Affine Cipher Technique Pdf
Affine Cipher Pdf Cryptography Cipher Abstract: this paper presents a new encryption technique, which combines affine ciphers and the residue number system. To overcome these limitations, we propose an enhanced affine cipher algorithm that integrates a digraph transformation and a modified three pass protocol for secure key exchange.
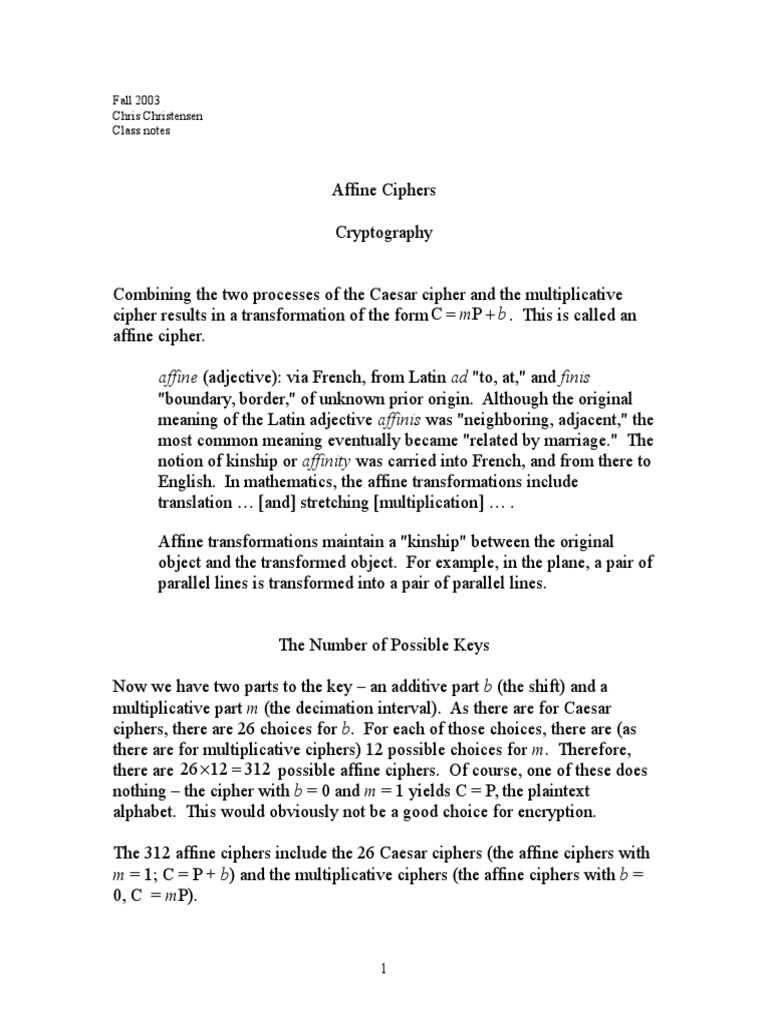
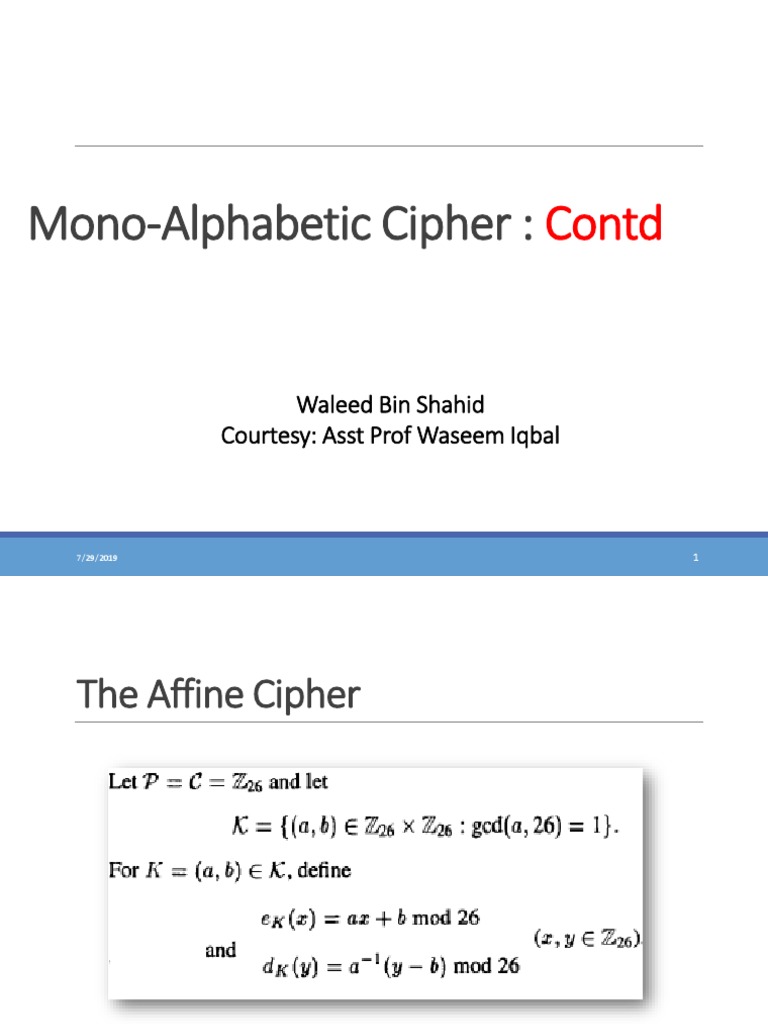
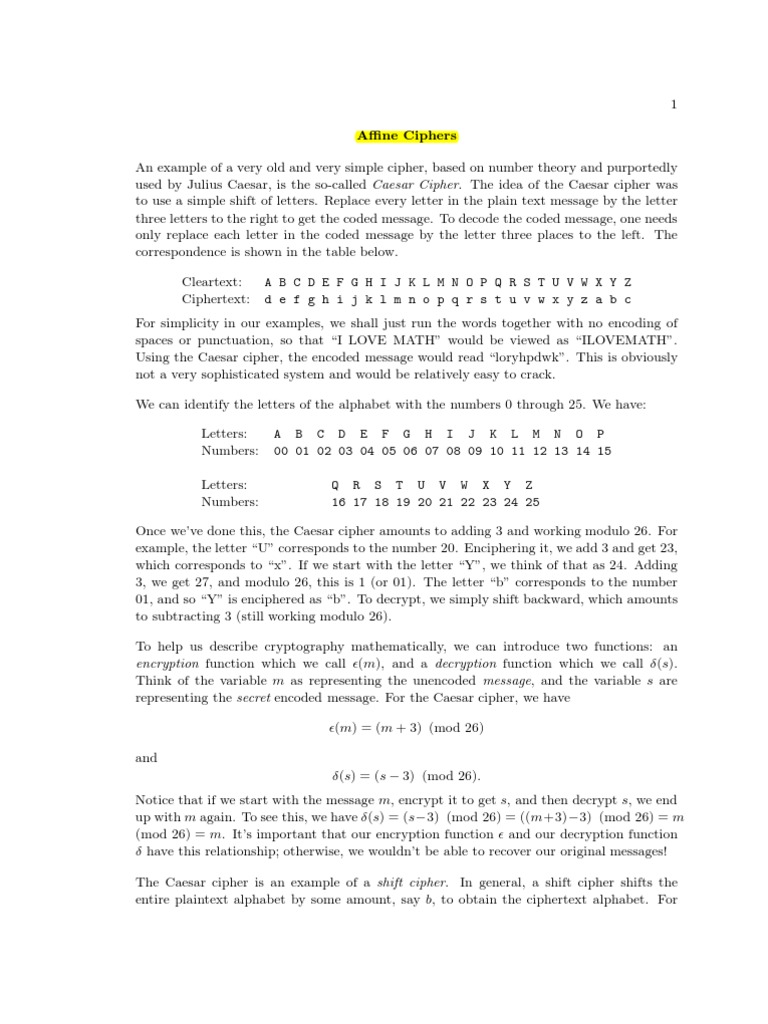
Affine Cipher Pdf Cipher Cryptanalysis Chapter two affine cipher addition (shifting) and multiplication can be combined to give an affine transformation. Affine cipher is a mono alphabetic substitution cipher, wherein each later in an alphabet is mapped out number equivalent, encrypted using a simple mathematical function and decrypted back to a. Eded is encrypted using the traditional affine cipher. first, each character is converted to its numerical equivalent according t its alphabetical index, such that a is 0 and z is 25. the alphabets a to z and the r corresponding index values are presented in table 1. based on the given, the numerical equivalent of the plaintext unneeded repre. Affine cipher is a monoalphabetic substitution cipher, wherein each later in an alphabet is mapped touts number equivalent, encrypted using a simple mathematical function and decrypted back to a letter.

