perform penetration testing, malware detection, privacy analysis, and runtime monitoring.
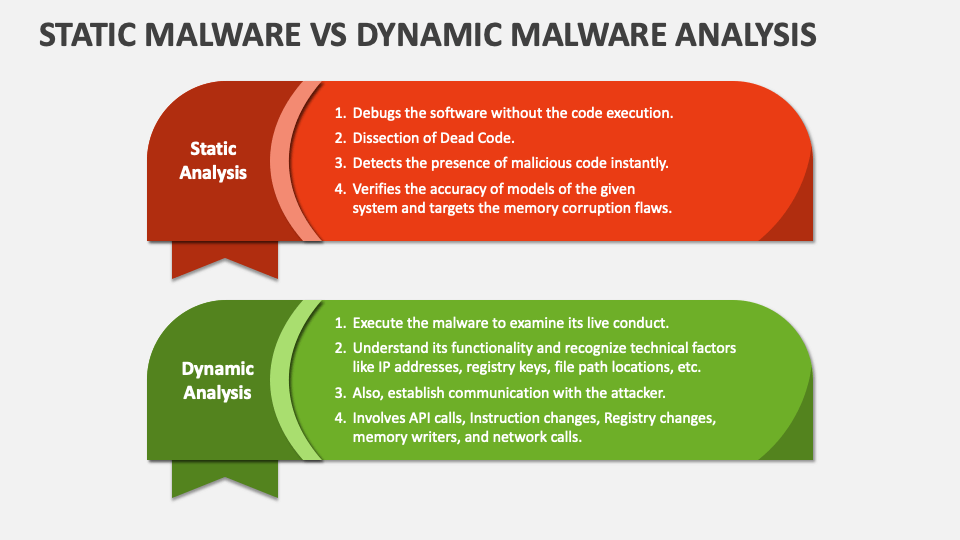
Static Malware Vs Dynamic Malware Analysis Powerpoint Presentation The goal of this research is to examine the effectiveness of static analysis to detect android malware by using permission based features. this study proposes machine learning with different sets of classifiers was used to evaluate android malware detection. It provides robust tools for static and dynamic analysis, allowing security professionals to perform penetration testing, malware detection, privacy analysis, and runtime monitoring.
Comments are closed.