Affine Ciphers Part One
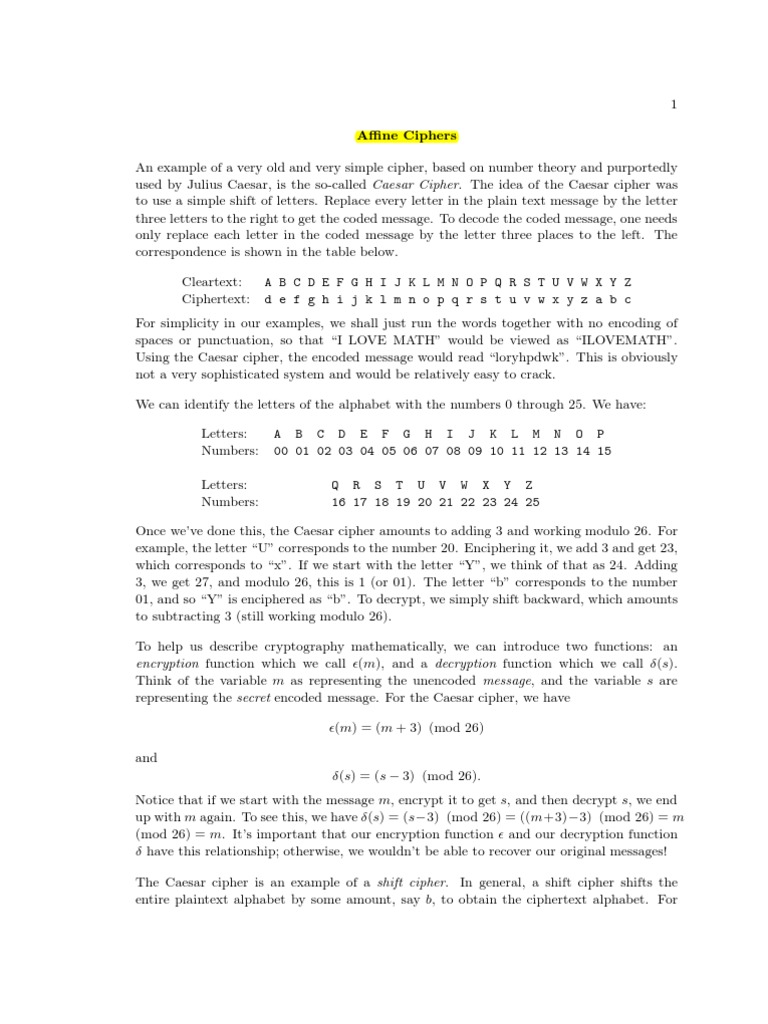
Affine Ciphers Pdf Cipher Cryptography Deep dive into the affine cipher: how it works, valid keys, modular inverses, encoding decoding, frequency analysis, and cracking methods. In this part (part 1), an introduction and principles of the encryption process using affine cipher is introduced. affine cipher is one of the oldest cryptographic techniques that.
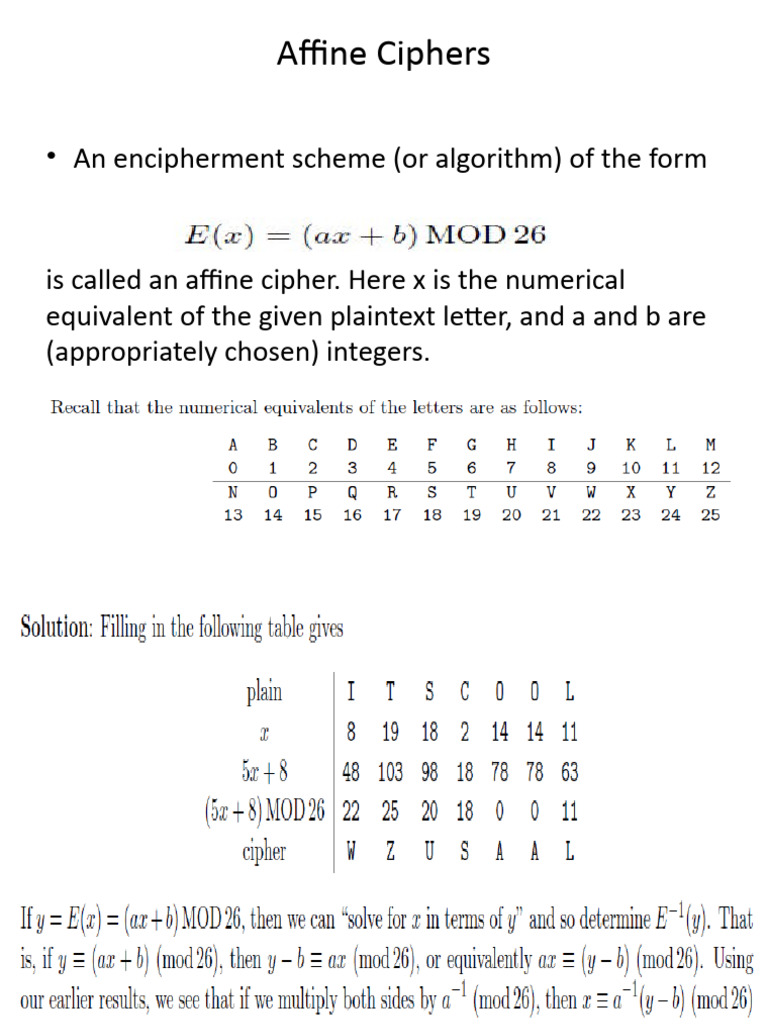
Affine Ciphers Pdf Cipher Cryptography What is the affine cipher? (definition) affine cipher is a monoalphabetic substitution method where each letter of the plaintext is replaced by another letter according to an affine function of the form $ f (x) = a \times x b \mod 26 $. In affine cipher each letter in an alphabet is mapped to its numeric equivalent, encrypted using a simple mathematical function, and converted back to a letter. The affine cipher represents one of the oldest and most elegant mathematical approaches to encryption. combining multiplication and addition in modular arithmetic, it transforms plaintext into ciphertext using two numeric keys. Find all possible keys. what are the requirements for a key to work? we now know how to encrypt a message using an affine cipher. however, it is just as important that we can decrypt the message at the other end, otherwise the person we are sending the message to will not be able to read it.
