A Malicious Encrypted Traffic Before Refinement Processing B
User Added Image The detection of malicious encrypted traffic is an important part of modern network security research. In this paper, we propose a maliciously encrypted traffic detection method based on multi granularity representation under data imbalance conditions.
Url Category Object With more and more encrypted traffic such as https, encrypted traffic protects not only normal traffic, but also malicious traffic. identification of encrypted. Encrypted traffic can obscure important information, making it difficult to detect malicious activities or classify network traffic accurately. therefore, understanding statistical techniques for analyzing encrypted traffic and detecting abnormalities becomes crucial in ensuring network security. Filter out all non encrypted traffic sessions in the mixed traffic dataset. (this ensures that there are no non encrypted traffic sessions at the session level that will affect the encrypted traffic analysis.). The results show transgraphnet’s strong robustness against malicious encrypted traffic with obfuscation, while also validating the effectiveness of the improved pld algorithm in processing time series.
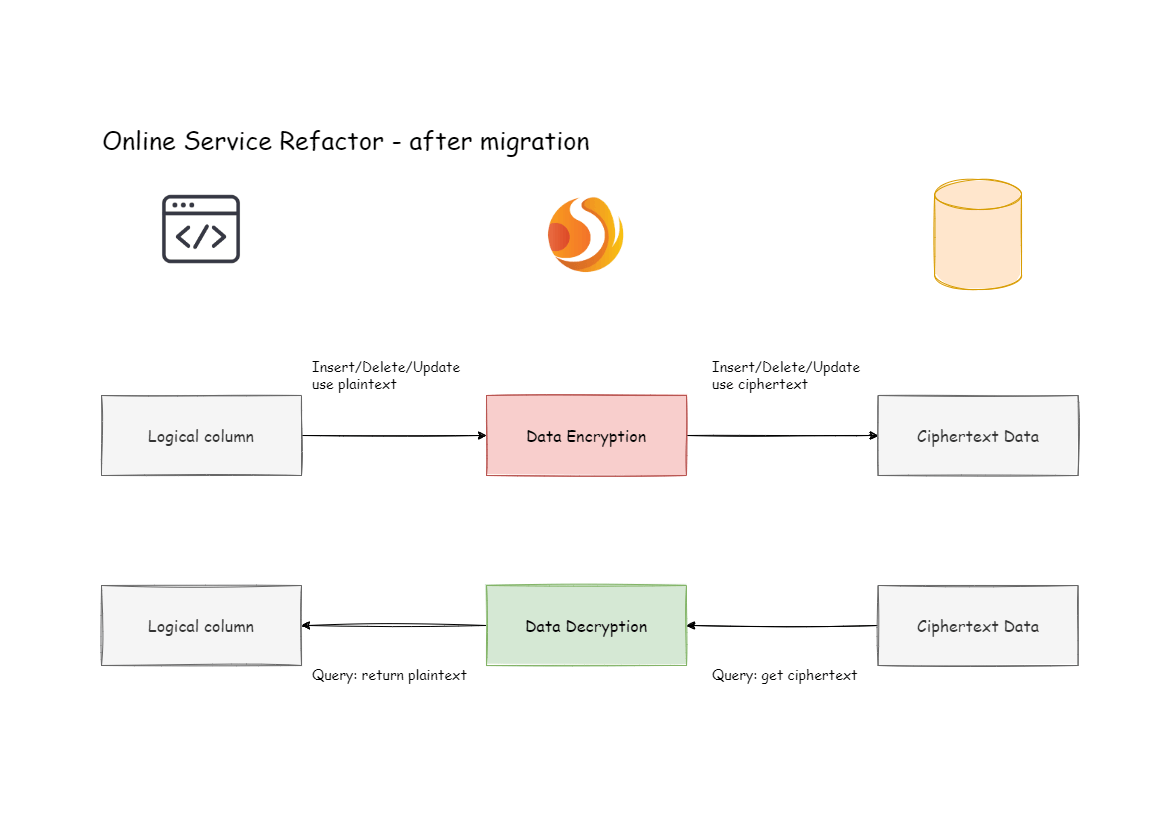
Encryption Shardingsphere Filter out all non encrypted traffic sessions in the mixed traffic dataset. (this ensures that there are no non encrypted traffic sessions at the session level that will affect the encrypted traffic analysis.). The results show transgraphnet’s strong robustness against malicious encrypted traffic with obfuscation, while also validating the effectiveness of the improved pld algorithm in processing time series. Keywords: encrypted attack traffic detection, en bert, pre training phase, data enhancement, weighted cross entropy, k l divergence. In order to solve these challenges, this paper proposes an encrypted traffic anomaly detection using self supervised contrastive learning (et ssl), a novel framework that detects anomalies in. Encrypted