Access Rules Idsecure Cloud English
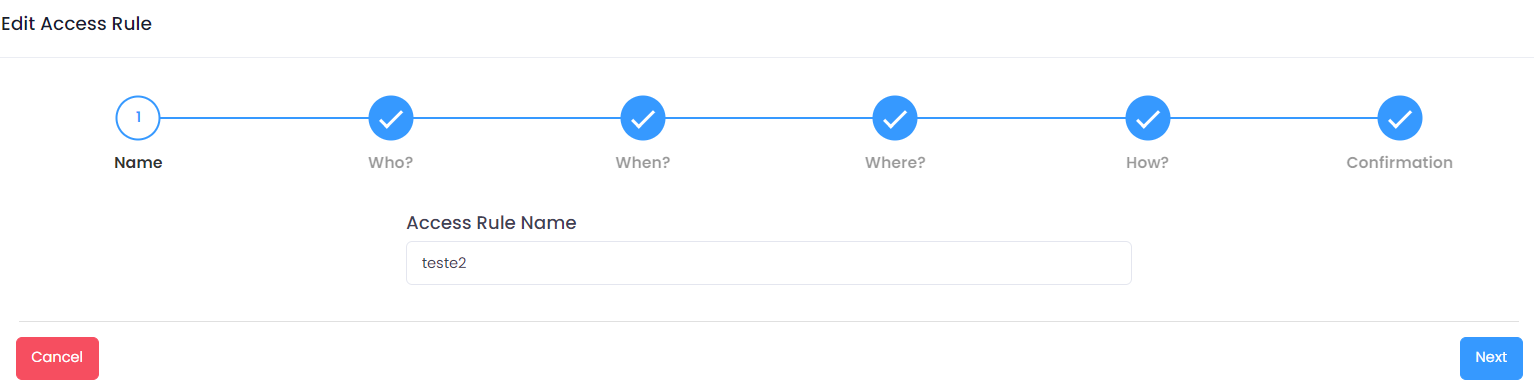
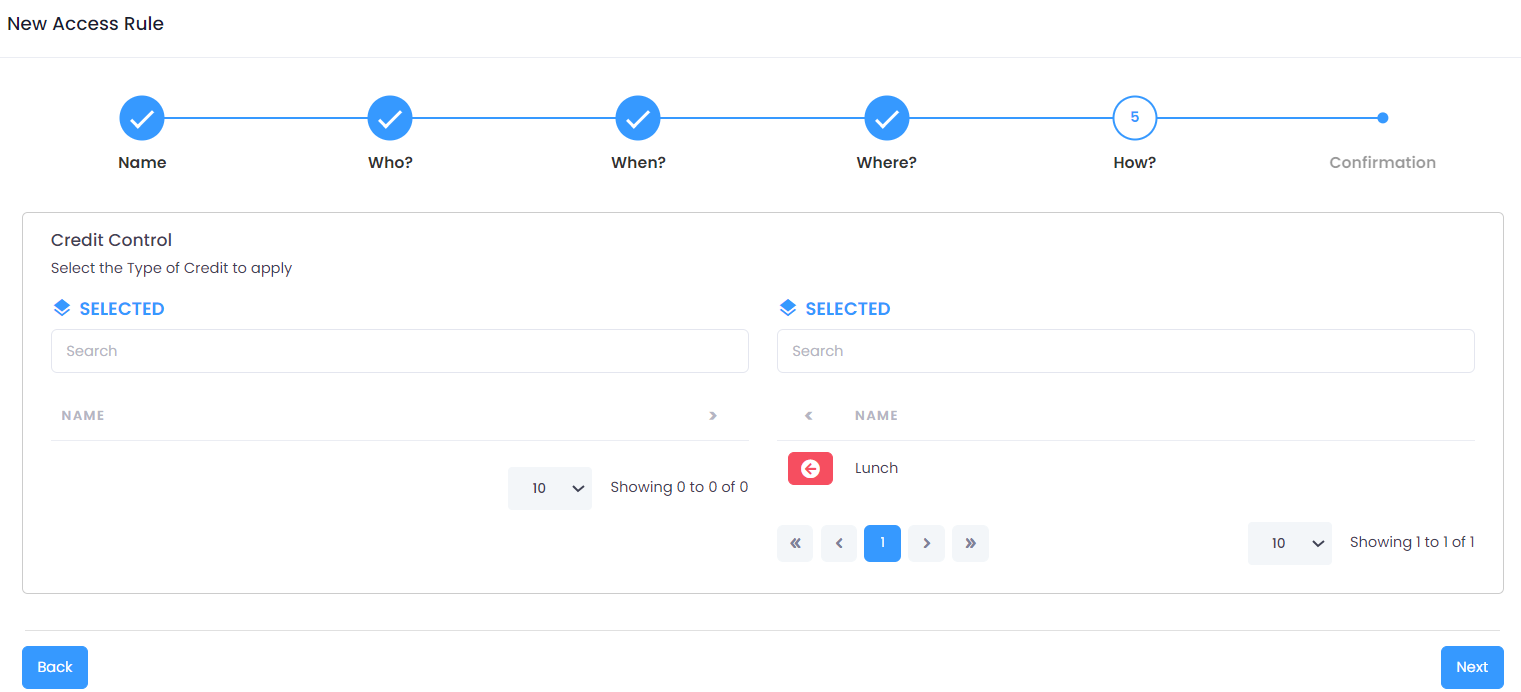
Access Control Software Idsecure Cloud Control Id Registering access rules in idsecure is a detailed process divided into 6 steps. these steps help configure the exact conditions to allow or deny access to certain areas for different users. With idsecure cloud, the configuration of devices is easy and friendly and access rule management is fast and secure. the system can be accessed by browser in any type of device.

