A Complete Guide To Biometric Authentication Methods Ondato Blog

Authentication Methods From Passwords To Biometrics Ondato Discover biometric authentication methods, from fingerprints to iris scans. learn types, examples, and devices shaping biometric technology today. See how different authentication methods work, including mfa, biometrics, and passwordless logins, to protect users and data.
A Complete Guide To Biometric Authentication Methods Ondato Blog This article covers everything about biometric authentication in ciam, including types like fingerprint and facial recognition, and how it stacks up against other methods. we'll explore implementation strategies, security considerations (like spoofing), and compliance needs (gdpr, ccpa). Biometric data is a unique identifier of each person. let's take a closer look at types of biometric authentication, examples and frequently asked questions. This comprehensive guide examines how these advanced systems operate, their key advantages, and practical implementation strategies. learn about different biometric modalities, fusion techniques, industry applications, and best practices for deployment. Discover biometric authentication methods, from fingerprints and facial recognition to behavioral analytics, and learn how to secure digital platforms.
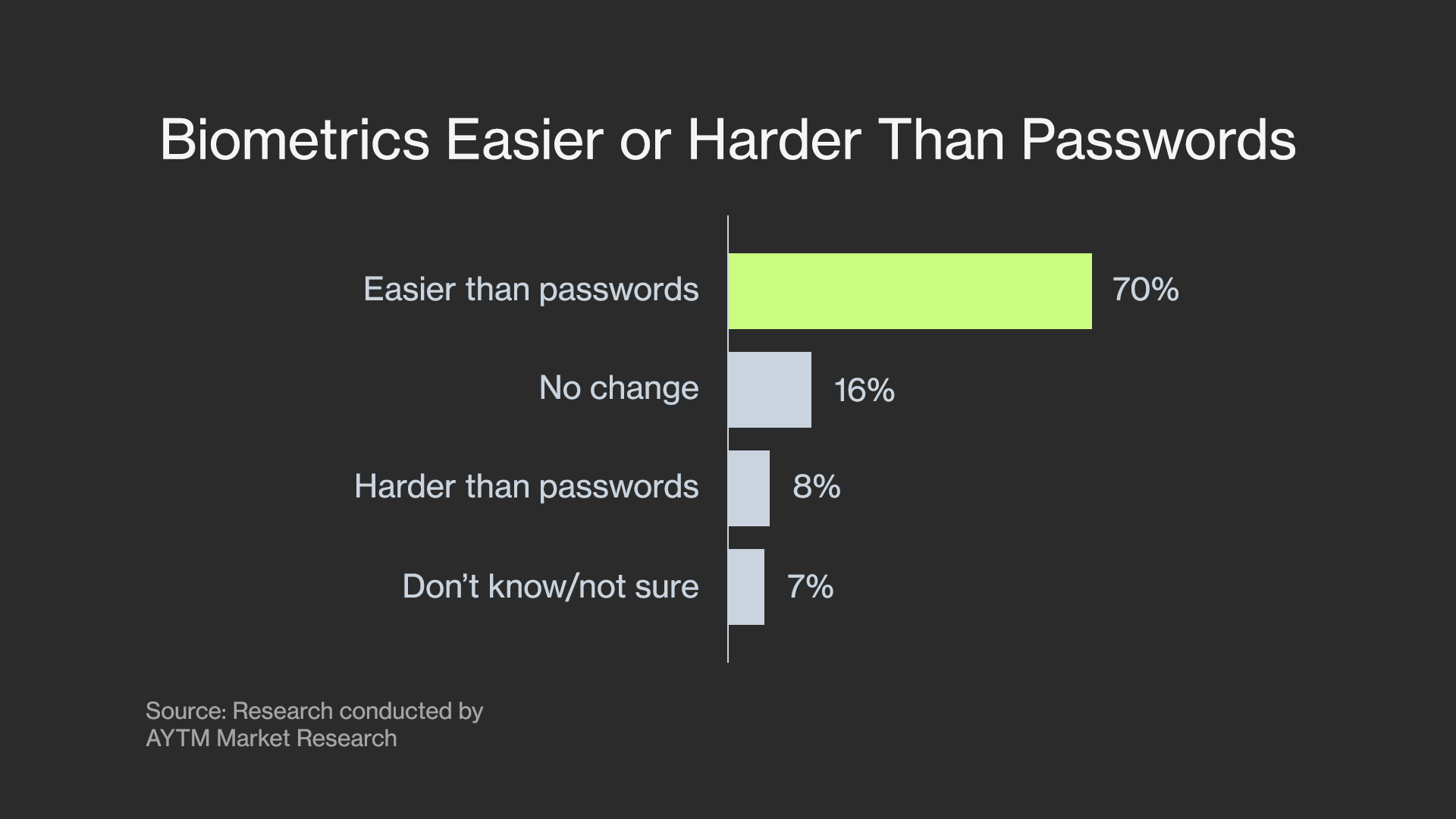
A Complete Guide To Biometric Authentication Methods Ondato Blog This comprehensive guide examines how these advanced systems operate, their key advantages, and practical implementation strategies. learn about different biometric modalities, fusion techniques, industry applications, and best practices for deployment. Discover biometric authentication methods, from fingerprints and facial recognition to behavioral analytics, and learn how to secure digital platforms. This comprehensive guide explores the latest trends, technologies, and implementation strategies for biometric systems, providing it security professionals and digital transformation leaders with essential insights for selecting and deploying the right biometric solution. In this guide, we’ll explore the different types of biometric authentication methods, compare them with passwords, and discuss use cases where these technologies are making a difference. Explore how biometric authentication works, the pros and cons of local, centralized, and decentralized systems, and how zero knowledge biometrics™ delivers privacy, security, and scalability. In this blog, we’ll explore what biometric authentication is, how it works, its various types, methods, examples, and its role in cybersecurity and network security. we’ll also discuss its advantages, challenges, and how artificial intelligence (ai) is shaping the future of biometric systems.
Comments are closed.