Adversarial Attacks On Deeplearning Github

Adversarial Attacks In Underwater Acoustic Target Recognition With Deep Our project presents the first large scale, unified empirical study of adversarial attacks and defenses across key computer vision and language modeling tasks—including image classification, segmentation, object detection, nlp, llms, and automatic speech recognition. To understand what makes cnns vulnerable to such attacks, we will implement our own adversarial attack strategies in this notebook, and try to fool a deep neural network.

Trustworthiness Of Deep Learning Under Adversarial Attacks In Power Systems This project offers the following features to facilitate the development of adversarial attacks and defenses: it supports ten state of the art attack algorithms with easy to use interfaces. Cleverhans is a library for performing evasion attacks and testing the robustness of a deep learning model on image models. it is developed in python and integrates with the tensorflow, torch and jax frameworks. Adversarial attacks are techniques that craft intentionally perturbed inputs to mislead machine learning models into producing incorrect outputs. they are central to research in ai robustness, security, and trustworthiness. In this work, we comprehensively survey and present the latest research on attacks based on adversarial examples against deep learning based cybersecurity systems, highlighting the risks they pose and promoting efficient countermeasures.
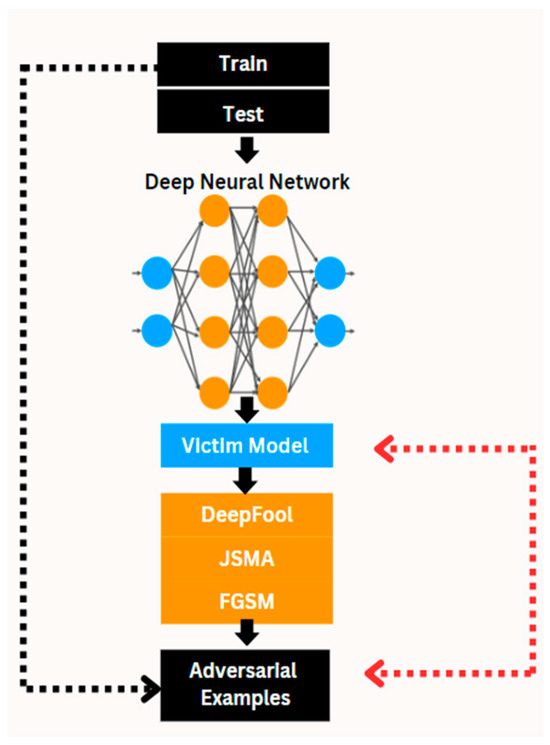
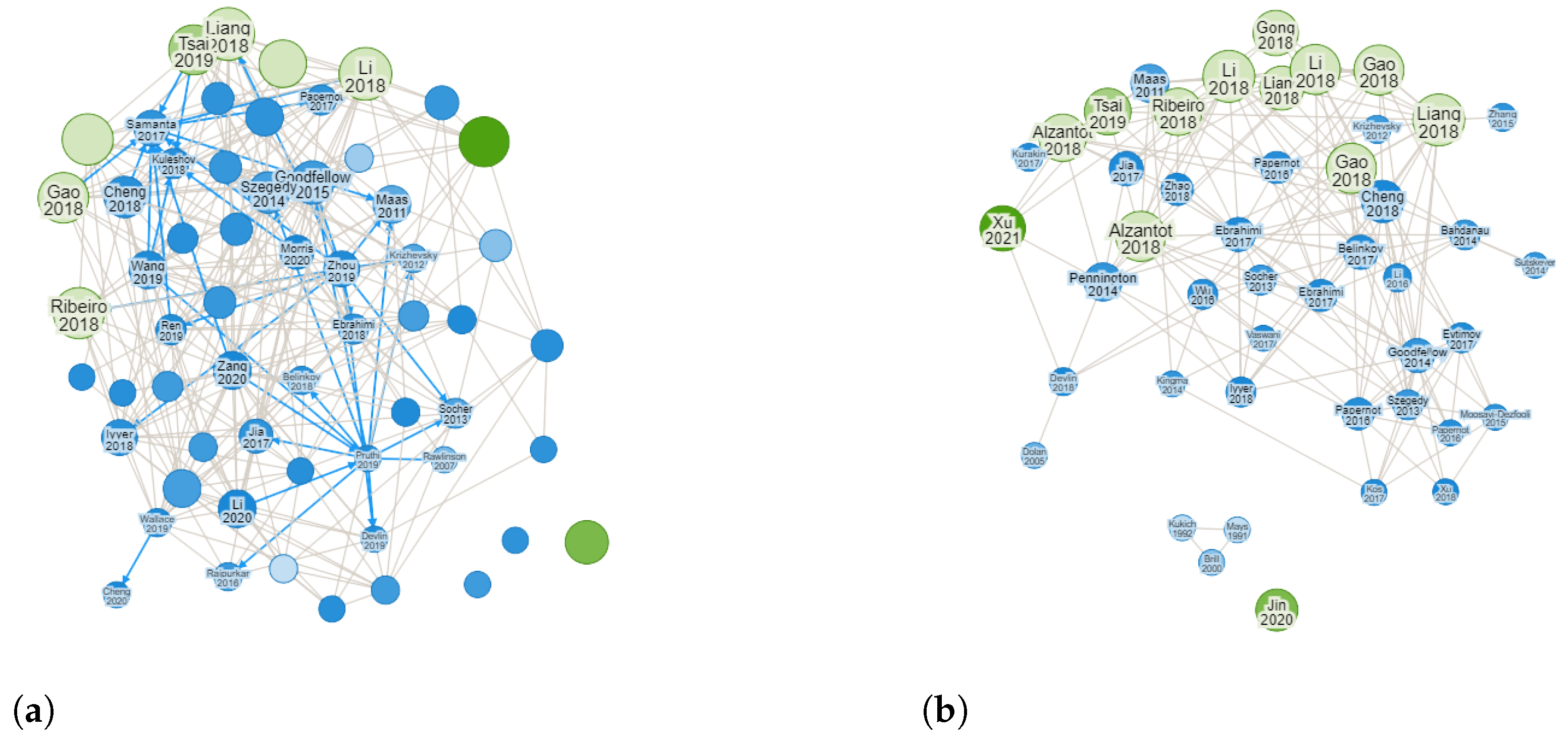
Trustworthiness Of Deep Learning Under Adversarial Attacks In Power Systems Adversarial attacks are techniques that craft intentionally perturbed inputs to mislead machine learning models into producing incorrect outputs. they are central to research in ai robustness, security, and trustworthiness. In this work, we comprehensively survey and present the latest research on attacks based on adversarial examples against deep learning based cybersecurity systems, highlighting the risks they pose and promoting efficient countermeasures. Inspired by apts, we propose an analysis framework for adversarial attacks that could help to establish a standard in understanding the security problems of deep learning systems. A curated list of adversarial attacks and defenses papers on graph structured data. Abstract—with rapid progress and significant successes in a wide spectrum of applications, deep learning is being applied in many safety critical environments. however, deep neural net works have been recently found vulnerable to well designed input samples, called adversarial examples. It currently contains more than 10 attack algorithms and 8 defense algorithms in image domain and 9 attack algorithms and 4 defense algorithms in graph domain, under a variety of deep learning architectures. in this manual, we introduce the main contents of deeprobust with detailed instructions.