traffic can obscure important information, making it difficult to detect malicious activities or classify network traffic accurately. therefore, understanding statistical techniques for analyzing encrypted traffic and detecting abnormalities becomes crucial in ensuring network security. In recent years, the rise of artificial intelligence allows us to use machine learning and deep learning methods to detect encrypted malicious traffic without decryption, and the detection results are very accurate.
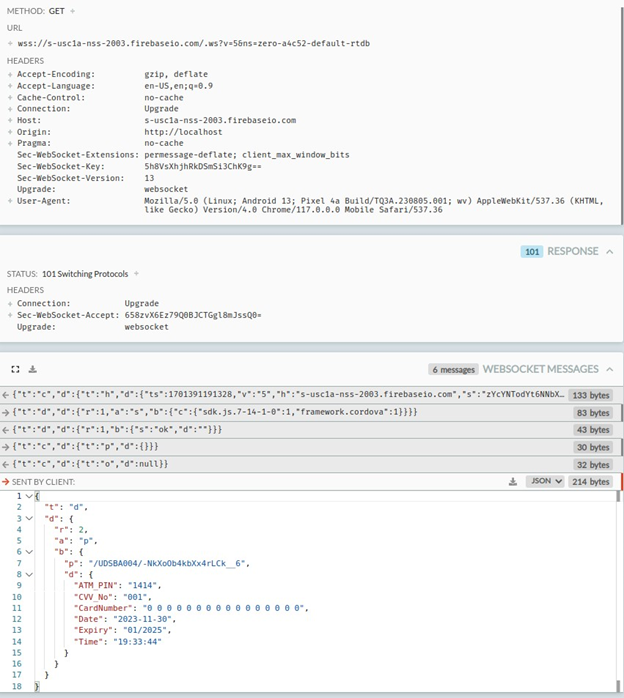
Shielding Against Android Phishing In Indian Banking Mcafee Blog Keywords: encrypted attack traffic detection, en bert, pre training phase, data enhancement, weighted cross entropy, k l divergence. In order to solve these challenges, this paper proposes an encrypted traffic anomaly detection using self supervised contrastive learning (et ssl), a novel framework that detects anomalies in. Encrypted traffic can obscure important information, making it difficult to detect malicious activities or classify network traffic accurately. therefore, understanding statistical techniques for analyzing encrypted traffic and detecting abnormalities becomes crucial in ensuring network security. In recent years, the rise of artificial intelligence allows us to use machine learning and deep learning methods to detect encrypted malicious traffic without decryption, and the detection results are very accurate.

Encrypted Traffic Decryption Tools Comparative Performance Analysis Encrypted traffic can obscure important information, making it difficult to detect malicious activities or classify network traffic accurately. therefore, understanding statistical techniques for analyzing encrypted traffic and detecting abnormalities becomes crucial in ensuring network security. In recent years, the rise of artificial intelligence allows us to use machine learning and deep learning methods to detect encrypted malicious traffic without decryption, and the detection results are very accurate.