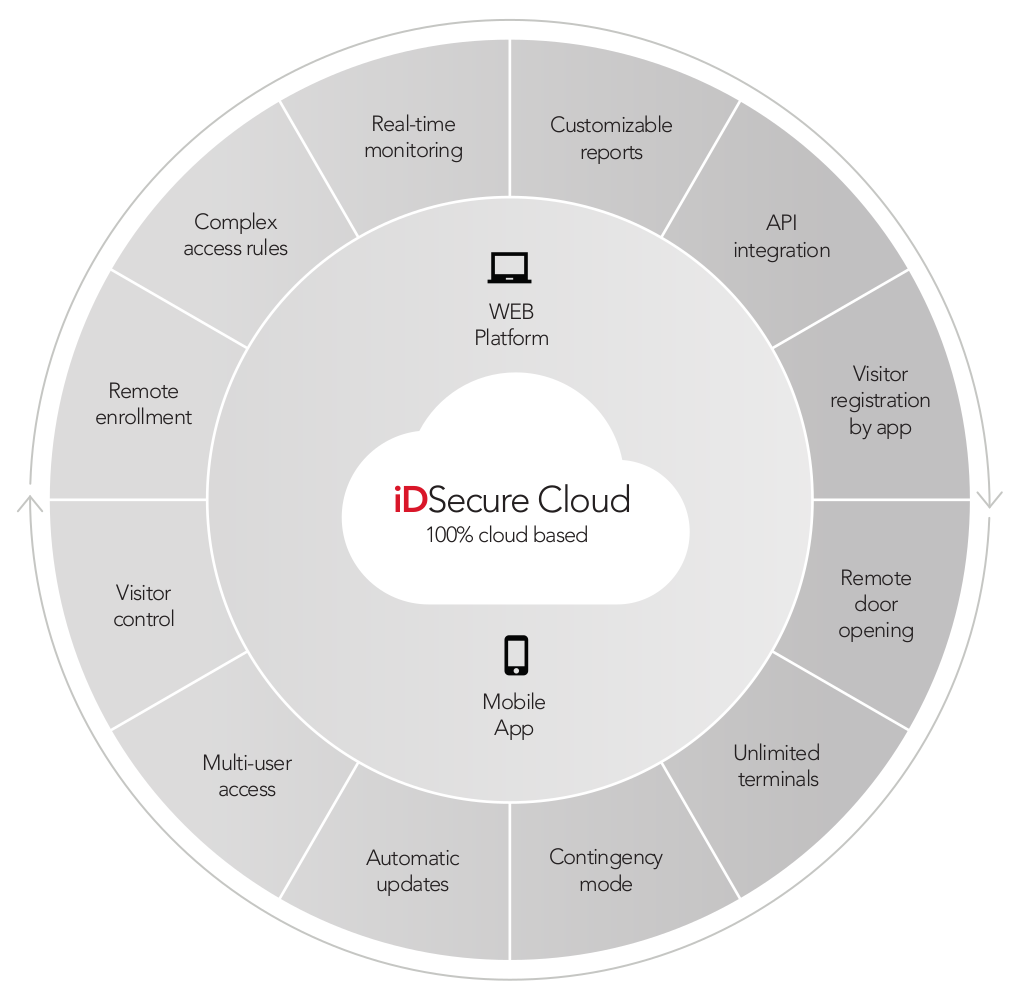
Control Id Idsecure Cloud Access Control Software Instructions Discover how to set up and manage your devices with the idsecure cloud software user manual. learn to connect devices, enroll users, create schedules, access rules, and areas effortlessly. With idsecure cloud, the configuration of devices is easy and friendly and access rule management is fast and secure. the system can be accessed by browser in any type of device. The cloud based software and the mobile app allow the use of any type of device, anywhere, to manage access rules in real time.the idsecure cloud platform was developed with a focus on usability, making the experience of the manager and security professional as intuitive as possible. The access menu presents tools for configuring various access related functionalities. through it, it is possible to configure devices, areas, schedules, access rules, and email notifications.
