A Developer Guide To Reporting Vulnerabilities Okta Developer
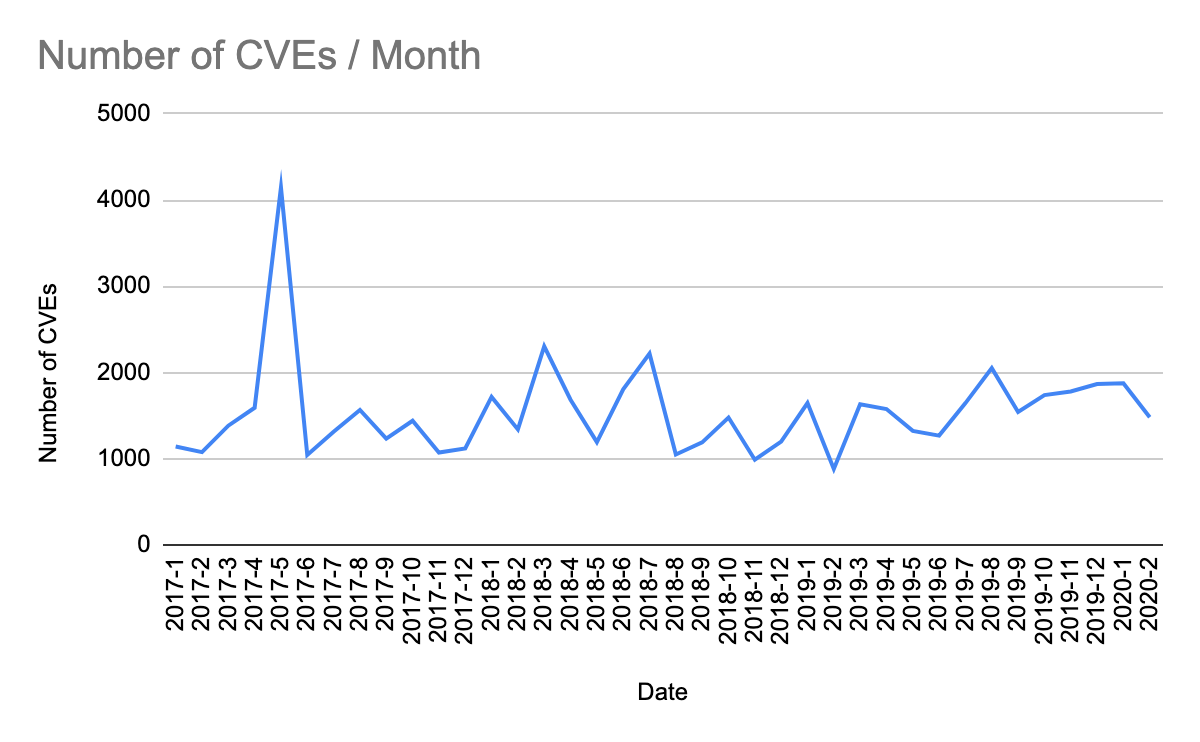
A Developer Guide To Reporting Vulnerabilities Okta Developer A developer guide to reporting vulnerabilities this post explains how to report a vulnerability and why it’s important to do so responsibly. In this video, you will learn how to report vulnerabilities and why they are handled differently than regular bugs.
A Developer Guide To Reporting Vulnerabilities Okta Developer This document covers the structured processes for reporting bugs, requesting features, and obtaining support for the @okta okta angular sdk. it details the github issue templates, support channels, and security reporting procedures available to users and contributors. The okta developer site serves okta's api documentation and guides, including: to build the site on your machine and or to contribute content to the site, view the instructions for getting set up. if you run into issues, view the instructions for troubleshooting. With this knowledge, you’ll be prepared to conduct your own research and publish vulnerabilities. this book is for security analysts, researchers, penetration testers, software developers, it engineers, and anyone who wants to learn how vulnerabilities are found and then disclosed to the public. Infosecurity has outlined the fundamental steps ethical hackers, independent researchers and other cybersecurity professionals need to take to responsibly disclose and report a vulnerability, as well as how patching processes work.
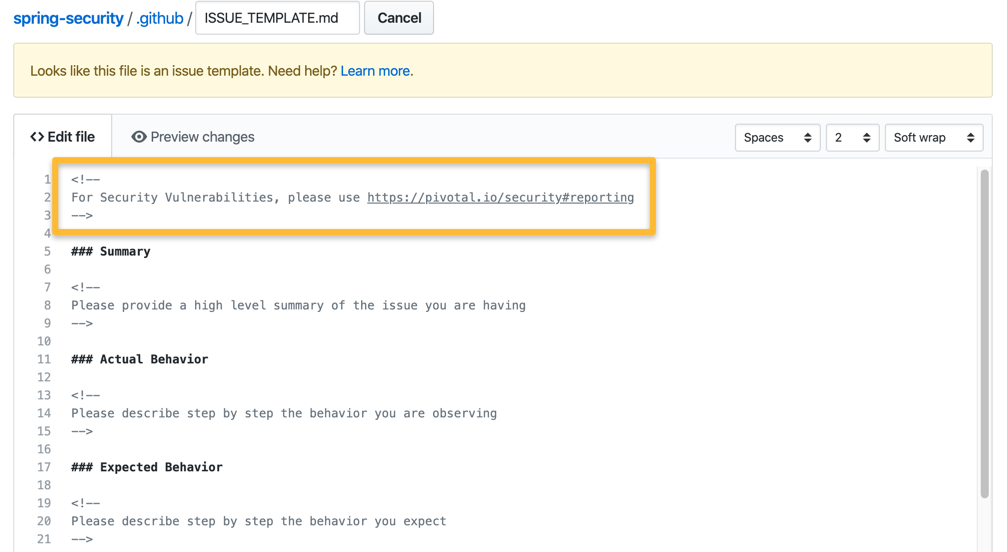
A Developer Guide To Reporting Vulnerabilities Okta Developer With this knowledge, you’ll be prepared to conduct your own research and publish vulnerabilities. this book is for security analysts, researchers, penetration testers, software developers, it engineers, and anyone who wants to learn how vulnerabilities are found and then disclosed to the public. Infosecurity has outlined the fundamental steps ethical hackers, independent researchers and other cybersecurity professionals need to take to responsibly disclose and report a vulnerability, as well as how patching processes work. We ask that you write clear and concise reports to enable us to make a determination. make sure to include your methodology, step by step instructions, and only submit after you verify your bug. Recorded at aws re:invent 2023, learn how okta uses snyk to simplify security complexity for auth0 developers. With an active directory security audit, spot threats before attackers do. find ad, entra id, and okta security gaps with purple knight. perform a comprehensive set of tests against the most common and effective attack vectors to find risky configurations and security vulnerabilities. Learn how to avoid conflict when you approach a company and report a vulnerability you found as a security researcher.

Okta Vulnerability Disclosure Policy Pdf Vulnerability Computing We ask that you write clear and concise reports to enable us to make a determination. make sure to include your methodology, step by step instructions, and only submit after you verify your bug. Recorded at aws re:invent 2023, learn how okta uses snyk to simplify security complexity for auth0 developers. With an active directory security audit, spot threats before attackers do. find ad, entra id, and okta security gaps with purple knight. perform a comprehensive set of tests against the most common and effective attack vectors to find risky configurations and security vulnerabilities. Learn how to avoid conflict when you approach a company and report a vulnerability you found as a security researcher.
Comments are closed.