Advice Prepare A Zero Trust Roadmap Principle Zero

Zero Trust Roadmap Pdf Cloud Computing Cyberspace Zero trust can feel like a massive undertaking, but it doesn’t have to be overwhelming. by approaching it step by step, grounded in practical priorities and supported by the right tools, organizations can make real progress without getting stuck in strategy mode. To help, we’ve built a vendor neutral roadmap for the entire zero trust journey, covering these five projects and others like them. some will take far longer than a few days, but the roadmap can provide greater clarity into what zero trust adoption means.

Zero Trust Roadmap Wp Pdf Computer Network Proxy Server Implementing a zero trust architecture can be done in steps without disrupting employee productivity and connectivity. this roadmap was built by security experts to provide a vendor agnostic zero trust architecture and example implementation timeline. Follow our proven five step roadmap, deployment checklist, and expert faqs to roll out a zero trust security model without derailing operations. By following a practical roadmap, starting with foundational steps like securing internet traffic and strengthening identity, and progressively extending zero trust policies to applications, devices, and networks, organizations can achieve significant security posture improvements. Explore the key phases like preparation, strategy, and roadmap crucial for a successful zero trust implementation.

Advice Prepare A Zero Trust Roadmap Principle Zero By following a practical roadmap, starting with foundational steps like securing internet traffic and strengthening identity, and progressively extending zero trust policies to applications, devices, and networks, organizations can achieve significant security posture improvements. Explore the key phases like preparation, strategy, and roadmap crucial for a successful zero trust implementation. Simplify zero trust implementation with this detailed guide. learn the policies, compliance, and monitoring strategies to implement zero trust security. Zero trust is no longer just a buzzword – it's a strategic imperative. this guide breaks down the most common implementation approaches and how they align with specific use cases. The preparation phase sets the stage for a successful zero trust adoption by providing a clear understanding of the current security landscape, identifying critical assets, and ensuring stakeholder alignment. Implement zero trust security in your organization. learn the framework, key technologies (ztna, microsegmentation, iam), vendor comparison, and step by step deployment guide.
Your Zero Trust Roadmap Five Steps To Securing User Access To Applications Simplify zero trust implementation with this detailed guide. learn the policies, compliance, and monitoring strategies to implement zero trust security. Zero trust is no longer just a buzzword – it's a strategic imperative. this guide breaks down the most common implementation approaches and how they align with specific use cases. The preparation phase sets the stage for a successful zero trust adoption by providing a clear understanding of the current security landscape, identifying critical assets, and ensuring stakeholder alignment. Implement zero trust security in your organization. learn the framework, key technologies (ztna, microsegmentation, iam), vendor comparison, and step by step deployment guide.

A Roadmap For Zero Trust The preparation phase sets the stage for a successful zero trust adoption by providing a clear understanding of the current security landscape, identifying critical assets, and ensuring stakeholder alignment. Implement zero trust security in your organization. learn the framework, key technologies (ztna, microsegmentation, iam), vendor comparison, and step by step deployment guide.
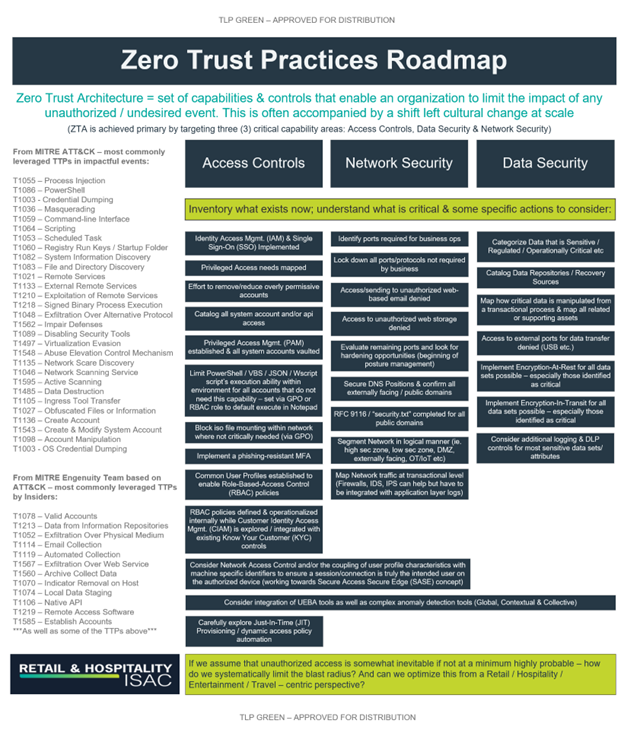
Rh Isac A Roadmap To Zero Trust Maturity Rh Isac
Comments are closed.