A Practical Guide To Zero Trust Security Threatpost
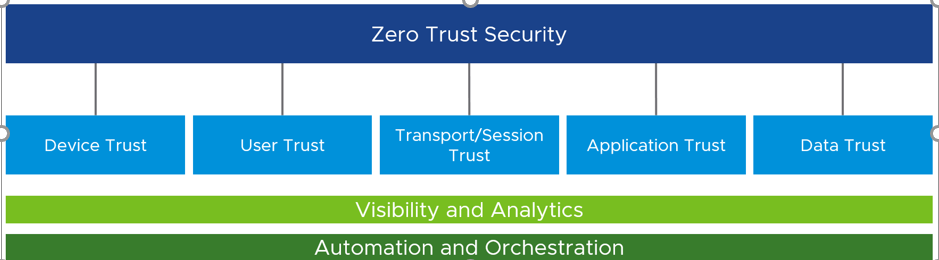
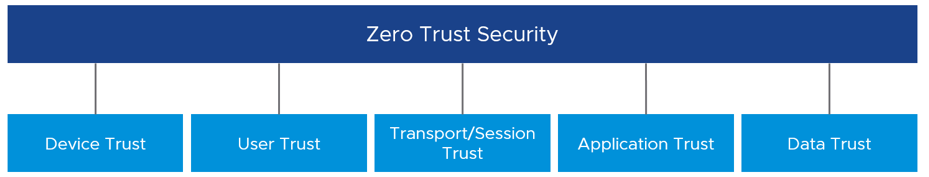
A Practical Guide To Zero Trust Security Threatpost There are five different pillars to implement when moving to a modern, zero trust security model. How to use zero trust architecture effectively in today’s modern cloud dependent infrastructures.
A Practical Guide To Zero Trust Security Threatpost Pair this “how to implement zero trust” guide with our expert led, ai driven managed services. talk to our experts today to see how we can help you achieve true cyber resilience with future proof security solutions. It’s not about buying security products! joseph carson, chief security scientist from thycoticcentrify, offers practical steps to start the zero trust journey. Learn the zero trust security model, its 3 core pillars, and how to implement it step by step using microsoft's framework to protect your business in 2026. Small and medium enterprises (sme) face a growing number of threats in today’s digital world. one of the most efective approaches to protecting critical resources and information is implementing the principles of zero trust in the company’s security architecture.

A Practical Guide To Zero Trust Security Threatpost Learn the zero trust security model, its 3 core pillars, and how to implement it step by step using microsoft's framework to protect your business in 2026. Small and medium enterprises (sme) face a growing number of threats in today’s digital world. one of the most efective approaches to protecting critical resources and information is implementing the principles of zero trust in the company’s security architecture. Take the first step toward a resilient identity security posture and download the complete guide to building an identity protection strategy to protect your organization’s digital identity landscape today. zero trust is a broad concept, and its implementation can vary. In this guide, we will explore the core principles of zero trust, its benefits, and a step by step approach to implementing it in different organizational settings. zero trust is a security model based on the principle of “never trust, always verify.”. Security leaders should read this report to understand the practical building blocks of a successful zero trust implementation roadmap. To move from concept to execution, security teams need more than guiding principles. they need practical steps: granular access controls, continuous verification, proactive hardening, all without slowing down business operations. so how do organizations turn zero trust from aspiration into action?.

Zero Trust Security A Hands On Guide Take the first step toward a resilient identity security posture and download the complete guide to building an identity protection strategy to protect your organization’s digital identity landscape today. zero trust is a broad concept, and its implementation can vary. In this guide, we will explore the core principles of zero trust, its benefits, and a step by step approach to implementing it in different organizational settings. zero trust is a security model based on the principle of “never trust, always verify.”. Security leaders should read this report to understand the practical building blocks of a successful zero trust implementation roadmap. To move from concept to execution, security teams need more than guiding principles. they need practical steps: granular access controls, continuous verification, proactive hardening, all without slowing down business operations. so how do organizations turn zero trust from aspiration into action?.
Comments are closed.