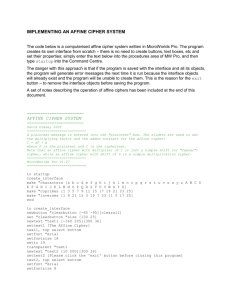
Affine Ciphers The affine cipher represents one of the oldest and most elegant mathematical approaches to encryption. combining multiplication and addition in modular arithmetic, it transforms plaintext into ciphertext using two numeric keys. Find all possible keys. what are the requirements for a key to work? we now know how to encrypt a message using an affine cipher. however, it is just as important that we can decrypt the message at the other end, otherwise the person we are sending the message to will not be able to read it. Let's encipher the message “hello world” with an affine cipher. let the multiplicative key be m = 5 and the shift s = 16; assume that we match up the alphabet with the integers from 0 to 25 in the usual way so that ‘a’ is 0, ‘b’ is 1, ‘c’ is 2, etc. It explains what affine ciphers are, how many possible keys there are, and methods for cryptanalysis of affine ciphers including using frequency analysis to determine the additive and multiplicative keys. Armed with the encrypting function (i.e., the "secret key" for the affine cipher), decrypting the message is straight forward just determine what each letter becomes under the function, and do the substitutions backwards. The affine cipher is a type of monoalphabetic substitution cipher, wherein each letter in an alphabet is mapped to its numeric equivalent, encrypted using a simple mathematical function, and converted back to a letter.
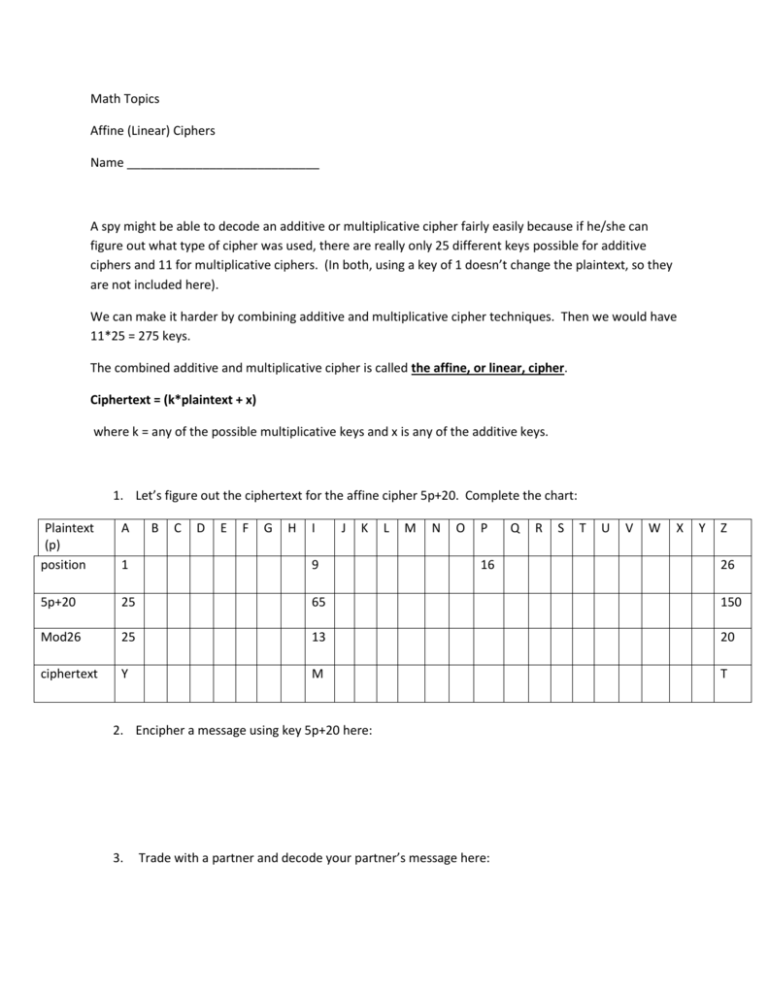
Affine Cipher Worksheet Encryption Decryption Let's encipher the message “hello world” with an affine cipher. let the multiplicative key be m = 5 and the shift s = 16; assume that we match up the alphabet with the integers from 0 to 25 in the usual way so that ‘a’ is 0, ‘b’ is 1, ‘c’ is 2, etc. It explains what affine ciphers are, how many possible keys there are, and methods for cryptanalysis of affine ciphers including using frequency analysis to determine the additive and multiplicative keys. Armed with the encrypting function (i.e., the "secret key" for the affine cipher), decrypting the message is straight forward just determine what each letter becomes under the function, and do the substitutions backwards. The affine cipher is a type of monoalphabetic substitution cipher, wherein each letter in an alphabet is mapped to its numeric equivalent, encrypted using a simple mathematical function, and converted back to a letter.
Comments are closed.