Access Control Types Role Based Access Control Attribute Based Access Control
What Are The Three Types Of Access 3 Types Of Access Control Are Rbac grants access based on user roles, pbac grants access based on policies, and abac grants access based on attributes, or characteristics, of the user, resource, and environment involved during sign on. Knowing the difference between role based access control (rbac) vs. attribute based access control (abac) can help you make a smart decision. the main difference between rbac vs. abac is the way each method grants access. rbac techniques allow you to grant access by roles.
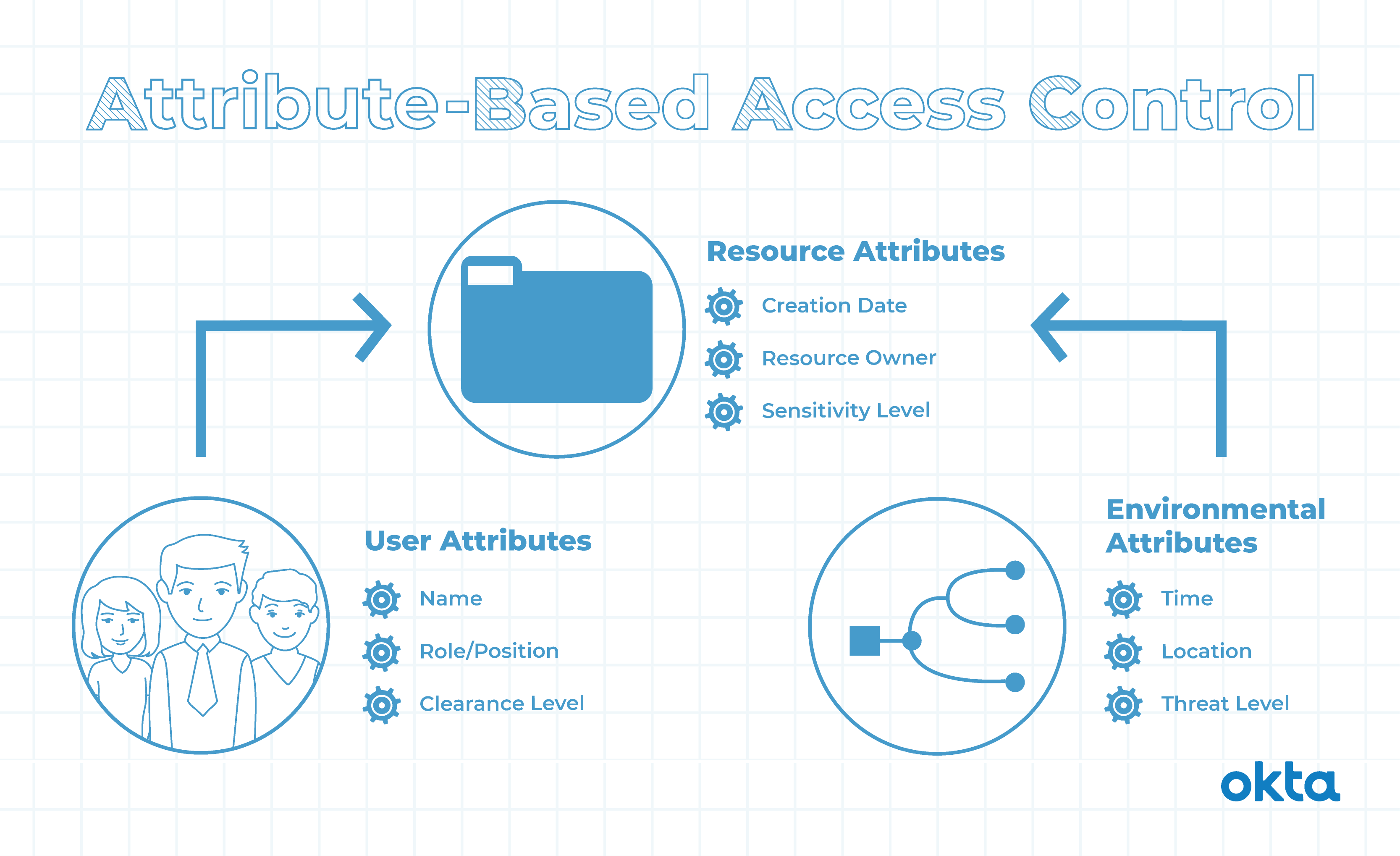
Rbac Vs Abac Definitions When To Use Okta You can use two broadly defined models to implement access control: role based access control (rbac) and attribute based access control (abac). each model has advantages and disadvantages, which are briefly discussed in this section. Role based access control vs. attribute based access control – which is better for you? find out how rbac and abac stack up here. Learn about discretionary, mandatory, rule based, role based, and attribute based access control. compare advantages and drawbacks of each with jumpcloud. In this article, we analyze the two most popular access control models: role based and attribute based. we explain what rbac and abac are, review their pros and cons, highlight their differences, and discuss whether it’s possible to combine them.
Why Attribute Based Access Control Is Replacing Role Based Access Learn about discretionary, mandatory, rule based, role based, and attribute based access control. compare advantages and drawbacks of each with jumpcloud. In this article, we analyze the two most popular access control models: role based and attribute based. we explain what rbac and abac are, review their pros and cons, highlight their differences, and discuss whether it’s possible to combine them. Compliance requires granular control over who can access what, when, and how. “abac enables more granular control by granting access based on a combination of user, resource, and environmental attributes, making it ideal for organizations with complex access requirements.”. The guide compares role based access control (rbac), attribute based access control (abac), and policy based access control (pbac), maps the steps from identification to enforcement, and weighs strengths and trade offs so teams pick a model that matches risk, compliance, and operations. Role based access control (rbac) and attribute based access control (abac) are two dominant models, each with unique strengths and weaknesses. with cyber threats rising by 15% annually, according to cybersecurity ventures, organizations must adopt robust access control models. Two popular models dominate the physical access control conversation: role based access control and attribute based access control. both approaches have strengths and weaknesses, and choosing the right one depends on your organization’s size, layout, and security needs.
Attribute Based Access Control Prompts Stable Diffusion Online Compliance requires granular control over who can access what, when, and how. “abac enables more granular control by granting access based on a combination of user, resource, and environmental attributes, making it ideal for organizations with complex access requirements.”. The guide compares role based access control (rbac), attribute based access control (abac), and policy based access control (pbac), maps the steps from identification to enforcement, and weighs strengths and trade offs so teams pick a model that matches risk, compliance, and operations. Role based access control (rbac) and attribute based access control (abac) are two dominant models, each with unique strengths and weaknesses. with cyber threats rising by 15% annually, according to cybersecurity ventures, organizations must adopt robust access control models. Two popular models dominate the physical access control conversation: role based access control and attribute based access control. both approaches have strengths and weaknesses, and choosing the right one depends on your organization’s size, layout, and security needs.
Comments are closed.