Allow For Unauthenticated Requests Issue 396 Actions Github Script
Allow For Unauthenticated Requests Issue 396 Actions Github Script Generally speaking, i don't think we should encourage unauthenticated requests. they're subjected to a lower rate limit based on the ip address that you'd likely hit fairly quickly. By the end of this article, you'll know exactly how to configure github actions permissions correctly, avoid the 3 most dangerous permission traps, and implement a security first approach that actually works in real projects.
Actions Github Script Download Sourceforge Net This answer recommends changing the default permissions for all action workflows to permissive instead of restrictive. from a security standpoint it is highly discouraged to do so. In this github pro tips post we will look at how to manage permissions in github actions workflows. github actions is a powerful tool for automating your ci cd pipelines workflows. When a workflow runs, github gives it a special token called github token. this token acts like a temporary robot user — it can read write to your repo but only if you allow it. However, many users encounter a frustrating roadblock: the "allow github actions to create and approve pull requests" setting in their repository is grayed out, preventing workflows from creating prs. if you’ve faced this issue, you’re not alone.
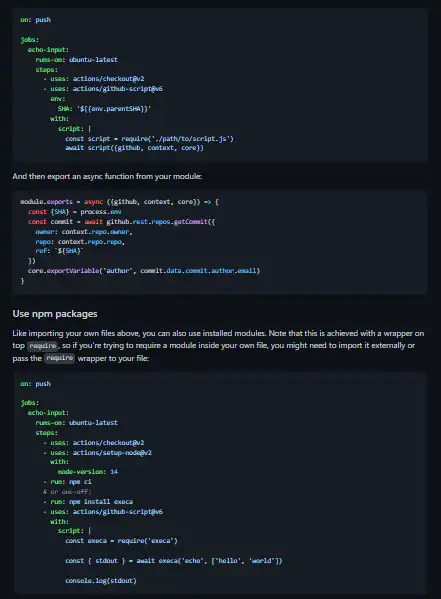
Actions Github Script Download For Windows When a workflow runs, github gives it a special token called github token. this token acts like a temporary robot user — it can read write to your repo but only if you allow it. However, many users encounter a frustrating roadblock: the "allow github actions to create and approve pull requests" setting in their repository is grayed out, preventing workflows from creating prs. if you’ve faced this issue, you’re not alone. Another protection you have against this type of scenario is a setting that lets you determine when github actions are run on code from pull requests. by default, pull requests from first time contributors require approval from a maintainer to start ci tests. In summary, as illustrated in the codeql alert above, we can now identify non obvious sources of untrusted data (for example, git or gh commands or third party actions) and, more importantly, track this untrusted data throughout complex workflows. Getting "resource not accessible by integration" in github actions? fix http 403, graphql createpullrequest, and github token permission errors. step by step with real examples. Let’s dive into practical solutions for these frustrating, yet frequently encountered, github actions errors, equipping you with the knowledge to build robust and reliable automation.
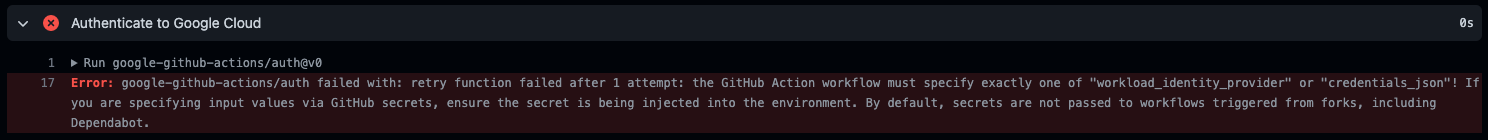
How To Inject Github Secret Into Environment Issue 226 Google Another protection you have against this type of scenario is a setting that lets you determine when github actions are run on code from pull requests. by default, pull requests from first time contributors require approval from a maintainer to start ci tests. In summary, as illustrated in the codeql alert above, we can now identify non obvious sources of untrusted data (for example, git or gh commands or third party actions) and, more importantly, track this untrusted data throughout complex workflows. Getting "resource not accessible by integration" in github actions? fix http 403, graphql createpullrequest, and github token permission errors. step by step with real examples. Let’s dive into practical solutions for these frustrating, yet frequently encountered, github actions errors, equipping you with the knowledge to build robust and reliable automation.
Comments are closed.