8 Build A System Credentials
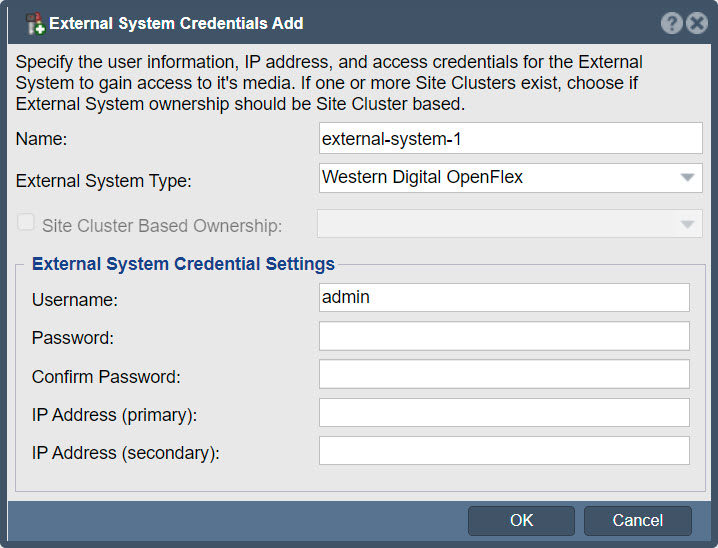
File External System Credentials Add Jpg Osnexus Online Documentation In this episode, we cover how to choose the right credentials for your system and why compatibility with your reader technology matters. Keeping digital information secure is like building a strong foundation, and a well designed security system is essential for protecting it. this article explains how to design a robust security system step by step, starting from defining goals to implementing scalable architecture.
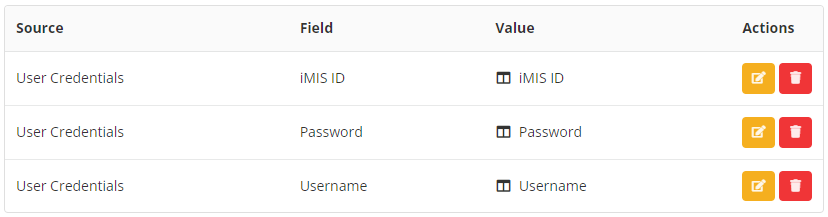
Credentials Tutorial In this article, we've covered how to read, write, update, and delete credentials using the credential manager in 8. this approach ensures that sensitive information is stored securely, leveraging the built in capabilities of the windows operating system. Credentials are an effective way to pass parameters into services that run with rootimage= or rootdirectory= and thus cannot read these resources directly from the host directory tree. specifically, portable services may be parameterized this way securely and robustly. This document provides a guide for credential providers on integrating with the android 14 credential manager api, detailing the setup, handling of credential creation and sign in requests for passkeys and passwords, and managing provider settings. This sample shows how credentials can be used when publishing artifacts to a maven repository using project properties. this approach allows you to keep sensitive configuration out of your project’s source code and inject it only when needed.
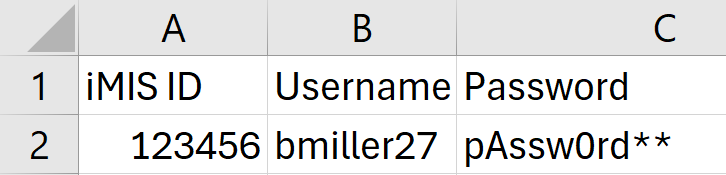
Credentials Tutorial This document provides a guide for credential providers on integrating with the android 14 credential manager api, detailing the setup, handling of credential creation and sign in requests for passkeys and passwords, and managing provider settings. This sample shows how credentials can be used when publishing artifacts to a maven repository using project properties. this approach allows you to keep sensitive configuration out of your project’s source code and inject it only when needed. Demonstrates how to build a v2 credential provider that makes use of the new capabilities in credential provider framework in windows 8 and windows 8.1. To build a functional and trustworthy verifiable credentials (vc) system, you need four core components working together. think of these as the foundational pillars that ensure every credential is secure, verifiable, and user controlled. In this article you'll find insights and solutions to enhance security protocols and streamline credential management in your company. Master the art of managing credentials in powershell effortlessly. this concise guide unveils key methods and tips for secure handling.
