Access Control Matrix Explained A Beginners Guide To Operating System Security

Access Control Matrix 2 Pdf Dive into the world of access control matrices in this beginner friendly video! we break down this fundamental security model, explaining how it ensures only authorized users and. The access matrix is a foundational model for managing access control in operating systems, providing a clear framework for defining and enforcing security policies.

Security In Operating System Complete Guide To Access Control And Learn about access control matrix a fundamental security model for managing permissions in operating systems. discover implementation examples, advantages, and real world applications. An effective access control matrix ensures secure data management. check out these essential examples and templates to streamline your access control processes. Keeping track of who can access what, and how, quickly becomes complex. this is where the access control matrix steps in as a fundamental security model. it offers a clear, structured way to define, visualize, and manage permissions across an entire system. Learn what an access control matrix is, how it manages user permissions, and its role in security with components, implementations, and tips.
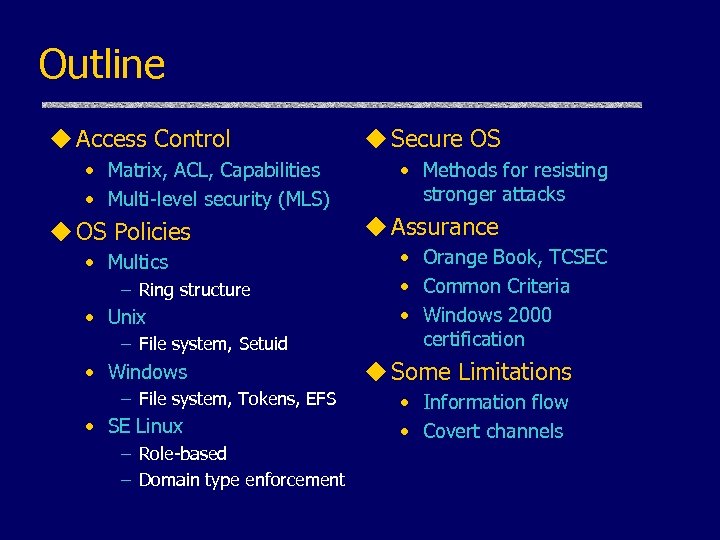
Access Control And Operating System Security John Mitchell Keeping track of who can access what, and how, quickly becomes complex. this is where the access control matrix steps in as a fundamental security model. it offers a clear, structured way to define, visualize, and manage permissions across an entire system. Learn what an access control matrix is, how it manages user permissions, and its role in security with components, implementations, and tips. In this post, we dive into what an acm is, when you need it, and how to create one. what is an access control matrix (acm)? an access control matrix (acm) is a security model that defines access rights by explicitly mapping who can perform which actions on which resources. Demystify the access control matrix and explore its core components, implementation models, and their applications for a robust cybersecurity framework. In our exploration of the access matrix in operating system, we will delve into its structure, access control mechanisms, and its pivotal role in maintaining system security and data integrity. Learn how access control matrices work and explore their structure, benefits, challenges, and real world use cases in cybersecurity and iam.
Comments are closed.