An Introduction To Rbac Abac Rebac In 6 Minutes
Rbac Vs Rebac Vs Abac A Beginner S Guide If you’ve ever worked with software that needs to keep things secure and organized, you’ve probably heard of access control systems. here's a quick explainer on the different types of access. In this article, we will compare three access control models—rbac, abac, and rebac—by looking at practical policy examples from actual products (aws iam, kubernetes, cedar, openfga, and spicedb).
Rbac Vs Rebac Vs Abac A Beginner S Guide Rbac, rebac, and abac each offer distinct advantages and limitations. selecting the right access control model depends on organizational needs, security requirements, and the complexity of access scenarios. Rbac alone is not enough. so, is abac the answer? or rebac, which we hear a lot about lately? what exactly is the difference? in this article, we will compare three access control modelsrbac, abac, and rebacby looking at practical policy examples from actual products (aws iam, kubernetes, cedar, openfga, and spicedb). But before diving into practice, let’s review theory and discuss the main authorization models: ibac, rbac, pbac, abac, rebac, acl, dac, and mac. Rbac ? abac !? rebac ?!?!? if these terms are unfamiliar to you, check out this 5 minute explainer video by sohan on different types of access control systems.
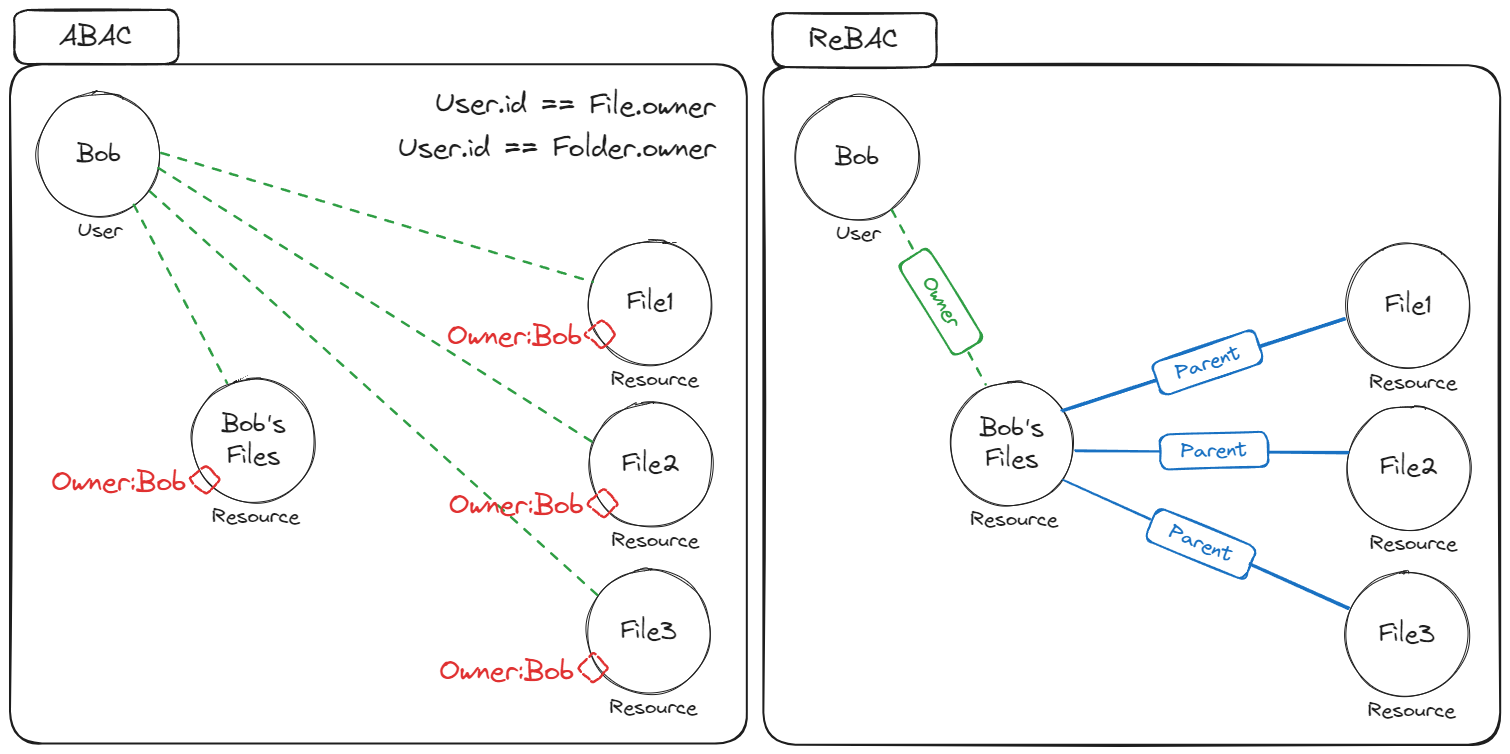
Rbac Vs Rebac Vs Abac A Beginner S Guide But before diving into practice, let’s review theory and discuss the main authorization models: ibac, rbac, pbac, abac, rebac, acl, dac, and mac. Rbac ? abac !? rebac ?!?!? if these terms are unfamiliar to you, check out this 5 minute explainer video by sohan on different types of access control systems. Summary: this article presents an overview of rbac vs. abac, plus several additional models of access control, including pbac, acl, and dac. you will learn what these methods are, how they differ from each other, and the pros and cons of each. While it is possible to model some of these relationships using rbac and abac, rebac allows us to do so more concisely and so it makes it easier to reason about the authorization model. Master rbac, abac, and rebac with practical typescript examples showing how to implement each permission system. Discuss two methods of permission management: acl and rbac, explain their operating principles, advantages and disadvantages, and discuss how to choose the appropriate mode to meet the authorization needs of the system.
Rbac Vs Rebac Vs Abac A Beginner S Guide Summary: this article presents an overview of rbac vs. abac, plus several additional models of access control, including pbac, acl, and dac. you will learn what these methods are, how they differ from each other, and the pros and cons of each. While it is possible to model some of these relationships using rbac and abac, rebac allows us to do so more concisely and so it makes it easier to reason about the authorization model. Master rbac, abac, and rebac with practical typescript examples showing how to implement each permission system. Discuss two methods of permission management: acl and rbac, explain their operating principles, advantages and disadvantages, and discuss how to choose the appropriate mode to meet the authorization needs of the system.
Authorization Policy Showdown Rbac Vs Abac Vs Rebac Master rbac, abac, and rebac with practical typescript examples showing how to implement each permission system. Discuss two methods of permission management: acl and rbac, explain their operating principles, advantages and disadvantages, and discuss how to choose the appropriate mode to meet the authorization needs of the system.
Comments are closed.