A Developers Guide To Iot Encryption Algorithms
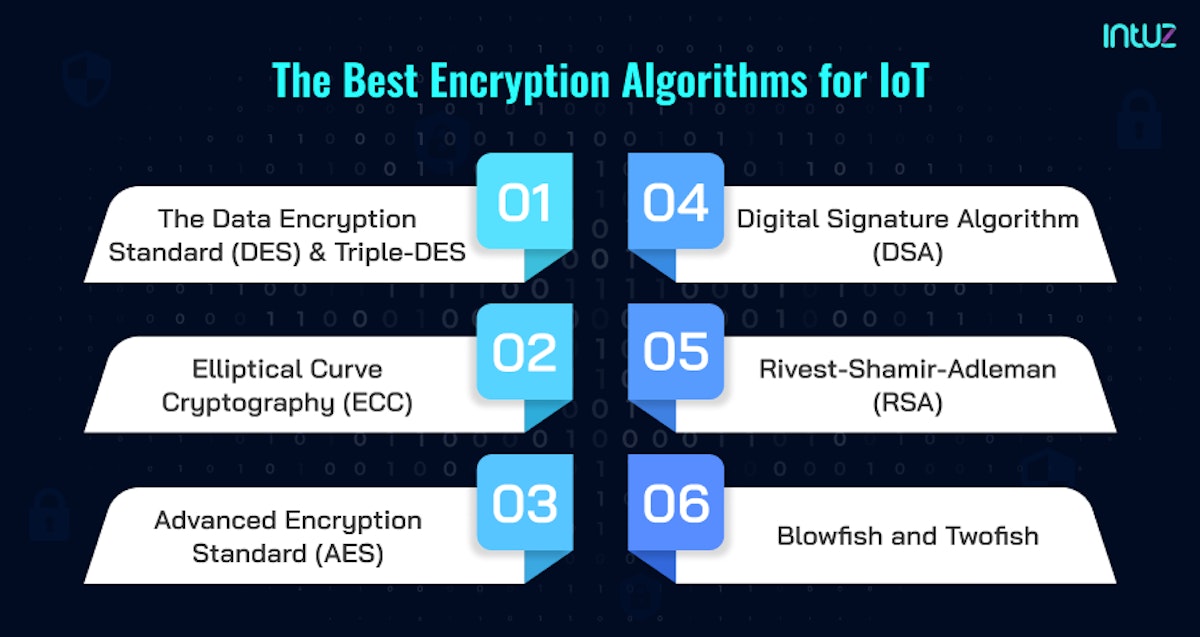
Securing The Iot Data Landscape Iot Encryption Algorithms Intuz Check out our guide to iot encryption algorithms where we cover different types of encryption and the most common iot encryption methods. This survey paper introduced an overview of iot technology, architecture, and applications and a detailed analysis comparing all cryptographic algorithms and their use in day to day life activities. this paper discusses lightweight block ciphers, stream ciphers, and hybrid ciphers.

Securing The Iot Data Landscape Iot Encryption Algorithms Intuz For example, developers can use cryptographic transport layer security protocol which encrypts the data to ensure that information remains secured and confidential. this confidentiality allows only the intended recipient to unlock the message and access the information. The exponential growth of the internet of things (iot) has increased the demand for robust security solutions that are tailored to devices with limited resources. this paper presents a systematic review of recent literature on lightweight encryption algorithms designed to meet this challenge. Our project focuses on delving into this domain by investigating an iot network that ensures the security of data through the utilization of widely recognized cryptographic algorithms, including aes, rsa, and blowfish. By synthesizing design principles, performance optimizations, and standardization frameworks, this survey offers system architects and developers a unified reference for selecting and deploying lightweight cryptographic primitives in practical iot applications.

Securing The Iot Data Landscape Iot Encryption Algorithms Intuz Our project focuses on delving into this domain by investigating an iot network that ensures the security of data through the utilization of widely recognized cryptographic algorithms, including aes, rsa, and blowfish. By synthesizing design principles, performance optimizations, and standardization frameworks, this survey offers system architects and developers a unified reference for selecting and deploying lightweight cryptographic primitives in practical iot applications. In such a manner, the paper intends to understand the current impact of cryptographic algorithms to evaluate the security and privacy offered using a combination of algorithms and specific boards. Zachary amos, editor of rehack magazine shares the five best encryption methods for iot devices to safeguard them against cyber threats. Overall, this article aspires to serve as a reference point and guide, particularly from a technical standpoint, for cybersecurity experts and researchers working in the context of iot. This study explores the key considerations and methodologies involved in developing encryption algorithms suitable for iot devices. the proliferation of iot (internet of things) devices has revolutionized numerous industries, offering unprecedented connectivity and data insights.
Comments are closed.