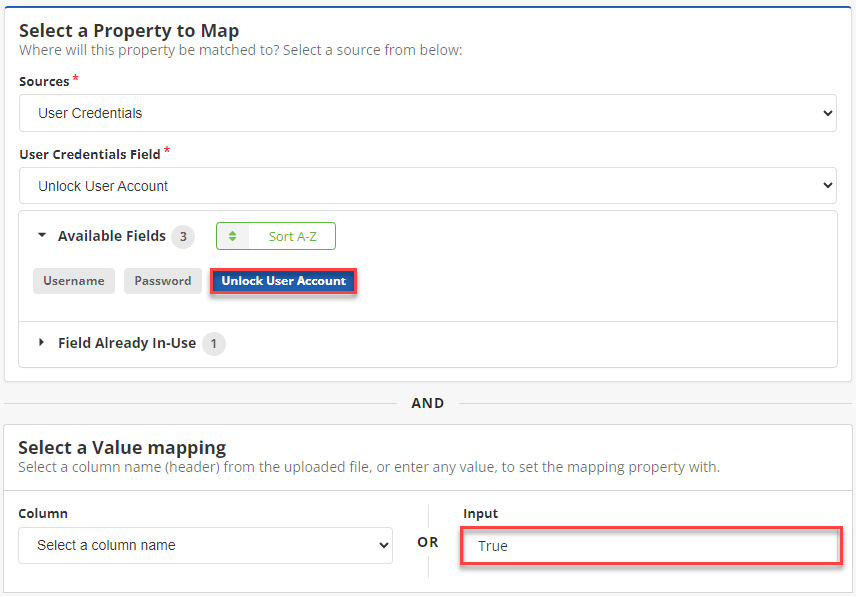
Credentials Tutorial Demonstrates how to build a v2 credential provider that makes use of the new capabilities in credential provider framework in windows 8 and windows 8.1. To build a functional and trustworthy verifiable credentials (vc) system, you need four core components working together. think of these as the foundational pillars that ensure every credential is secure, verifiable, and user controlled. In this article you'll find insights and solutions to enhance security protocols and streamline credential management in