Access Control And Operating System Security John Mitchell
Access Control And Operating System Security John Mitchell Access control lists are widely used, often with groups some aspects of capability concept are used in kerberos,. Spring 2010 cs 155 control and access control operating system security john mitchell lecture goal: cover background and concepts used in android security model ieee security and privacy, jan. feb. 2009.

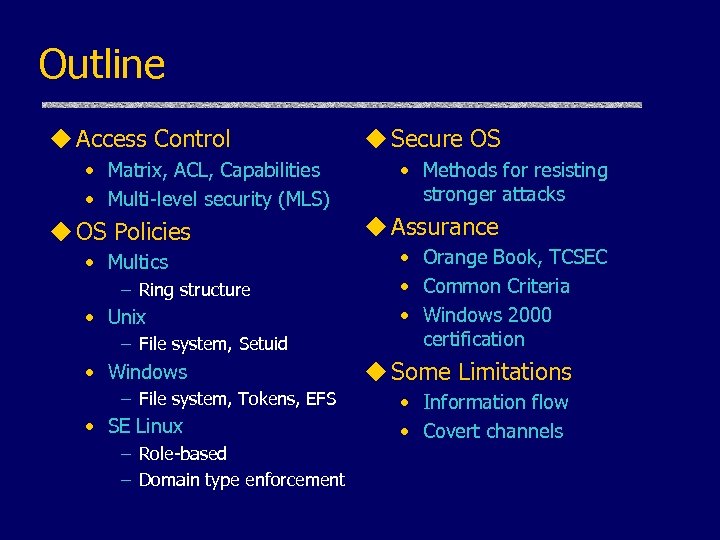
Security Computing 5 Access Control Pdf Access Control Computer Learning about such protection in operating systems provides a solid basis for understanding computer security. aside from unix, we base our discussion in large part on multics; its segmented virtual addressing, access control, and protection rings heavily influenced later systems. Role based access control • each process has an associated role – separate system and user processes • configuration files specify – set of domains that may be entered by each role. Access control and operating system security john mitchell outline access control matrix acl capabilities multi level security mls os policies multics ring str…. Outline (may not finish in one lecture) access control and operating ‹ access control concepts ‹ secure os system security • matrix, acl, capabilities • methods.

6 Os Security And Access Control Pdf Computer Access Control Access control and operating system security john mitchell outline access control matrix acl capabilities multi level security mls os policies multics ring str…. Outline (may not finish in one lecture) access control and operating ‹ access control concepts ‹ secure os system security • matrix, acl, capabilities • methods. This document outlines key concepts related to access control and operating system security. it discusses access control models like access control matrices, lists, and capabilities. This lecture discusses concepts related to operating system security, access control, and implementation attacks, exploring topics such as access control list (acl) vs. capabilities, role based access control, and multi level security. We discuss the types, methods, models, implementations, and best practices of operating system access control, providing a comprehensive overview of the subject matter. We then describe three popular protection structures called access control lists, capability lists, and protection domains, and examine the degree of control provided by them over sharing of files.
Comments are closed.