Affine Cipher Pdf
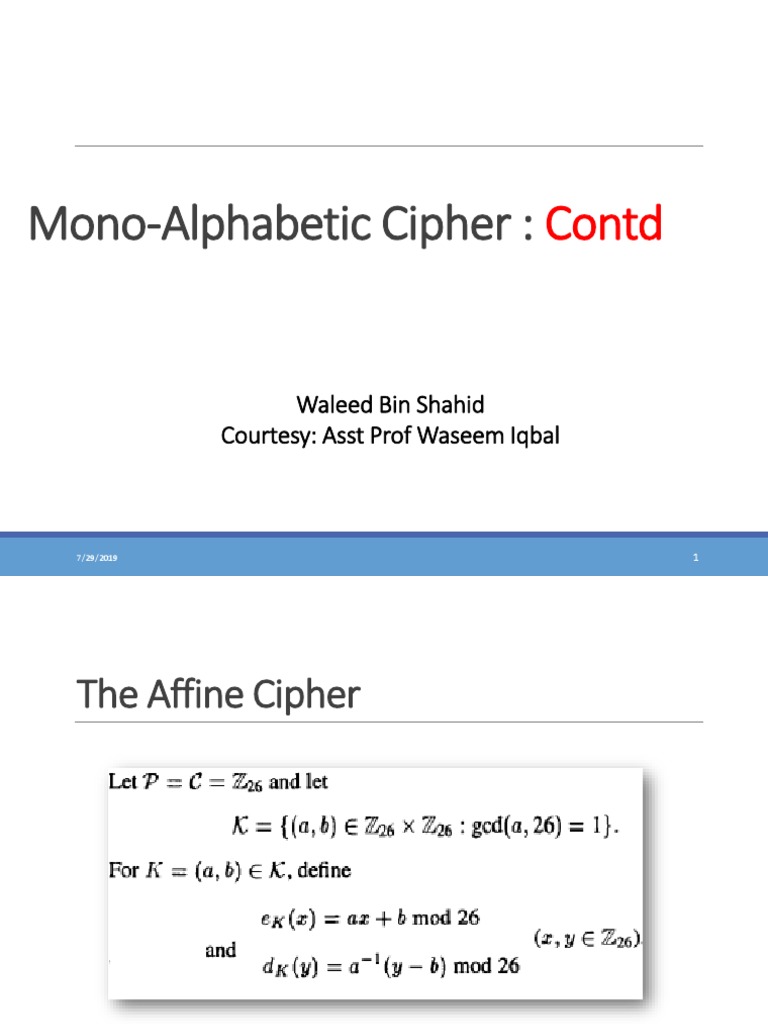
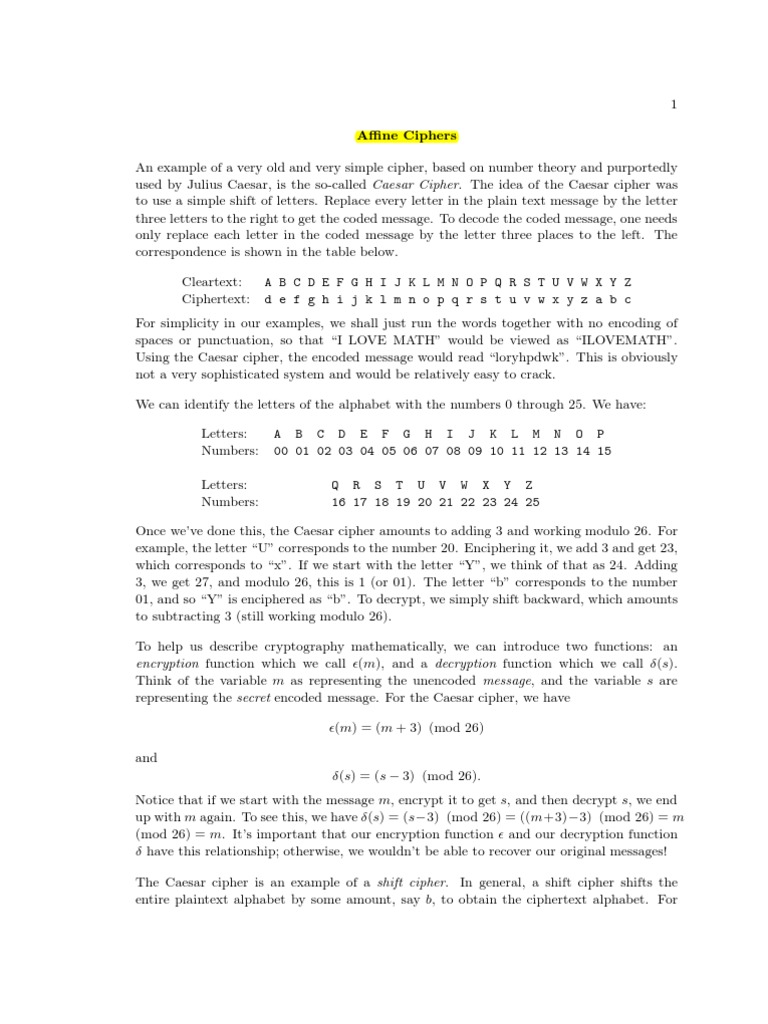
Affine Cipher Pdf Cryptography Cipher Affine ciphers an encipherment scheme (or algorithm) of the form e(x) = (ax b) mod 26 affine cipher. here x is the numerical equivalent of the given plaintext le b are (appropriately chosen) integers. Find all possible keys. what are the requirements for a key to work? we now know how to encrypt a message using an affine cipher. however, it is just as important that we can decrypt the message at the other end, otherwise the person we are sending the message to will not be able to read it.
Affine Cipher Pdf Cipher Cryptanalysis Now we show how to obtain the key (a and w) of an affine block cipher using a set of known or chosen texts consider the encryption function of the d dimensional affine block cipher:. Chapter two affine cipher addition (shifting) and multiplication can be combined to give an affine transformation. To encrypt or decrypt using an affine cipher, we would probably construct the plaintext ciphertext correspondences and make substitutions, but because affine encryption is a two step process, let’s look more carefully at the decryption process. Affine.pdf free download as pdf file (.pdf), text file (.txt) or read online for free. an affine cipher is a generalization of a shift cipher that uses modular arithmetic.

Affine Cipher Pdf To encrypt or decrypt using an affine cipher, we would probably construct the plaintext ciphertext correspondences and make substitutions, but because affine encryption is a two step process, let’s look more carefully at the decryption process. Affine.pdf free download as pdf file (.pdf), text file (.txt) or read online for free. an affine cipher is a generalization of a shift cipher that uses modular arithmetic. Affine ciphers an encipherment scheme (or algorithm) of the form e(x) = (ax b) mod 26 is called an affine cipher. here x is the numerical equivalent of the given plaintext letter, and a and b are (appropriately chosen) integers. recall that the numerical equivalents of the letters are as follows: b. The affine