Ai Zero Trust Tenet 4 Dynamic Policy Access
Zero Trust Access Policies Policy Based Adaptive Access Ai zero trust – tenet 4: dynamic policy accessdescription:welcome to the fourth tenet of ai zero trust – dynamic policy access.in this episode, we examine ho. Access to resources is determined by dynamic policy including the observable state of client identity, application service, and the requesting asset and may include other behavioral and environmental attributes.

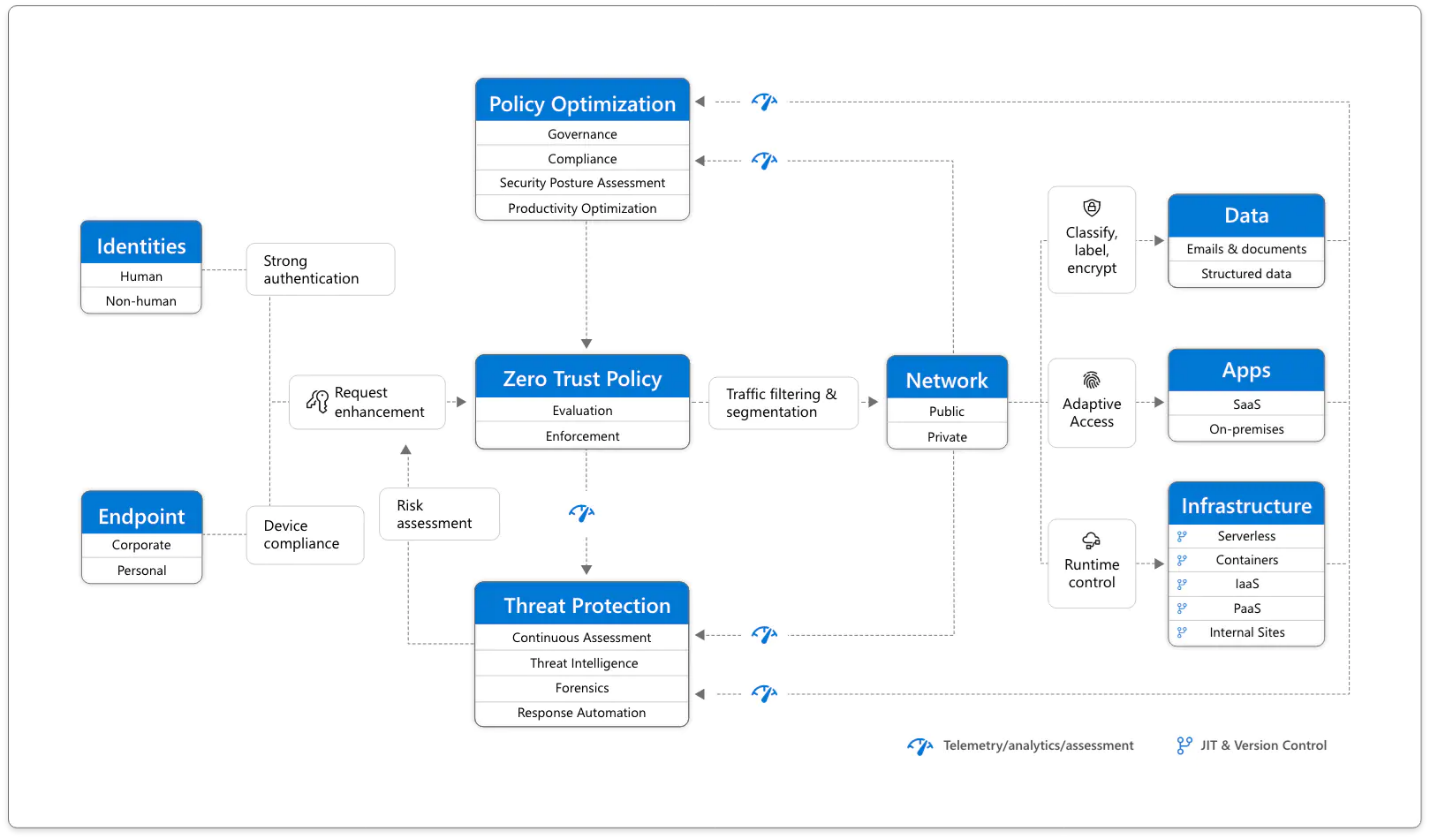
Zero Trust Access Policies Policy Based Adaptive Access Tenet 4: access to resources is determined by dynamic policy. the tenet: "access to resources is determined by dynamic policy—including the observable state of client identity, application service, and the requesting asset—and may include other behavioral and environmental attributes.". The cloud security alliance (csa) is the world’s leading not for profit organization committed to awareness, implementation, and credentialing of ai, cloud, and zero trust. The trust algorithm: dynamic access decision making — central to the nist zero trust architecture is the trust algorithm — the computational process by which the policy engine evaluates access requests and produces authorization decisions. 1. introduction this document is a cross sectoral profile of and companion resource for the ai risk management framework (ai rmf 1.0) for generative ai,1 pursuant to president biden’s executive order (eo) 14110 on safe, secure, and trustworthy artificial intelligence.2 the ai rmf was released in january 2023, and is intended for voluntary use and to improve the ability of organizations to.
