7 4 Recommended Controls

Recommended Controls Powerpoint Templates Slides And Graphics A full list of the iso 27001 controls from annex a, each with a detailed explanation of how to meet it. Access the full list of 93 iso 27001:2022 annex a controls. a complete reference guide organised by the 4 new themes: organisational, people, physical, and tech.
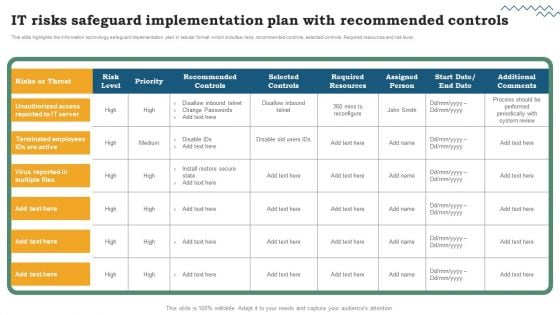
Recommended Controls Powerpoint Templates Slides And Graphics To comply with iso 27001 control 7.4, your organization should implement comprehensive security monitoring measures. these measures should cover all aspects of physical security, including surveillance, access control, alarm systems, and real time incident detection. Iso 27002:2022 introduces several new information security controls including a7.4 –physical security monitoring. this blog takes a brief look at what is required. Compliance with iso 27001 annex a 7.4 requires organizations to diligently adhere to the recommended practices and controls. conducting regular audits and assessments is essential to ensure compliance and identify areas for improvement. This is the fourth of five videos exploring chapter 7 of wheeler's most excellent book on security risk management.table of contents: 00:00 composite servi.
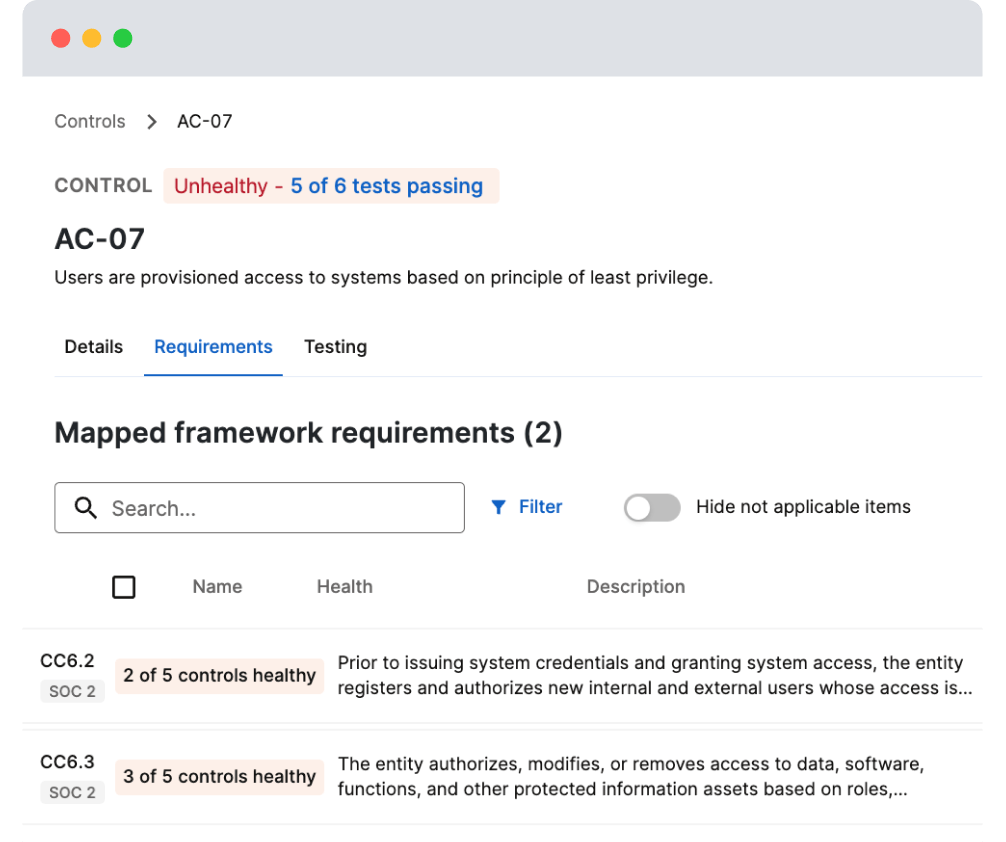
Controls Compliance with iso 27001 annex a 7.4 requires organizations to diligently adhere to the recommended practices and controls. conducting regular audits and assessments is essential to ensure compliance and identify areas for improvement. This is the fourth of five videos exploring chapter 7 of wheeler's most excellent book on security risk management.table of contents: 00:00 composite servi. This section describes 14 controls related to protection of physical environment that can influence security of information:. What does control 7.4 mean? this control focuses on continuous physical surveillance to detect and deter unauthorized access to facilities. Outlined in annex a of the iso 27001 standard, these controls are categorized into four key themes: organizational, physical, people, and technological. they cover a wide range of security areas, such as access management, encryption, physical protection, and incident response. Provisioning capabilities of midpoint, together with role based access control (rbac) policies can be used to grant access to monitoring and alarms systems to appropriate personnel.
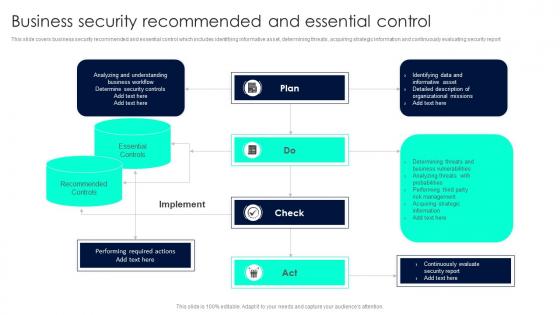
Recommended Controls Powerpoint Presentation And Slides Ppt Template This section describes 14 controls related to protection of physical environment that can influence security of information:. What does control 7.4 mean? this control focuses on continuous physical surveillance to detect and deter unauthorized access to facilities. Outlined in annex a of the iso 27001 standard, these controls are categorized into four key themes: organizational, physical, people, and technological. they cover a wide range of security areas, such as access management, encryption, physical protection, and incident response. Provisioning capabilities of midpoint, together with role based access control (rbac) policies can be used to grant access to monitoring and alarms systems to appropriate personnel.

Development Controls In Architecture Pdf Outlined in annex a of the iso 27001 standard, these controls are categorized into four key themes: organizational, physical, people, and technological. they cover a wide range of security areas, such as access management, encryption, physical protection, and incident response. Provisioning capabilities of midpoint, together with role based access control (rbac) policies can be used to grant access to monitoring and alarms systems to appropriate personnel.

Chapter 7 Tp7 Pdf Version Control Specification Technical Standard
Comments are closed.