Administering Encryption Profiles

Encryption Profiles Access the administer encryption profile page (peopletools > security > encryption > encryption profiles). the fields and controls on the page vary depending upon whether you are creating a new profile or modifying an existing profile, and depending upon the requirements of the profile components. Encryption profiles can be managed with either a graphical user interface or with a command line interface. encryption profiles are stored in the secrets.jks file in the cdc replication keystore directory. the password that cdc replication needs to access secrets.jks is stored in secrets.b64.

Encryption Profiles To use your encryption profile, follow the steps below: you can have different encryption profiles for each available environment mode (uat, dev, prod). go to your web service miniapp where you want to use the encryption service. This section of the guide on the recommendations for the secure configuration of an sns firewall in version 4.3 ltsb lists the recommended encryption profiles. Learn about the available options to configure personal data encryption and how to configure them via microsoft intune or configuration service providers (csp). This document describes the configuration of the cisco registered envelope service encryption (cres) profiles within the email security appliance (esa) focused on the different security levels allowed.

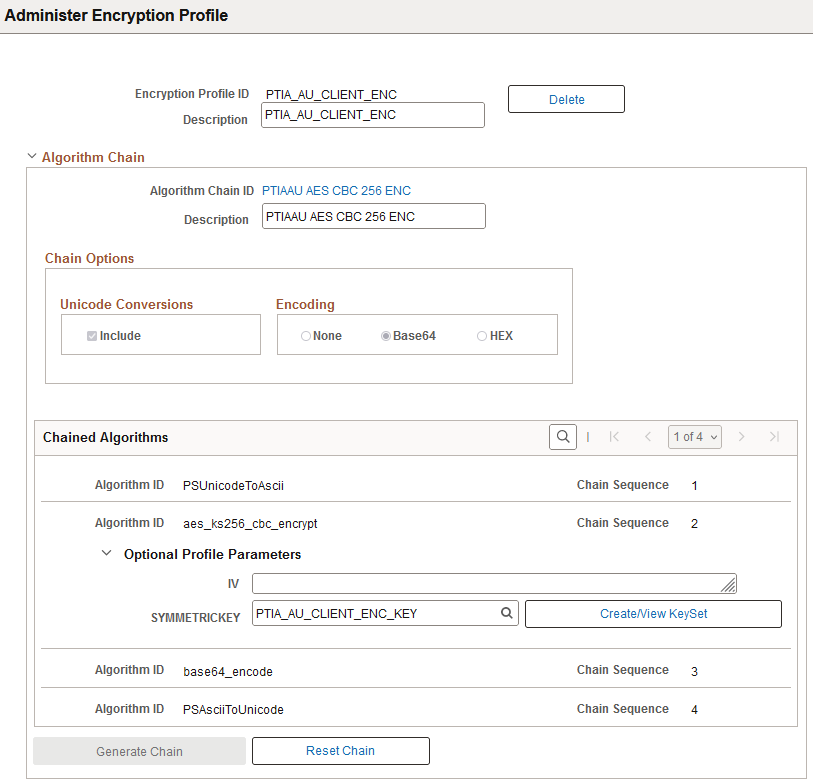
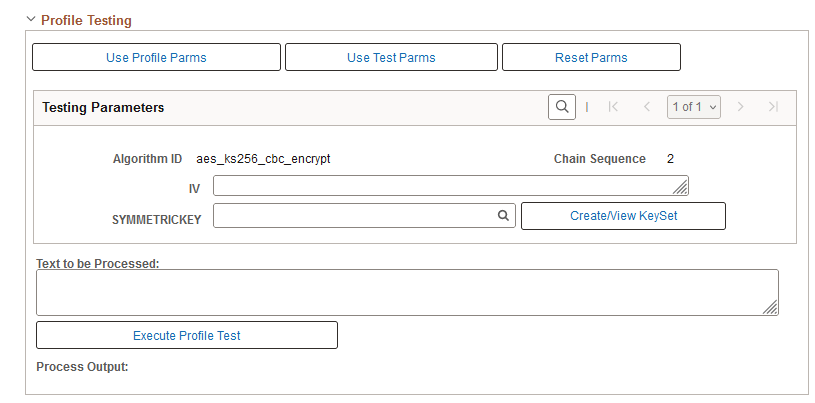
Encryption Profiles Learn about the available options to configure personal data encryption and how to configure them via microsoft intune or configuration service providers (csp). This document describes the configuration of the cisco registered envelope service encryption (cres) profiles within the email security appliance (esa) focused on the different security levels allowed. This example illustrates the fields and controls on the encryption profile page. to define a new encryption profile, specify a new profile id, then select an algorithm chain id. each algorithm in the chain appears in order, in its own row with its algorithm id and chain sequence number. You can use the command line version of the configuration tool to manage encryption profiles. This article details the settings you can find in bitlocker profiles created before june 19, 2023, for the windows 10 and later platform for endpoint security disk encryption policy. You will discuss the best practices of organizing, implementing, administering, and evaluating peoplesoft security; explore the capabilities of application security by creating permission lists, roles, and user profiles; and use development security to control peopletools such as application designer, process scheduler, query, and data mover.

Encryption Profiles This example illustrates the fields and controls on the encryption profile page. to define a new encryption profile, specify a new profile id, then select an algorithm chain id. each algorithm in the chain appears in order, in its own row with its algorithm id and chain sequence number. You can use the command line version of the configuration tool to manage encryption profiles. This article details the settings you can find in bitlocker profiles created before june 19, 2023, for the windows 10 and later platform for endpoint security disk encryption policy. You will discuss the best practices of organizing, implementing, administering, and evaluating peoplesoft security; explore the capabilities of application security by creating permission lists, roles, and user profiles; and use development security to control peopletools such as application designer, process scheduler, query, and data mover.
Administering Encryption Profiles This article details the settings you can find in bitlocker profiles created before june 19, 2023, for the windows 10 and later platform for endpoint security disk encryption policy. You will discuss the best practices of organizing, implementing, administering, and evaluating peoplesoft security; explore the capabilities of application security by creating permission lists, roles, and user profiles; and use development security to control peopletools such as application designer, process scheduler, query, and data mover.
Administering Encryption Profiles
Comments are closed.