Affine Cipher Pdf Eded is encrypted using the traditional affine cipher. first, each character is converted to its numerical equivalent according t its alphabetical index, such that a is 0 and z is 25. the alphabets a to z and the r corresponding index values are presented in table 1. based on the given, the numerical equivalent of the plaintext unneeded repre. Affine cipher is a monoalphabetic substitution cipher, wherein each later in an alphabet is mapped touts number equivalent, encrypted using a simple mathematical function and decrypted back to a letter. Affine.pdf free download as pdf file (.pdf), text file (.txt) or read online for free. an affine cipher is a generalization of a shift cipher that uses modular arithmetic. The affine cipher is simply a special case of the more general monoalphabetic substitution cipher. in this paper, we study the affine cipher and generalized affine cipher. This paper presents a new encryption technique, which combines affine ciphers and the residue number system. The hill cypher uses matrix features such as matrix multiplication and matrix inverse, and the affine cipher, which combines additive and multiplicative cyphers, requires two keys: one for the additive cypher and another for the multiplicative cypher.
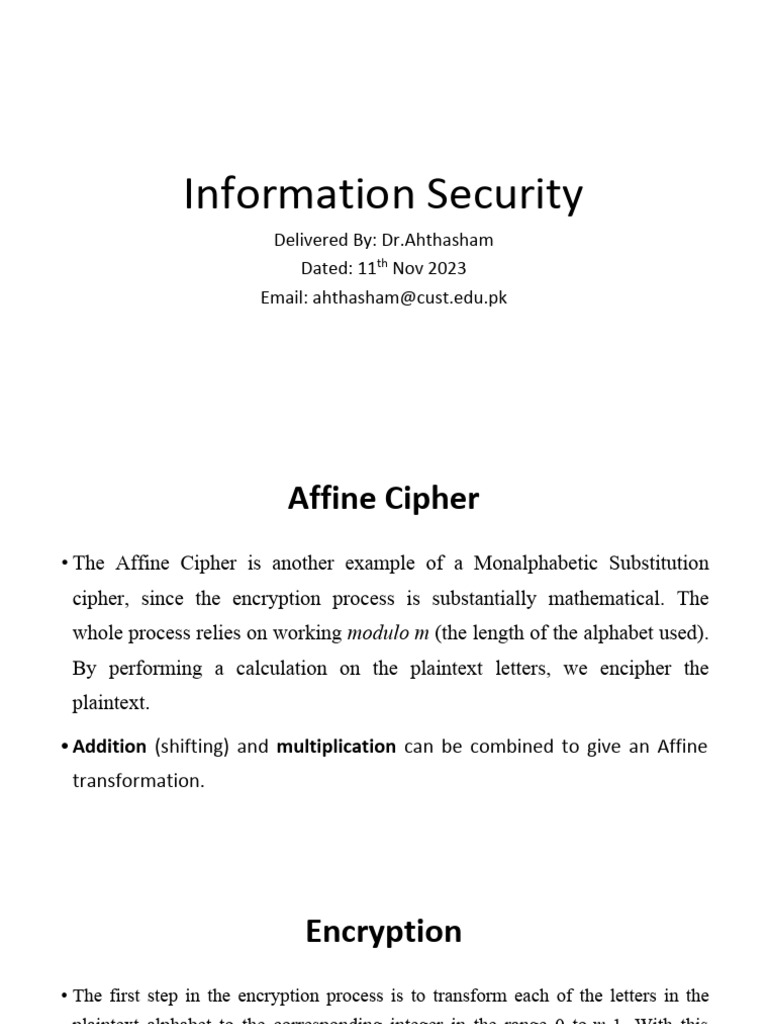
Lecture 15 Affine Cipher Pdf Encryption Mathematics Affine.pdf free download as pdf file (.pdf), text file (.txt) or read online for free. an affine cipher is a generalization of a shift cipher that uses modular arithmetic. The affine cipher is simply a special case of the more general monoalphabetic substitution cipher. in this paper, we study the affine cipher and generalized affine cipher. This paper presents a new encryption technique, which combines affine ciphers and the residue number system. The hill cypher uses matrix features such as matrix multiplication and matrix inverse, and the affine cipher, which combines additive and multiplicative cyphers, requires two keys: one for the additive cypher and another for the multiplicative cypher.
Affine Ciphers Pdf Cipher Cryptography This paper presents a new encryption technique, which combines affine ciphers and the residue number system. The hill cypher uses matrix features such as matrix multiplication and matrix inverse, and the affine cipher, which combines additive and multiplicative cyphers, requires two keys: one for the additive cypher and another for the multiplicative cypher.
Comments are closed.