your company. Master the art of managing credentials in powershell effortlessly. this concise guide unveils key methods and tips for secure handling.
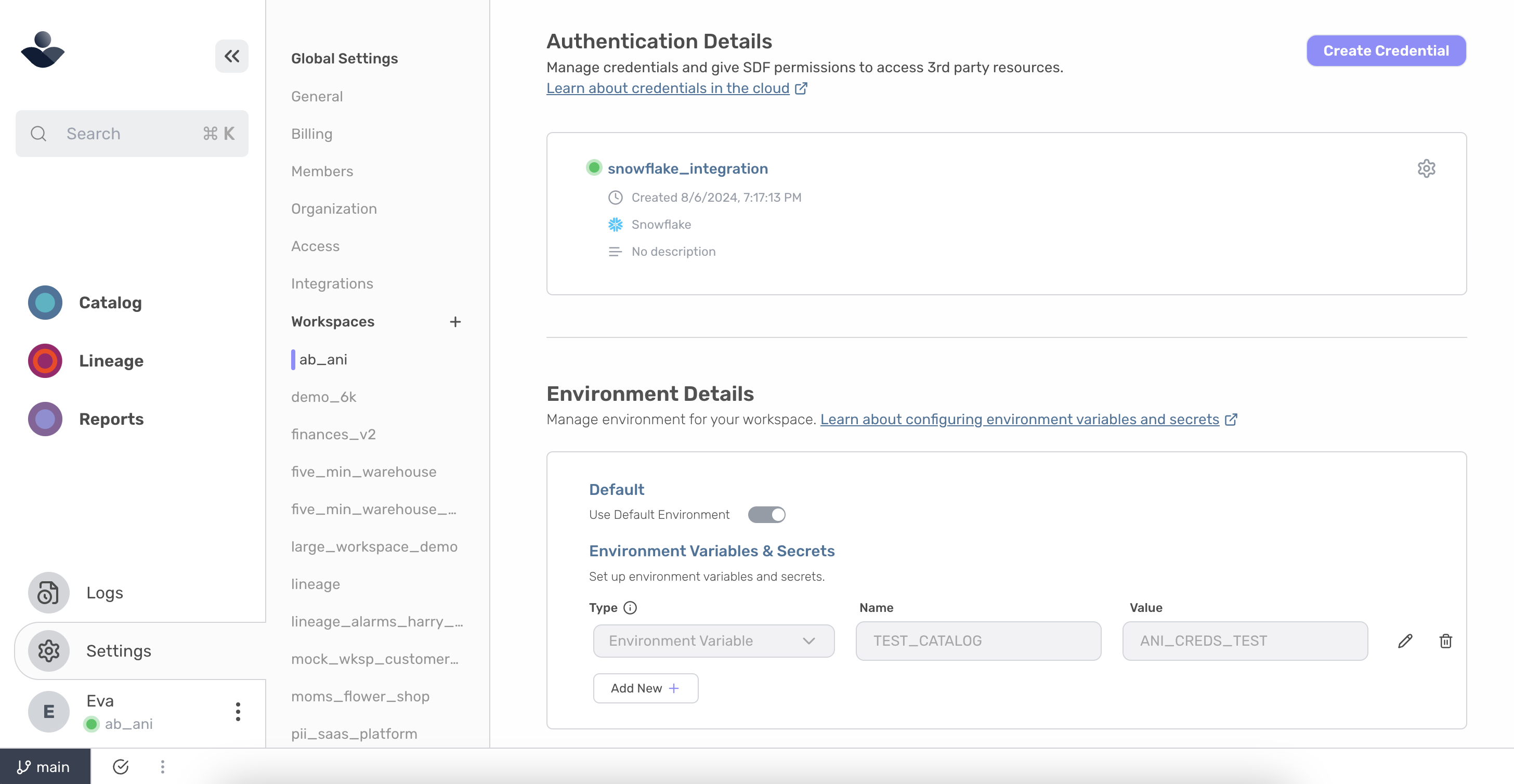
Adding Workspace Credentials Sdf In this article you'll find insights and solutions to enhance security protocols and streamline credential management in your company. Master the art of managing credentials in powershell effortlessly. this concise guide unveils key methods and tips for secure handling.
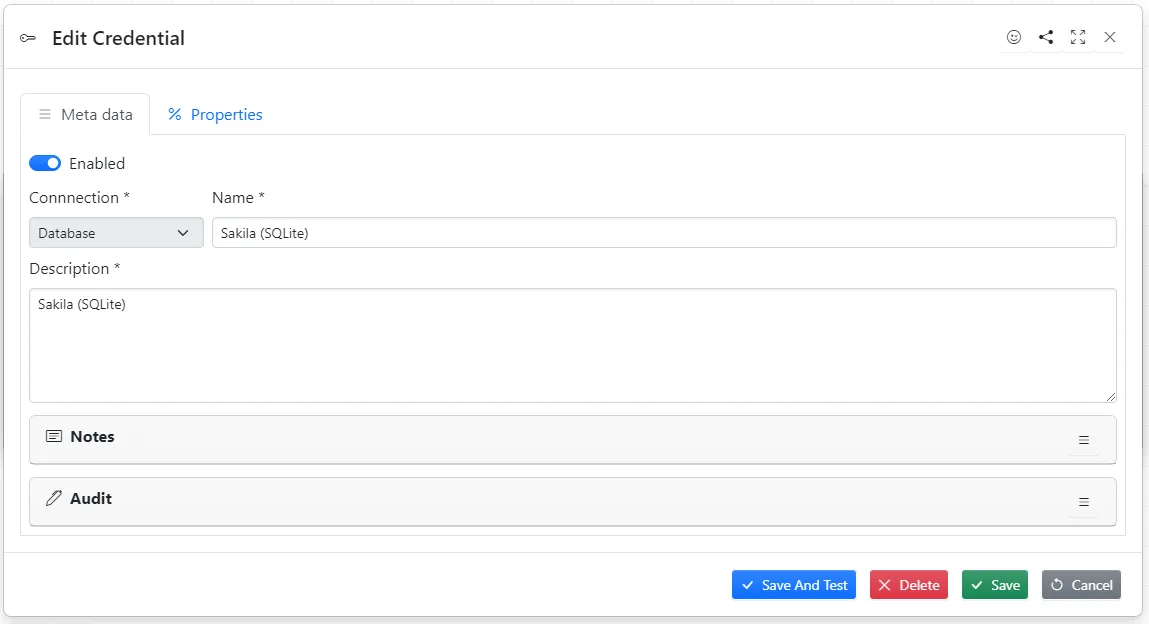
Creating Credentials
Comments are closed.