Affine Cipher Pdf Cipher Cryptanalysis
Affine Cipher Pdf Cryptography Cipher It explains what affine ciphers are, how many possible keys there are, and methods for cryptanalysis of affine ciphers including using frequency analysis to determine the additive and multiplicative keys. Abstract this project researches methods to crack classical ciphers, specifically shift and affine ciphers. an is english program determines whether a given string of text is in english. in this project, different is english programs were used and compared to find which works best for cipher cracking.
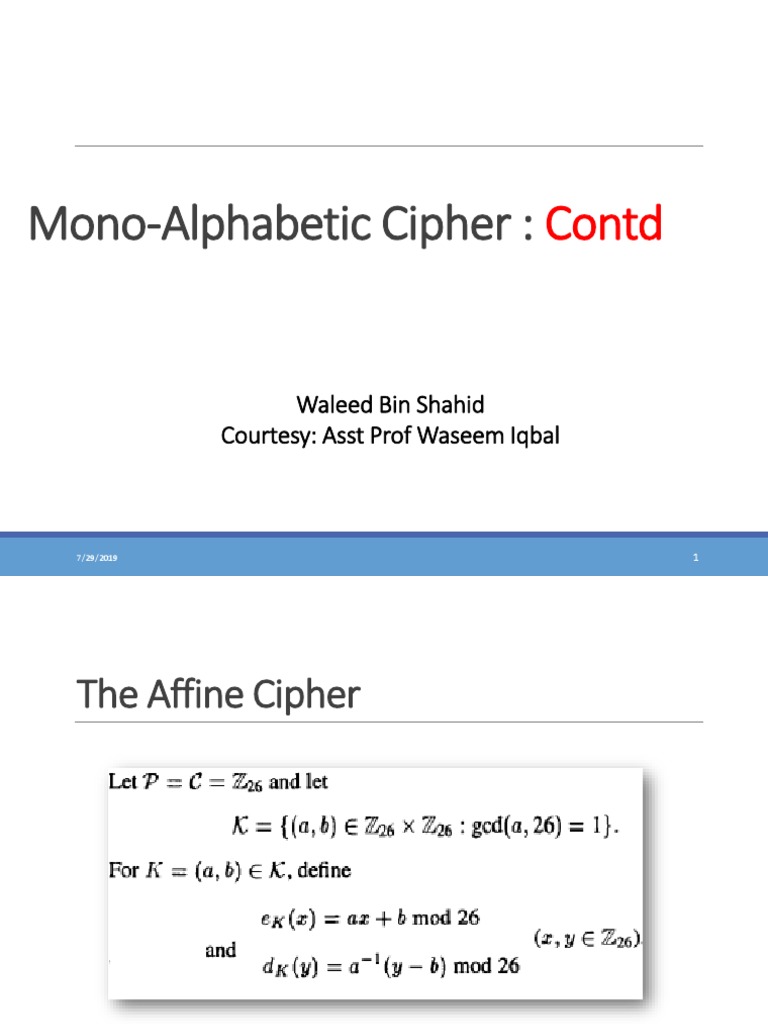
Affine Cipher Pdf Cipher Cryptanalysis In this research paper, we aim to investigate the cryptanalysis of the affine cipher using the brute force algorithm. our objective is to develop an implementation that can effectively decrypt a ciphertext encrypted using the affine cipher with a known alphabet size. Usually to encrypt or decrypt using an affine cipher, we would probably construct the plaintext ciphertext correspondences and make substitutions, but because affine encryption is a two step process, let’s consider a bit more carefully the decryption process. Affine ciphers an encipherment scheme (or algorithm) of the form e(x) = (ax b) mod 26 affine cipher. here x is the numerical equivalent of the given plaintext le b are (appropriately chosen) integers. We now know how to encrypt a message using an affine cipher. however, it is just as important that we can decrypt the message at the other end, otherwise the person we are sending the message to will not be able to read it.

Affine Cipher Pdf Affine ciphers an encipherment scheme (or algorithm) of the form e(x) = (ax b) mod 26 affine cipher. here x is the numerical equivalent of the given plaintext le b are (appropriately chosen) integers. We now know how to encrypt a message using an affine cipher. however, it is just as important that we can decrypt the message at the other end, otherwise the person we are sending the message to will not be able to read it. Affine cipher addition (shifting) and multiplication can be combined to give an affine transformation. Now we show how to obtain the key (a and w) of an affine block cipher using a set of known or chosen texts consider the encryption function of the d dimensional affine block cipher:. The affine cipher is simply a special case of the more general monoalphabetic substitution cipher. in this paper, we study the affine cipher and generalized affine cipher. Pdf | genetic algorithms (gas) have been used as a powerful tool for cryptanalyzing affine ciphers in this paper for the first time.
Comments are closed.