7 2 7 Scan For Ftp Vulnerabilities

Reported Known Ftp Vulnerabilities Download Table 40 subscribers 14 1.7k views 4 months ago this video provides a solution for lab work 7.2.7 scan for ftp vulnerabilities more. Automated vulnerability scanners, such as nessus or openvas, can perform automated checks for known ftp vulnerabilities. these tools provide a baseline assessment, but their findings need to be validated through manual verification.
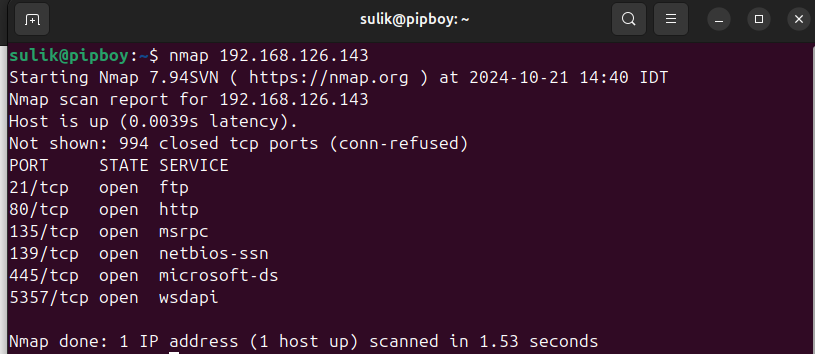
Exploiting Ftp Vulnerabilities On Metasploitable 2 By Josegpac Medium To access this whole post, join patreon today. when you become a member, you get instant access to exclusive posts and benefits. get more from comptia sos! ( save our servers ) on patreon. 🔐 security lab 7.2.7 — scan for ftp vulnerabilities this lab demonstrates how to identify vulnerabilities related to ftp (file transfer protocol), understand why ftp is. Is your file transfer protocol leaving you exposed? today we walk through lab 7.2.7, focusing on scanning for ftp vulnerabilities. we explore how hackers identify weak points in file. A server is used to transfer company financial data to remote branches using the ftp protocol. since the data is sensitive to the company, you have been asked to scan the host for.
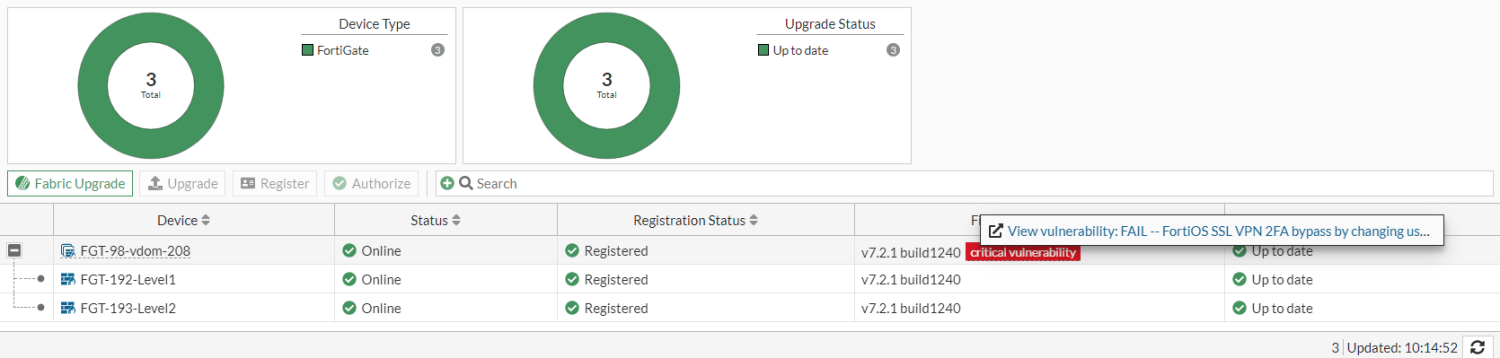
Vulnerabilities Fortigate Fortios 7 6 3 Fortinet Document Library Is your file transfer protocol leaving you exposed? today we walk through lab 7.2.7, focusing on scanning for ftp vulnerabilities. we explore how hackers identify weak points in file. A server is used to transfer company financial data to remote branches using the ftp protocol. since the data is sensitive to the company, you have been asked to scan the host for. In this article, i’m exploring a new vulnerability on the metasploitable 2 virtual machine by exploiting an ftp (file transfer protocol) service running on the target. In this lab, we will be establishing a shell on our metasploitable vm by exploiting a vulnerable ftp service. the objective of this lab is to highlight the importance of enumeration and to show you how a vulnerable service can be exploited using metasploit. Ftp (file transfer protocol) pentesting techniques for identifying, exploiting, enumeration, attack vectors and post exploitation insights. This article will guide you through the process of using nessus to scan ftp servers for security vulnerabilities, including how to configure nessus for ftp scanning, common vulnerabilities to look out for, and best practices for securing ftp servers.
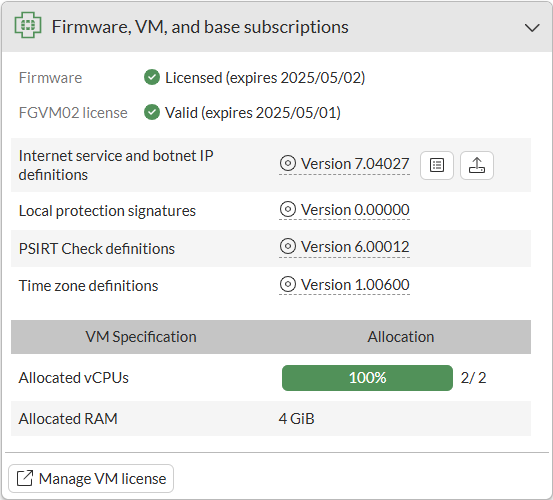
Vulnerabilities Fortigate Fortios 7 6 3 Fortinet Document Library In this article, i’m exploring a new vulnerability on the metasploitable 2 virtual machine by exploiting an ftp (file transfer protocol) service running on the target. In this lab, we will be establishing a shell on our metasploitable vm by exploiting a vulnerable ftp service. the objective of this lab is to highlight the importance of enumeration and to show you how a vulnerable service can be exploited using metasploit. Ftp (file transfer protocol) pentesting techniques for identifying, exploiting, enumeration, attack vectors and post exploitation insights. This article will guide you through the process of using nessus to scan ftp servers for security vulnerabilities, including how to configure nessus for ftp scanning, common vulnerabilities to look out for, and best practices for securing ftp servers.
Comments are closed.