Access Android With Metasploit Kali Cybersecurity

How To Use Metasploit In Kali Linux A Step By Step Tutorial C Pdf This guide outlined essential steps for using metasploit to hack android devices, underscoring the importance of ethical practices in cybersecurity. the knowledge gained should be used responsibly to enhance security measures and contribute positively to the field of information technology. Kali linux: provides a comprehensive penetration testing environment equipped with security tools, including metasploit, for conducting vulnerability assessments and penetration testing.
Android Phone Access With Metasploit And Portmap Android Rat From Penetration testing, often conducted through open source frameworks like metasploit, simulates unauthorized access to identify vulnerabilities in both software and hardware. This study focuses on how someone could use the rapid7's metasploit 'msfvenom' framework to handle malicious apk files and access android devices by using phishing or social engineering. This guide walks through the full process of generating and delivering an android reverse shell payload using msfvenom and metasploit. from basic payload creation to advanced meterpreter interaction, the knowledge gained here is fundamental for android penetration testing in lab environments. Unlock the world of android hacking using kali linux with our step by step guide. learn to create a trojan .apk, set up a listener, and exploit android devices seamlessly.
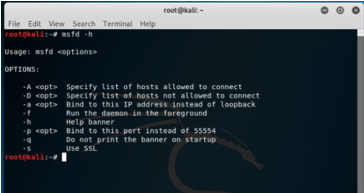
Kali Linux Metasploit How Kali Linux Metasploit Works This guide walks through the full process of generating and delivering an android reverse shell payload using msfvenom and metasploit. from basic payload creation to advanced meterpreter interaction, the knowledge gained here is fundamental for android penetration testing in lab environments. Unlock the world of android hacking using kali linux with our step by step guide. learn to create a trojan .apk, set up a listener, and exploit android devices seamlessly. Now, let’s start with the step by step guide on how to access an android phone remotely using kali linux: step 1: setting up the environment. the first step is to install the required tools on your kali linux system. this includes tools like adb (android debug bridge), metasploit, and a reverse tcp payload. The metasploit platform is used to break into android devices using tools developed by offensive security like msf. these tools can help students and professionals learn new things. Kali linux is a linux distro with a preset of hacking tools and frameworks that can serve multiple purposes in various phases of penetration testing. in this tutorial, we shall focus on metasploit android based payloads and msfvenom tool to create the apk file. In this article, we will explore how to access an android phone using kali linux and understand the various features and benefits this powerful open source penetration testing platform can offer.
Comments are closed.