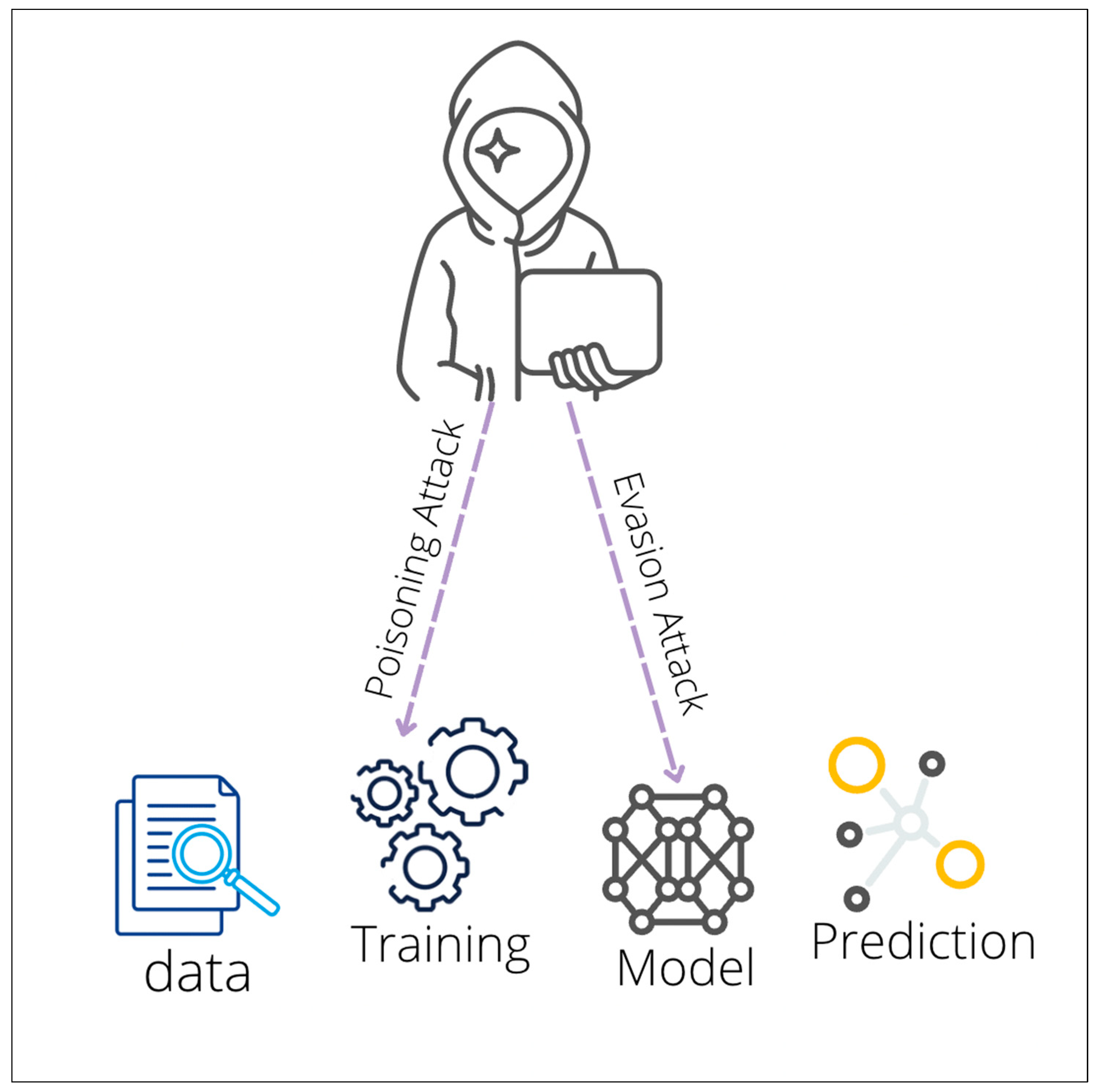
Adversarial Machine Learning Attacks Against Intrusion Detection Inspired by apts, we propose an analysis framework for adversarial attacks that could help to establish a standard in understanding the security problems of deep learning systems. A curated list of adversarial attacks and defenses papers on graph structured data. Abstract—with rapid progress and significant successes in a wide spectrum of applications, deep learning is being applied in many safety critical environments. however, deep neural net works have been recently found vulnerable to well designed input samples, called adversarial examples. It currently contains more than 10 attack algorithms and 8 defense algorithms in image domain and 9 attack algorithms and 4 defense algorithms in graph domain, under a variety of deep learning architectures. in this manual, we introduce the main contents of deeprobust with detailed instructions.

A Survey Of Adversarial Attacks An Open Issue For Deep Learning Abstract—with rapid progress and significant successes in a wide spectrum of applications, deep learning is being applied in many safety critical environments. however, deep neural net works have been recently found vulnerable to well designed input samples, called adversarial examples. It currently contains more than 10 attack algorithms and 8 defense algorithms in image domain and 9 attack algorithms and 4 defense algorithms in graph domain, under a variety of deep learning architectures. in this manual, we introduce the main contents of deeprobust with detailed instructions.
A Survey Of Adversarial Attacks An Open Issue For Deep Learning
Comments are closed.