A Step By Step Guide To Zero Trust Implementation

An Overview Of Zero Trust Study Guide Pdf Computer Network Zero trust is easy to understand, but hard to implement, as it requires architectural changes, not just technical controls. let’s understand step by how to implement zero trust in practice. Explore a step by step guide on implementing zero trust, covering deployment principles, challenges, and best practices for effective implementation.
How To Implement Zero Trust A Step By Step Guide Implementing a zero trust security model doesn't have to be intimidating. this guide covers each step of the process and tools to help maintain compliance. Our guide on how to implement zero trust security breaks down core principles, key components, and best practices for building a modern security framework. In this guide, we’ll break down everything you need to know about zero trust implementation, from core principles and architecture to step by step deployment and best practices. This e book presents a step by step guide to implementing a zero trust security posture while navigating the challenges and adopting the best practices throughout your organization.

A Step By Step Guide To Zero Trust Implementation In this guide, we’ll break down everything you need to know about zero trust implementation, from core principles and architecture to step by step deployment and best practices. This e book presents a step by step guide to implementing a zero trust security posture while navigating the challenges and adopting the best practices throughout your organization. As attackers become more sophisticated, companies need more powerful security. learn how to implement zero trust to keep operations secure. Zero trust implementation becomes practical when broken into clear, repeatable steps without trying to secure everything at once. this 6 step implementation plan and checklist helps organizations design zero trust architecture in a structured, low risk manner. This guide outlines a practical, tool enabled roadmap to help you move from strategy to implementation without starting from scratch or reinventing your stack. step 1: build a real inventory, not just an asset list. Learn how to implement zero trust security and the steps you need to take. understand why implementation involves a policy of never trusting and always verifying the authenticity and privileges of devices and users.
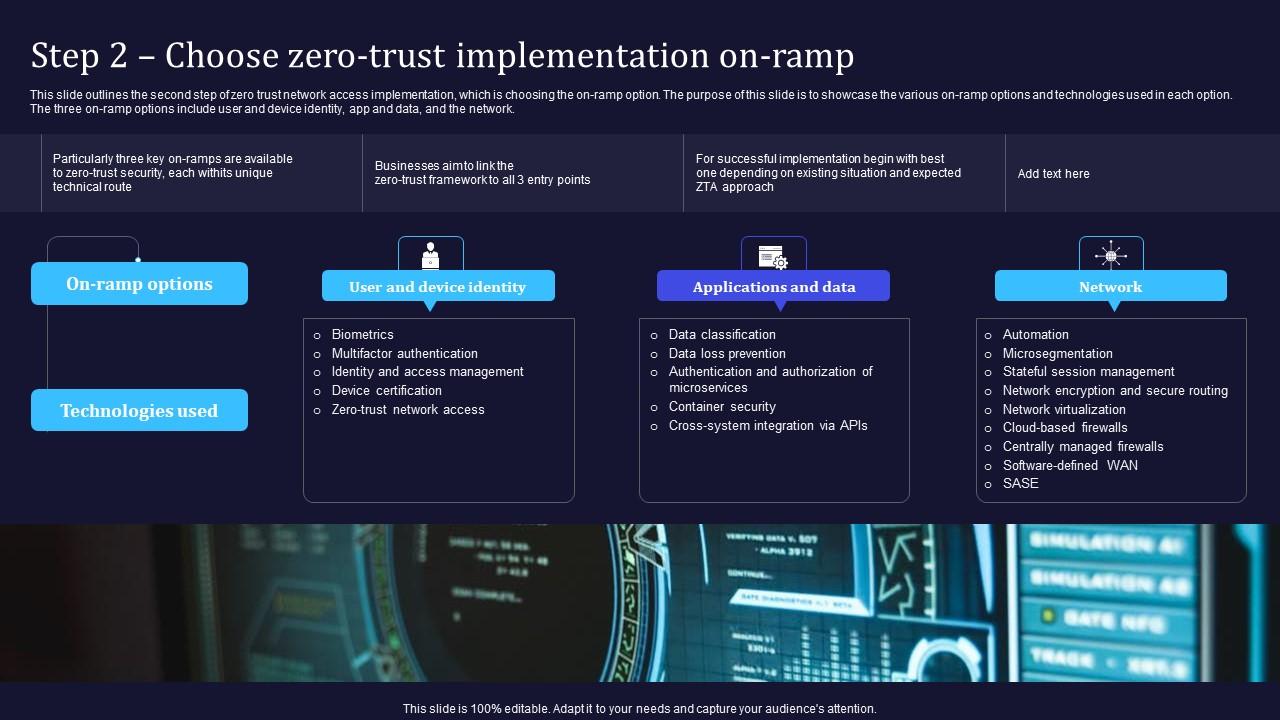
Zero Trust Model Step 2 Choose Zero Trust Implementation On Ramp As attackers become more sophisticated, companies need more powerful security. learn how to implement zero trust to keep operations secure. Zero trust implementation becomes practical when broken into clear, repeatable steps without trying to secure everything at once. this 6 step implementation plan and checklist helps organizations design zero trust architecture in a structured, low risk manner. This guide outlines a practical, tool enabled roadmap to help you move from strategy to implementation without starting from scratch or reinventing your stack. step 1: build a real inventory, not just an asset list. Learn how to implement zero trust security and the steps you need to take. understand why implementation involves a policy of never trusting and always verifying the authenticity and privileges of devices and users.
Practical Guide To Understanding And Implementing Zero Trust This guide outlines a practical, tool enabled roadmap to help you move from strategy to implementation without starting from scratch or reinventing your stack. step 1: build a real inventory, not just an asset list. Learn how to implement zero trust security and the steps you need to take. understand why implementation involves a policy of never trusting and always verifying the authenticity and privileges of devices and users.
Comments are closed.