cipher is simply a special case of the more general monoalphabetic substitution cipher. in this paper, we study the affine cipher and generalized affine cipher. This paper presents a novel approach that combines a modified hill cipher (hc) with random network coding (rnc) to achieve secure and loss tolerant one to one communication. Affine cipher method affine method is used to encrypt and decrypt the message. tow operation can be applied to get the encryption processes which are addition and multiplication. so the 'key' for the affine cipher consists of 2 numbers, that mean two key need in this algorithm k1 and k2.
Lecture 15 Affine Cipher Pdf Encryption Mathematics Affine ciphers an encipherment scheme (or algorithm) of the form e(x) = (ax b) mod 26 is called an affine cipher. here x is the numerical equivalent of the given plaintext letter, and a and b are (appropriately chosen) integers. recall that the numerical equivalents of the letters are as follows: b. The affine cipher is simply a special case of the more general monoalphabetic substitution cipher. in this paper, we study the affine cipher and generalized affine cipher. This paper presents a novel approach that combines a modified hill cipher (hc) with random network coding (rnc) to achieve secure and loss tolerant one to one communication. Affine cipher method affine method is used to encrypt and decrypt the message. tow operation can be applied to get the encryption processes which are addition and multiplication. so the 'key' for the affine cipher consists of 2 numbers, that mean two key need in this algorithm k1 and k2.
Affine Ciphers Pdf Cipher Cryptography This paper presents a novel approach that combines a modified hill cipher (hc) with random network coding (rnc) to achieve secure and loss tolerant one to one communication. Affine cipher method affine method is used to encrypt and decrypt the message. tow operation can be applied to get the encryption processes which are addition and multiplication. so the 'key' for the affine cipher consists of 2 numbers, that mean two key need in this algorithm k1 and k2.
Comments are closed.