Github Gauravghandat 23 Ai Powered Zero Trust Access Control Ai The trust algorithm: dynamic access decision making — central to the nist zero trust architecture is the trust algorithm — the computational process by which the policy engine evaluates access requests and produces authorization decisions. 1. introduction this document is a cross sectoral profile of and companion resource for the ai risk management framework (ai rmf 1.0) for generative ai,1 pursuant to president biden’s executive order (eo) 14110 on safe, secure, and trustworthy artificial intelligence.2 the ai rmf was released in january 2023, and is intended for voluntary use and to improve the ability of organizations to. It examines the benefits, challenges, and future trends, providing a comprehensive guide to leveraging zero trust and ai for fortified cyber defenses. Access to individual enterprise resources is granted on a per session basis. access to resources is determined by dynamic policy—including the observable state of client identity, application service, and the requesting asset—and may include other behavioral and environmental attributes. This paper introduces a novel framework that leverages artificial intelligence (ai) and behavioral fingerprinting to enable continuous and adaptive access evaluation within a zero trust environment. Conclusion: embracing ai driven zero trust the transition toward ai driven zero trust is no longer a choice but a prerequisite for survival in a world of automated threats. by moving beyond static defenses and embracing an ai enabled cybersecurity architecture, businesses can finally achieve the agility and security required for the modern era.
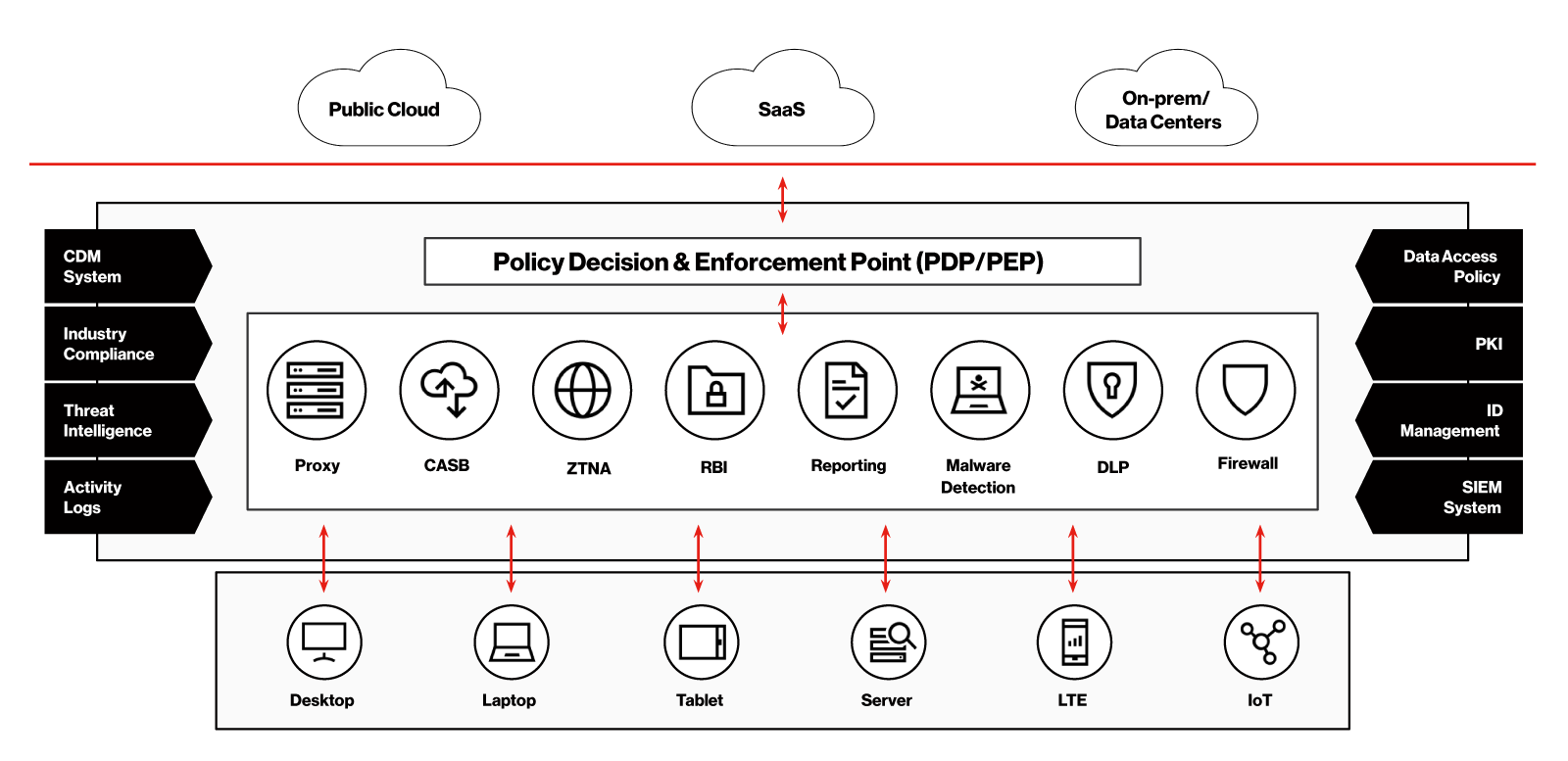
Zero Trust Dynamic Network Access Solutions Verizon It examines the benefits, challenges, and future trends, providing a comprehensive guide to leveraging zero trust and ai for fortified cyber defenses. Access to individual enterprise resources is granted on a per session basis. access to resources is determined by dynamic policy—including the observable state of client identity, application service, and the requesting asset—and may include other behavioral and environmental attributes. This paper introduces a novel framework that leverages artificial intelligence (ai) and behavioral fingerprinting to enable continuous and adaptive access evaluation within a zero trust environment. Conclusion: embracing ai driven zero trust the transition toward ai driven zero trust is no longer a choice but a prerequisite for survival in a world of automated threats. by moving beyond static defenses and embracing an ai enabled cybersecurity architecture, businesses can finally achieve the agility and security required for the modern era.
Comments are closed.