About Saas Security Api Malware Detection Zscaler

Saas Attack Detection And Prevention Wit Pdf Cloud Computing Malware Saas security scan configuration allows you to schedule scans that use your saas security dlp and malware detection policies to inspect content in sanctioned saas applications. Saas security api ¶ the following methods allow for interaction with the zia saas security api endpoint resources. methods are accessible via zia.saas security api copyright (c) 2023, zscaler inc.
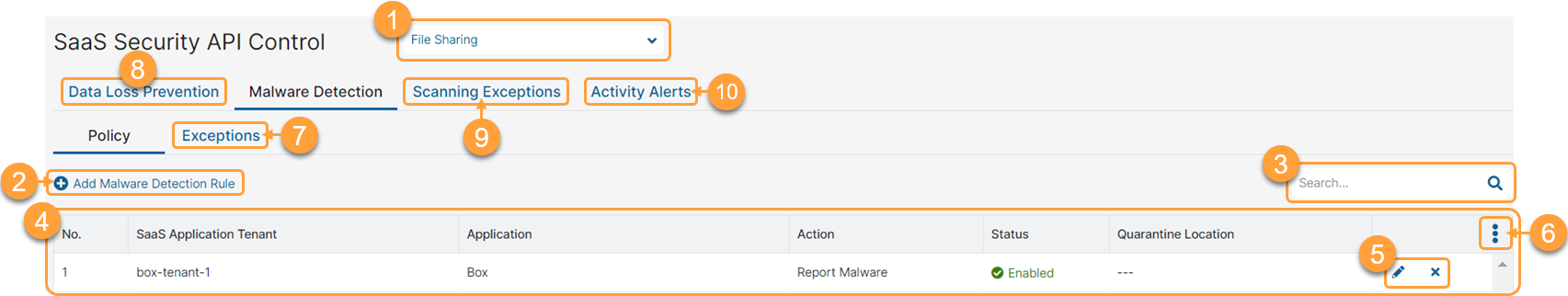
About Saas Security Api Malware Detection Zscaler The zscaler saas security api is designed to scan sanctioned saas applications for sensitive data at rest and remediate policy violations. a data loss prevention (dlp) rule within this service identifies files containing sensitive information (e.g., pii, financial data). It leverages web proxy logs to filter for blocked actions associated with malware, aggregating occurrences by user, url, and threat category. this detection is significant for soc as it highlights attempts to access malicious content, indicating potential compromise or targeted attacks. I’m working with my security team, who is requesting that the dlp and malware scanning saas api for zoom to be added, see article about adding zscaler to zoom article. Traditional network tools are inadequate for securing the use of saas applications. fortunately, zscaler’s multimode casb addresses the full breadth of cloud security use cases so that you can defend data at rest, protect data in motion, stop threats wherever they occur, and much more.

Saas Malware Detection Prevention Metaflows Detection Saas I’m working with my security team, who is requesting that the dlp and malware scanning saas api for zoom to be added, see article about adding zscaler to zoom article. Traditional network tools are inadequate for securing the use of saas applications. fortunately, zscaler’s multimode casb addresses the full breadth of cloud security use cases so that you can defend data at rest, protect data in motion, stop threats wherever they occur, and much more. Threat detection and response are essential elements of a successful cybersecurity strategy. zscaler’s logging features provide a variety of useful information that may be used to improve threat detection and response plans in a sase framework. Z insights provides visibility and analytics across web traffic, firewall, iot, saas security, shadow it, and cyber security domains via a graphql api. note: z insights only supports oneapi authentication. By providing inline inspection across all traffic, securing data at rest in cloud applications, extending protection to the endpoint, and leveraging ai for smarter detection, zscaler helps. How you can integrate zscaler’s security analytics and logging capabilities to optimize your policies to power your soc, including processes for preventing, logging, detecting, investigating, and mitigating threats.
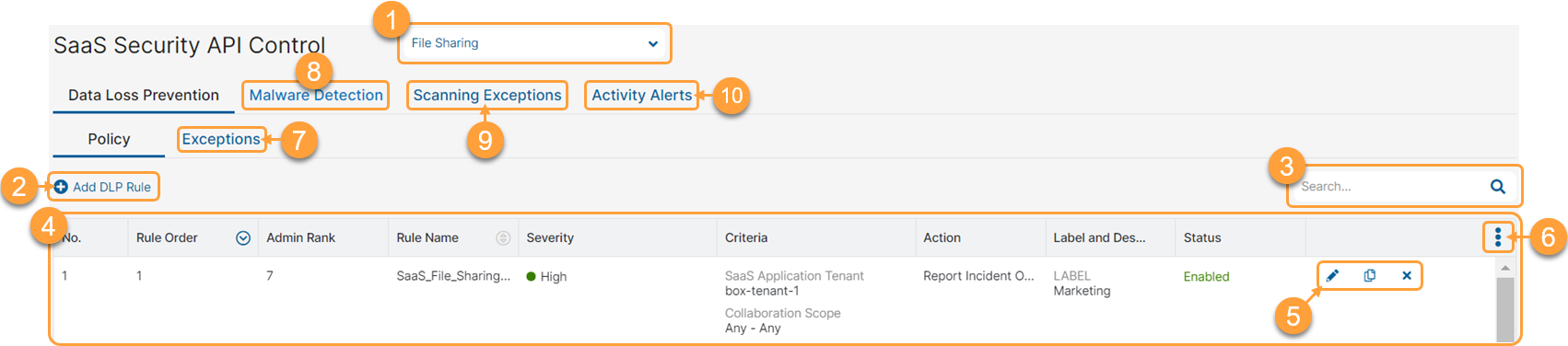
About Saas Security Api Dlp Zscaler Threat detection and response are essential elements of a successful cybersecurity strategy. zscaler’s logging features provide a variety of useful information that may be used to improve threat detection and response plans in a sase framework. Z insights provides visibility and analytics across web traffic, firewall, iot, saas security, shadow it, and cyber security domains via a graphql api. note: z insights only supports oneapi authentication. By providing inline inspection across all traffic, securing data at rest in cloud applications, extending protection to the endpoint, and leveraging ai for smarter detection, zscaler helps. How you can integrate zscaler’s security analytics and logging capabilities to optimize your policies to power your soc, including processes for preventing, logging, detecting, investigating, and mitigating threats.

Configuring Saas Security Api Scanning Exceptions Zscaler By providing inline inspection across all traffic, securing data at rest in cloud applications, extending protection to the endpoint, and leveraging ai for smarter detection, zscaler helps. How you can integrate zscaler’s security analytics and logging capabilities to optimize your policies to power your soc, including processes for preventing, logging, detecting, investigating, and mitigating threats.
Comments are closed.