649e58edb7c618952545823dcaef24c38374426e Gifv

94cc228e6b54004da8cb75ed4f6efd51 Youtube It's common knowledge that the decryption of a "hash" is impossible. this service uses "reverse lookup" via the database to match a hash to its value. our database is around ~3000m records in size and keeps growing. calculate hash! with no changes in a codebase! decode!. Identify and detect unknown hashes using this tool. this page will tell you what type of hash a given string is. if you want to attempt to decrypt them, click this link instead. decrypt hashes.

2d6e48bfb9a6f6ea2633a08c9ad3be26 Youtube Join our upcoming webinar on november 6th at 17:00 pm cest and 11:00 am edt where we'll show you how to transform raw intelligence into a dynamic, actionable defense strategy. we’ll start with a real world scenario from google threat intelligence. Uncover it is a malware configuration extractor that can analyze files statically. Meet base64 decode and encode, a simple online tool that does exactly what it says: decodes from base64 encoding as well as encodes into it quickly and easily. base64 encode your data without hassles or decode it into a human readable format. Instructions to insert two key files into the yuzu keys folder 1: open yuzu exe 2: look in the top left corner, and click file. 3: click the "open yuzu folder" option 4: locate the keys folder 5: paste the who key files "prod.keys" and "title.keys" into the empty keys folder enojy.
B5ea649db2312071e5c4e8236a158f0c Youtube Meet base64 decode and encode, a simple online tool that does exactly what it says: decodes from base64 encoding as well as encodes into it quickly and easily. base64 encode your data without hassles or decode it into a human readable format. Instructions to insert two key files into the yuzu keys folder 1: open yuzu exe 2: look in the top left corner, and click file. 3: click the "open yuzu folder" option 4: locate the keys folder 5: paste the who key files "prod.keys" and "title.keys" into the empty keys folder enojy. Quickly search and locate dll files by cryptographic hash (md5, sha1, or sha256) to verify integrity and compatibility. Learn what a hash is, how it works, and how hashes are used for verification, cybersecurity, file integrity, and blockchain metadata. Ransomware.live tracks ransomware groups and their activity. it was created by julien mousqueton, a security researcher. the website provides information on the groups' infrastructure, victims, and payment demands. it also includes a live map that shows the latest ransomware attacks. When you go to a download website to download a large file, you might see a series of numbers displayed alongside the download link. these are commonly referred to as checksums or hashes and allow you to confirm that the download completed successfully.
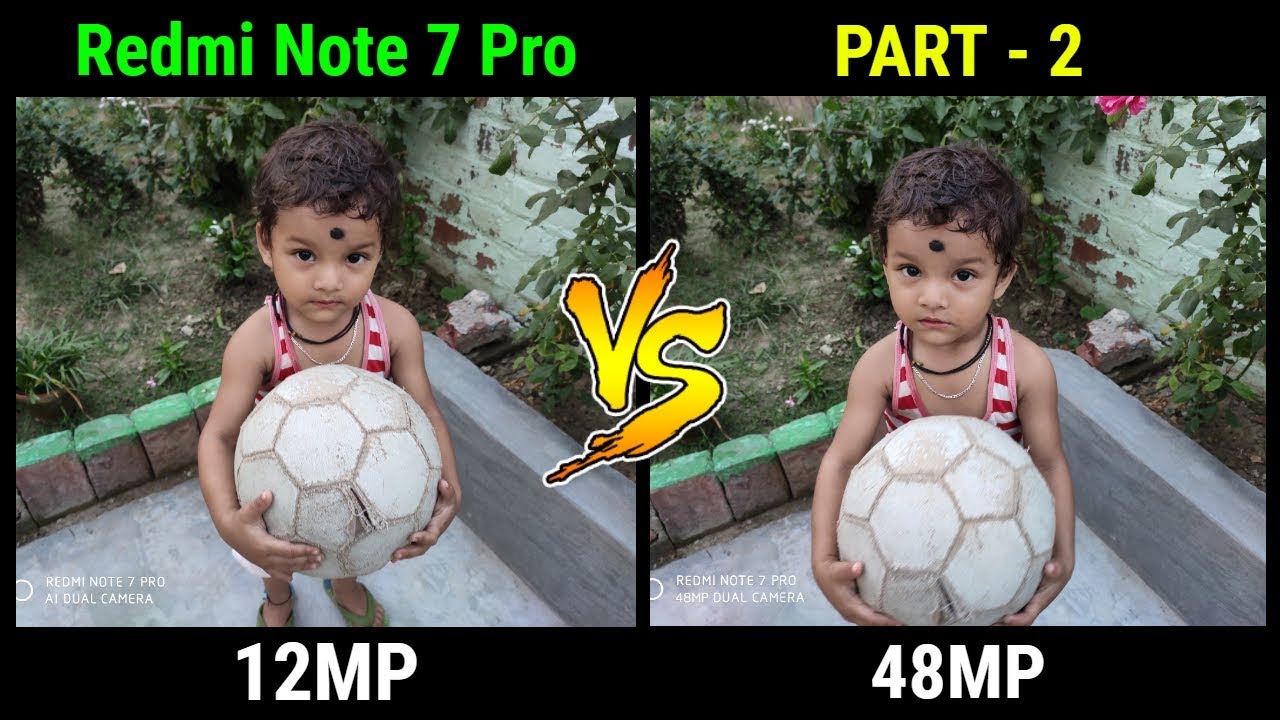
Redmi Note 7 Pro 12mp Camera Vs 48mp Camera Part 2 Data Dock Youtube Quickly search and locate dll files by cryptographic hash (md5, sha1, or sha256) to verify integrity and compatibility. Learn what a hash is, how it works, and how hashes are used for verification, cybersecurity, file integrity, and blockchain metadata. Ransomware.live tracks ransomware groups and their activity. it was created by julien mousqueton, a security researcher. the website provides information on the groups' infrastructure, victims, and payment demands. it also includes a live map that shows the latest ransomware attacks. When you go to a download website to download a large file, you might see a series of numbers displayed alongside the download link. these are commonly referred to as checksums or hashes and allow you to confirm that the download completed successfully.
Comments are closed.