An Overview Of The Proposed Threat Model Download Scientific Diagram
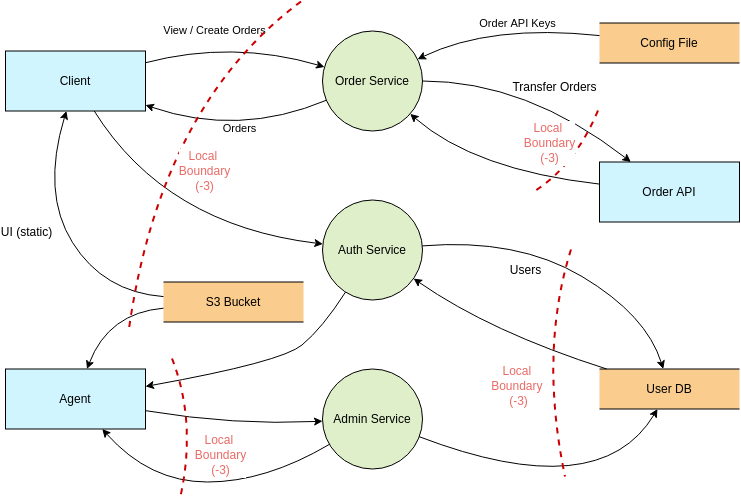
Threat Modeling Threat Model Diagram Template Figure 1 presents an overview of our proposed threat model. as shown in figure 1, our proposed threat model assumes that an attacker has infected a users' smartphone with a. Making threat modeling a core component of your sdlc can help increase product security. the threat modeling process can be decomposed into four high level steps. frequently, each step is documented as it is carried out. the resulting document is the threat model for the application.
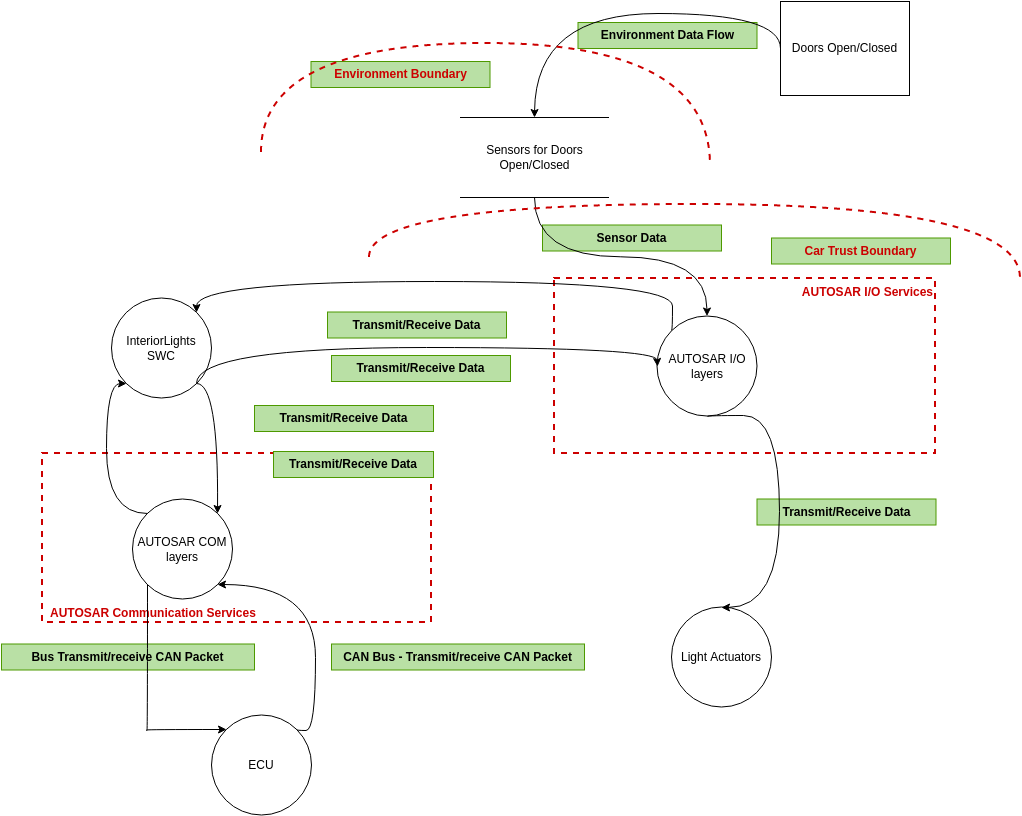
Threat Modeling Threat Model Diagram Template A new framework approach to securing smd is proposed to ensure that users have strong protection over their data within smd. An overview of the threat analysis method using the vulnerability db is shown in figure 1. the proposed threat analysis method conducts the following three procedures: •. We design two schemes using the proposed models to address identity disclosure and attribute disclosure problems in publishing healthcare data. We propose a threat analysis method utilizing topic model analysis and vulnerability databases. the method is based on attack tree analysis.

