Access Control Matrix Ppt

Access Control Matrix 2 Pdf This document discusses access control and protection states. it provides an overview of access control matrices, which represent protection states by defining the access rights of subjects over objects. Explore our fully editable and customizable access control matrix powerpoint presentation, designed to help you effectively manage and visualize access permissions in your organization.

Bab Iii Access Control Matrix Pdf Access control matrix free download as powerpoint presentation (.ppt), pdf file (.pdf), text file (.txt) or view presentation slides online. the document discusses access control matrices and protection states. This document provides an in depth overview of the access control matrix (acm) model used in computer security and integrity. it describes the structure and function of the acm, including how it characterizes the rights of subjects in relation to objects. Access control matrix csse 490 computer security mark ardis, rose hulman institute march 9, 2004. With this rbac matrix ppt template, you'll be able to outline your whole plan for secure and intelligent user management in a format your audience will easily understand. moreover, it's perfect for showing decision makers how access rules actually protect data while making workflows smoother.

Access Control Matrix Ppt Powerpoint Presentation Ideas Examples Cpb Access control matrix csse 490 computer security mark ardis, rose hulman institute march 9, 2004. With this rbac matrix ppt template, you'll be able to outline your whole plan for secure and intelligent user management in a format your audience will easily understand. moreover, it's perfect for showing decision makers how access rules actually protect data while making workflows smoother. Based on slides provided by matt bishop for use with computer security: art and science. plus hru examples from ravi sandhu. It describes common access control models like discretionary access control (dac), mandatory access control (mac), and role based access control (rbac). it also discusses access control terminology, technical processes, and best practices for implementing access controls. Access control matrix.ppt free download as powerpoint presentation (.ppt), pdf file (.pdf), text file (.txt) or view presentation slides online. the document discusses access control matrices and protection state transitions. Role based access control (rbac) matrix is an essential framework for managing user permissions and access rights within an organization. this model allows administrators to define roles based on job functions and assign permissions to those roles rather than to individual users.
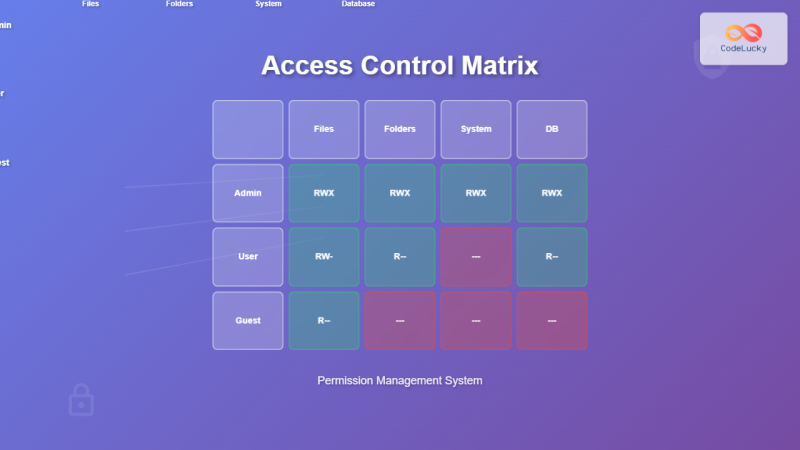
Access Control Matrix Comprehensive Guide To Permission Management Based on slides provided by matt bishop for use with computer security: art and science. plus hru examples from ravi sandhu. It describes common access control models like discretionary access control (dac), mandatory access control (mac), and role based access control (rbac). it also discusses access control terminology, technical processes, and best practices for implementing access controls. Access control matrix.ppt free download as powerpoint presentation (.ppt), pdf file (.pdf), text file (.txt) or view presentation slides online. the document discusses access control matrices and protection state transitions. Role based access control (rbac) matrix is an essential framework for managing user permissions and access rights within an organization. this model allows administrators to define roles based on job functions and assign permissions to those roles rather than to individual users.
Ppt Access Control Matrix Powerpoint Presentation Free Download Id Access control matrix.ppt free download as powerpoint presentation (.ppt), pdf file (.pdf), text file (.txt) or view presentation slides online. the document discusses access control matrices and protection state transitions. Role based access control (rbac) matrix is an essential framework for managing user permissions and access rights within an organization. this model allows administrators to define roles based on job functions and assign permissions to those roles rather than to individual users.
Comments are closed.