Access Control Models Pdf Computer Access Control Information

Access Control Models And Methods Types Of Access Control Pdf This paper is concerned with overview and analysis for a number of access control models. first, an overview of access control models is presented. The document provides an overview and analysis of various access control models. it describes models like identity based access control, access control lists, capabilities, multilevel access control and mandatory access control.

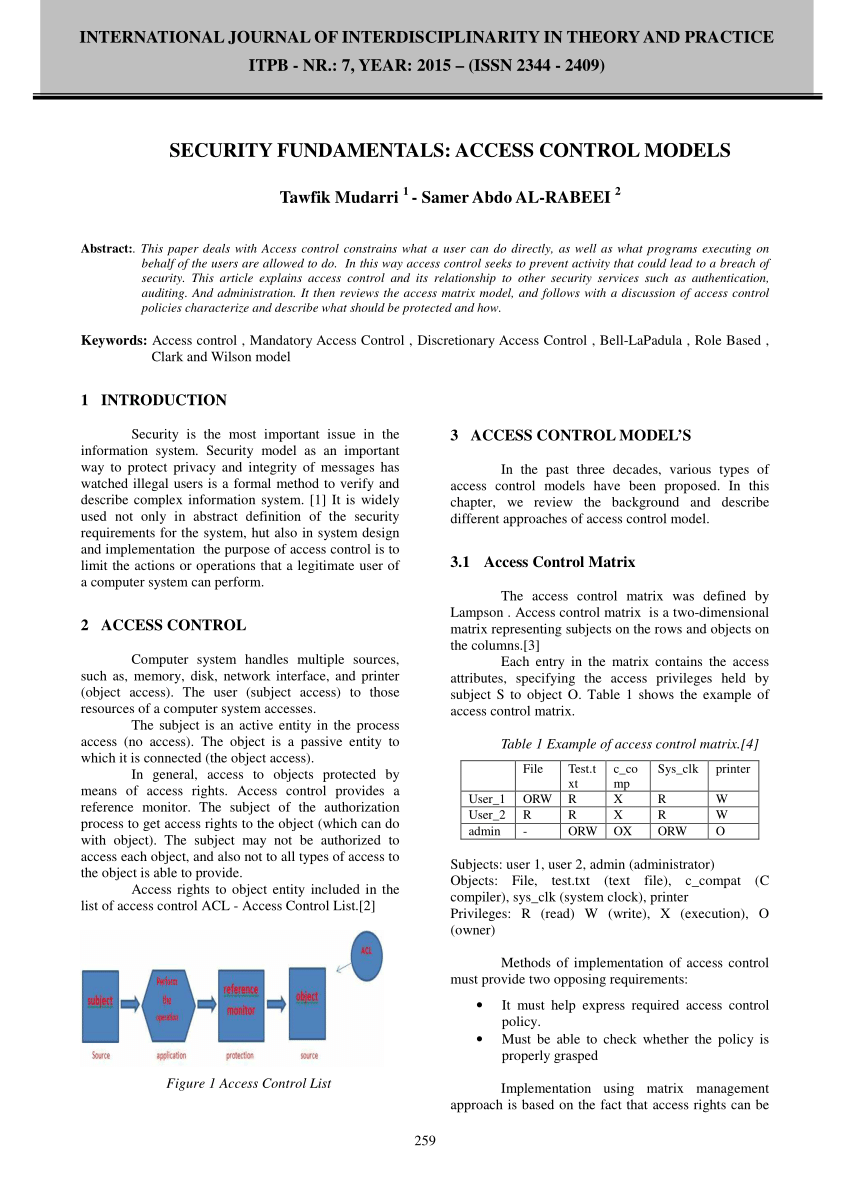
Access Control Modes Pdf Computer Access Control Operating System The rest of this paper discusses current and future access control models—including access control lists, role based access control, attribute based access control, policy based access control, and risk adaptive access control—and the infrastructure needed to support them. This paper comprehensively analyzes access control models (acms) through a two pronged approach. first, we conduct a narrative literature review (nlr) to classify traditional acms, evaluating their security strengths and weaknesses and compatible security protocols. While an access control mechanism defines how the access control does behave, an access control model specifies how it shall behave how shall it be decided whether a requested access is permitted or not?. Access control models are usually seen as frameworks for implementing and ensuring the integrity of security policies that mandate how information can be accessed and shared on a system.

Attribute Based Access Control Model In2 Pdf Computer Access While an access control mechanism defines how the access control does behave, an access control model specifies how it shall behave how shall it be decided whether a requested access is permitted or not?. Access control models are usually seen as frameworks for implementing and ensuring the integrity of security policies that mandate how information can be accessed and shared on a system. This paper conducts a comprehensive exploration of access control, traversing from traditional paradigms like dac, mac, rbac, and abac to contemporary trends such as policy based access control and blockchain based access control. In this chapter we illustrate different access control policies and models that have been proposed in the literature, also investigating their low level implementation in terms of security mechanisms. With the developing of information technologies, more complex access control models have been created. this paper is concerned with overview and analysis for a number of access control models. In this chapter we investigate the basic concepts behind access control design and enforcement, and point out different security requirements that may need to be taken into consideration.
Pdf Security Fundamentals Access Control Models This paper conducts a comprehensive exploration of access control, traversing from traditional paradigms like dac, mac, rbac, and abac to contemporary trends such as policy based access control and blockchain based access control. In this chapter we illustrate different access control policies and models that have been proposed in the literature, also investigating their low level implementation in terms of security mechanisms. With the developing of information technologies, more complex access control models have been created. this paper is concerned with overview and analysis for a number of access control models. In this chapter we investigate the basic concepts behind access control design and enforcement, and point out different security requirements that may need to be taken into consideration.

Access Control Models Pdf Computer Access Control Information With the developing of information technologies, more complex access control models have been created. this paper is concerned with overview and analysis for a number of access control models. In this chapter we investigate the basic concepts behind access control design and enforcement, and point out different security requirements that may need to be taken into consideration.

04 Access Control Pdf Computer Access Control Computer File
Comments are closed.