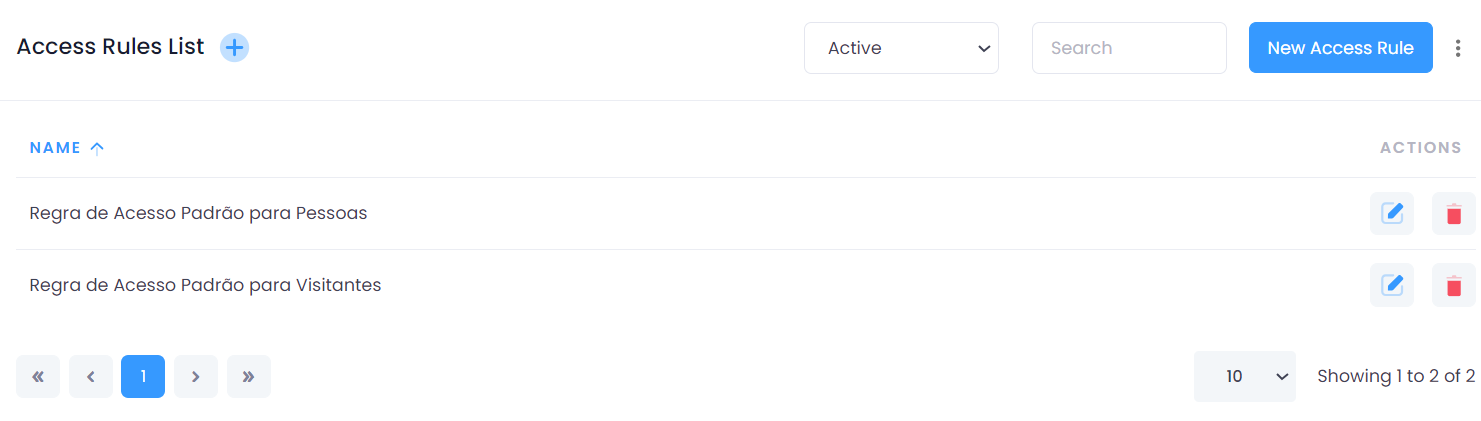
Access Rules Idsecure Saas Manual The cloud based software and the mobile app allow the use of any type of device, anywhere, to manage access rules in real time.the idsecure cloud platform was developed with a focus on usability, making the experience of the manager and security professional as intuitive as possible. The access menu presents tools for configuring various access related functionalities. through it, it is possible to configure devices, areas, schedules, access rules, and email notifications. Idsecure cloud allows you to generate various types of reports, one of them being the “access logs”. to view the logs, go into “reports” > “access logs” and click on the blue icon on the right. Compatibility with the most advanced security requirements. all control id access controllers (e.g., idaccess, idbox, idface and idblock) are natively integrated with idsecure cloud and. With idsecure cloud, the configuration of devices is easy and friendly and access rule management is fast and secure. the system can be accessed by browser in any type of device. To access the system settings, navigate to the side menu and select: settings > system. by accessing the system settings screen, you will have access to seven tabs that allow you to customize the system according to your preferences.
Access Rules Idsecure Saas Manual Idsecure cloud allows you to generate various types of reports, one of them being the “access logs”. to view the logs, go into “reports” > “access logs” and click on the blue icon on the right. Compatibility with the most advanced security requirements. all control id access controllers (e.g., idaccess, idbox, idface and idblock) are natively integrated with idsecure cloud and. With idsecure cloud, the configuration of devices is easy and friendly and access rule management is fast and secure. the system can be accessed by browser in any type of device. To access the system settings, navigate to the side menu and select: settings > system. by accessing the system settings screen, you will have access to seven tabs that allow you to customize the system according to your preferences.
Access Rules Idsecure Saas Manual With idsecure cloud, the configuration of devices is easy and friendly and access rule management is fast and secure. the system can be accessed by browser in any type of device. To access the system settings, navigate to the side menu and select: settings > system. by accessing the system settings screen, you will have access to seven tabs that allow you to customize the system according to your preferences.

Access Control Software Idsecure Cloud Control Id Assa Abloy
Comments are closed.