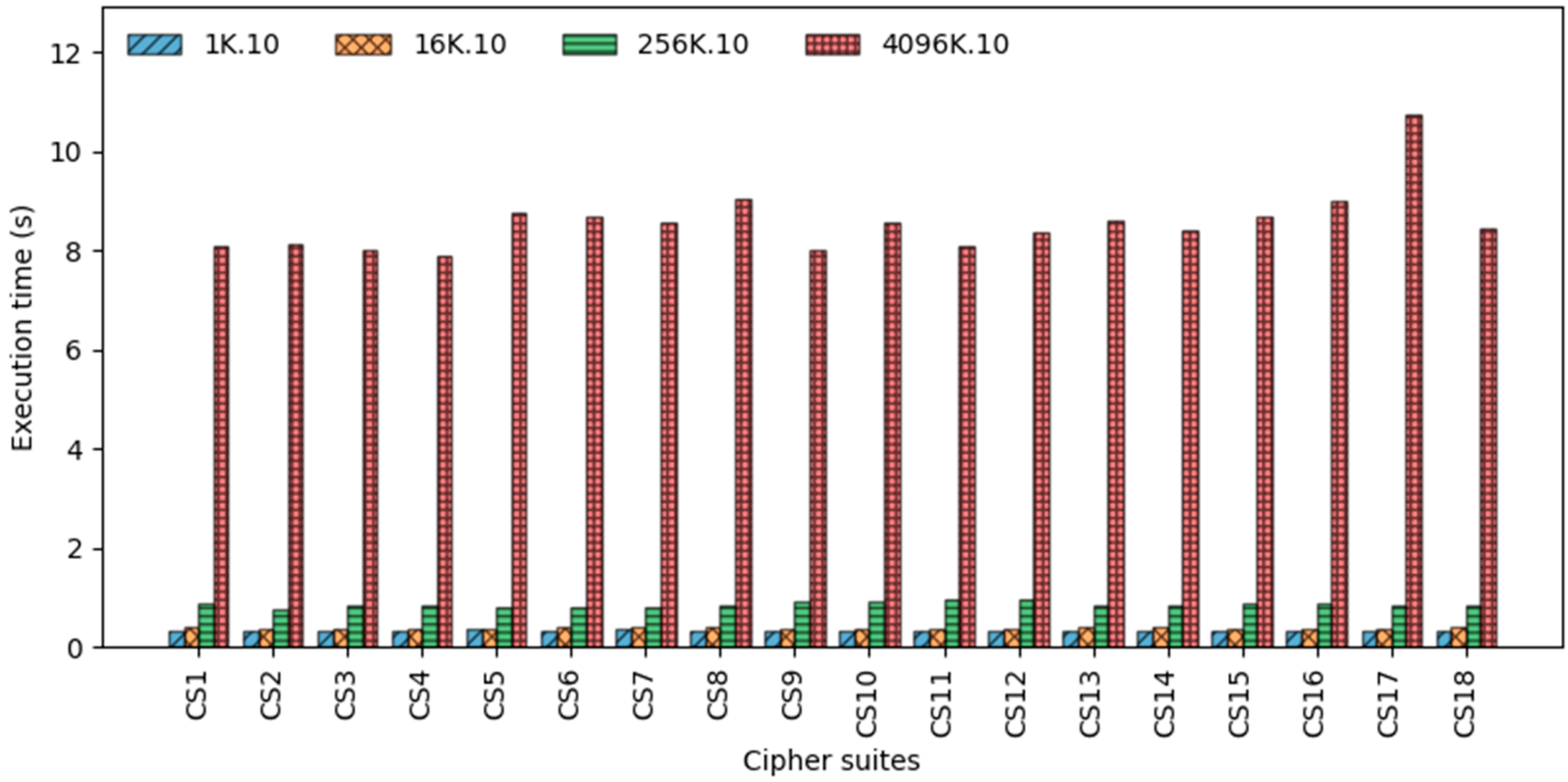
Encrypted Traffic Decryption Tools Comparative Performance Analysis
Comments are closed.