Android And Its Architecture Android Malware Analysis

Android Malware Detection Based On Image Analysis Pdf Artificial This systematic literature review examines cutting edge approaches to android malware analysis, with implications for securing resource constrained environments. This systematic literature review (slr) examines cutting edge approaches to android malware analysis with direct im plications for securing iot infrastructures.

Android Malware Analysis Pdf Objective: this literature review aims to provide a comprehensive overview of android malware analysis techniques and methodologies, evaluating the effectiveness of different approaches like static, dynamic, machine learning and deep learning. In this paper, we review the android components to propose a threat model that illustrates the possible threats that are present in the android. we also present the attack taxonomy to. In the domain of android malware detection, many researchers use a hybrid analysis framework that combines both static and dynamic analysis methods. this approach typically involves designing a detection system with two layers: a static layer and a dynamic layer. Android malware analysis involves examining and understanding malware behaviour and its characteristics. it also includes potential adversarial impacts on android devices. this paper presents a quick understanding and a holistic view of malware detection and analysis.
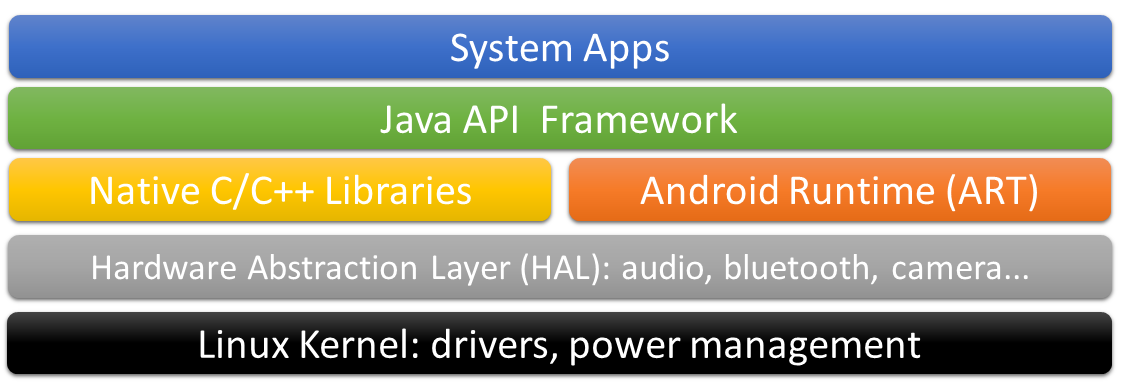
Android Malware Architecture Download Scientific Diagram In the domain of android malware detection, many researchers use a hybrid analysis framework that combines both static and dynamic analysis methods. this approach typically involves designing a detection system with two layers: a static layer and a dynamic layer. Android malware analysis involves examining and understanding malware behaviour and its characteristics. it also includes potential adversarial impacts on android devices. this paper presents a quick understanding and a holistic view of malware detection and analysis. This paper offers a comprehensive analysis model for android malware. the model presents the essential factors affecting the analysis results of android malware that are vision based. This article presents a comprehensive survey on leading android malware analysis and detection techniques, and their effectiveness against evolving malware. this article categorizes systems by methodology and date to evaluate progression and weaknesses. In this paper, the android components have been reviewed to propose a threat model that illustrates the possible threats that are present in the android. the researchers also present the attack taxonomy to illustrate the possible attacks at various layers of the android architecture. Malware from android devices. these engines use a variety of techniques to identify and neutralize malware threats, such as signature based scanning, behavioral analysis, and machine learning.

Android Malware Analysis Pptx This paper offers a comprehensive analysis model for android malware. the model presents the essential factors affecting the analysis results of android malware that are vision based. This article presents a comprehensive survey on leading android malware analysis and detection techniques, and their effectiveness against evolving malware. this article categorizes systems by methodology and date to evaluate progression and weaknesses. In this paper, the android components have been reviewed to propose a threat model that illustrates the possible threats that are present in the android. the researchers also present the attack taxonomy to illustrate the possible attacks at various layers of the android architecture. Malware from android devices. these engines use a variety of techniques to identify and neutralize malware threats, such as signature based scanning, behavioral analysis, and machine learning.

Pdf Android Application Malware Analysis In this paper, the android components have been reviewed to propose a threat model that illustrates the possible threats that are present in the android. the researchers also present the attack taxonomy to illustrate the possible attacks at various layers of the android architecture. Malware from android devices. these engines use a variety of techniques to identify and neutralize malware threats, such as signature based scanning, behavioral analysis, and machine learning.
Android Malware Ii Android Basics Layakk
Comments are closed.