Threat Model Diagram Elements Download Scientific Diagram We design two schemes using the proposed models to address identity disclosure and attribute disclosure problems in publishing healthcare data. We propose a threat analysis method utilizing topic model analysis and vulnerability databases. the method is based on attack tree analysis. Threat modeling is a critical step in understanding which assets are most likely to be targeted in a cloud environment and the vulnerabilities that are present. the direction of attack is represented from source to target machine in a proposed threat model. Threat modeling is the process of finding threats to a system, evaluating the risk associated with each threat, selecting mitigations to counteract each threat. In this context, a tool to perform systematic analysis of threat modeling for cps is proposed. a real world wireless railway temperature monitoring system is used as a case study to validate the proposed approach. This document provides guidance on conducting cyber threat modelling. it discusses the importance of threat modelling for prioritizing risks and focuses on a system level approach to threat modelling.
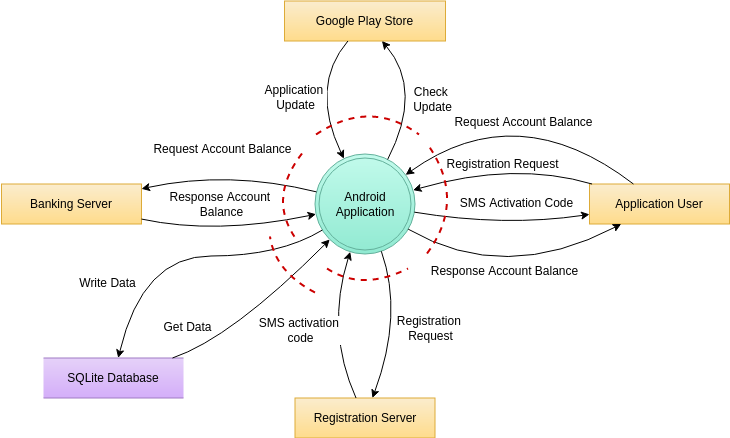
Website Threat Modeling Threat Model Diagram Template Threat modeling is a critical step in understanding which assets are most likely to be targeted in a cloud environment and the vulnerabilities that are present. the direction of attack is represented from source to target machine in a proposed threat model. Threat modeling is the process of finding threats to a system, evaluating the risk associated with each threat, selecting mitigations to counteract each threat. In this context, a tool to perform systematic analysis of threat modeling for cps is proposed. a real world wireless railway temperature monitoring system is used as a case study to validate the proposed approach. This document provides guidance on conducting cyber threat modelling. it discusses the importance of threat modelling for prioritizing risks and focuses on a system level approach to threat modelling.
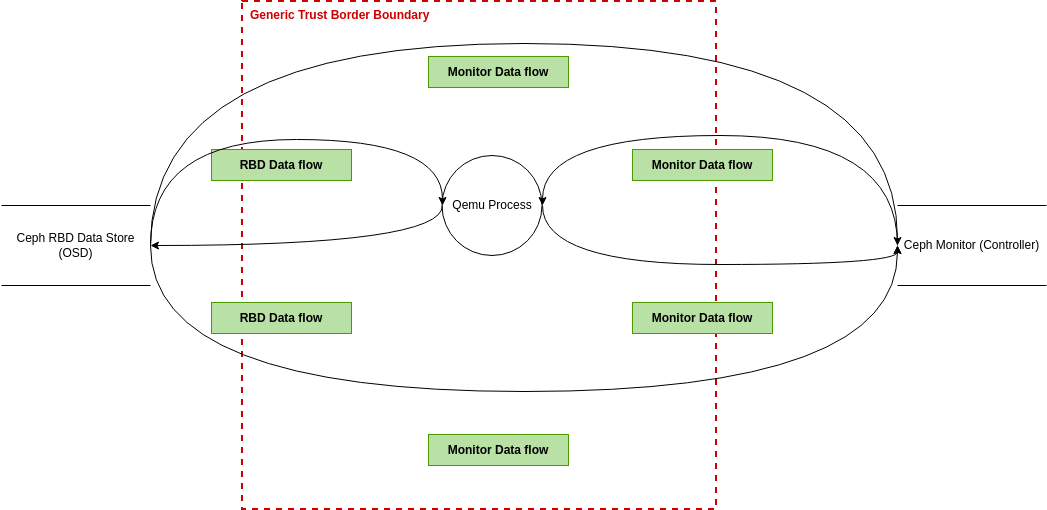
Website Threat Modeling Threat Model Diagram Template In this context, a tool to perform systematic analysis of threat modeling for cps is proposed. a real world wireless railway temperature monitoring system is used as a case study to validate the proposed approach. This document provides guidance on conducting cyber threat modelling. it discusses the importance of threat modelling for prioritizing risks and focuses on a system level approach to threat modelling.
Comments are closed.