6 Phishing2 Export Php
Php Excel Export Code Data To File Phppot Enjoy the videos and music you love, upload original content, and share it all with friends, family, and the world on . Simple php phishing page. github gist: instantly share code, notes, and snippets.

10 Best Php Projects To Add To Your Resume Updated In this section, we'll teach you how to exploit some common scenarios using examples from php, ruby, and java deserialization. we hope to demonstrate how. A collection of php exploit scripts, found when investigating hacked servers. these are stored for educational purposes and to test fuzzers and vulnerability scanners. 6 phishing 2 export php cehv7 by engineer momen hany arabic moamen hany مؤمن هاني 11.3k subscribers subscribe. Php script intdended to be used during phishing campaigns as a credentials collector linked to backdoored html
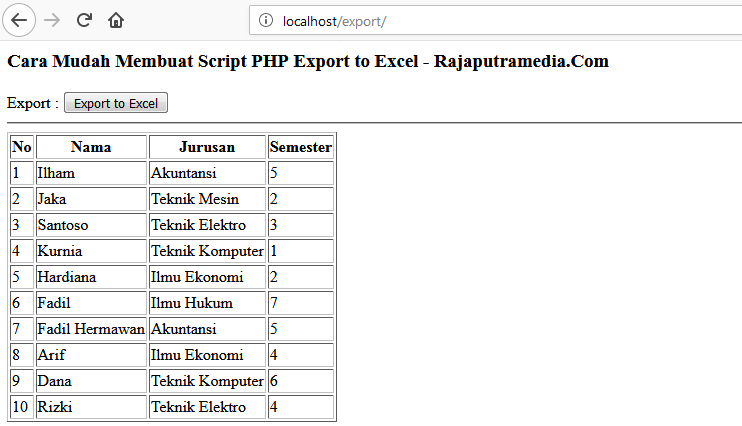
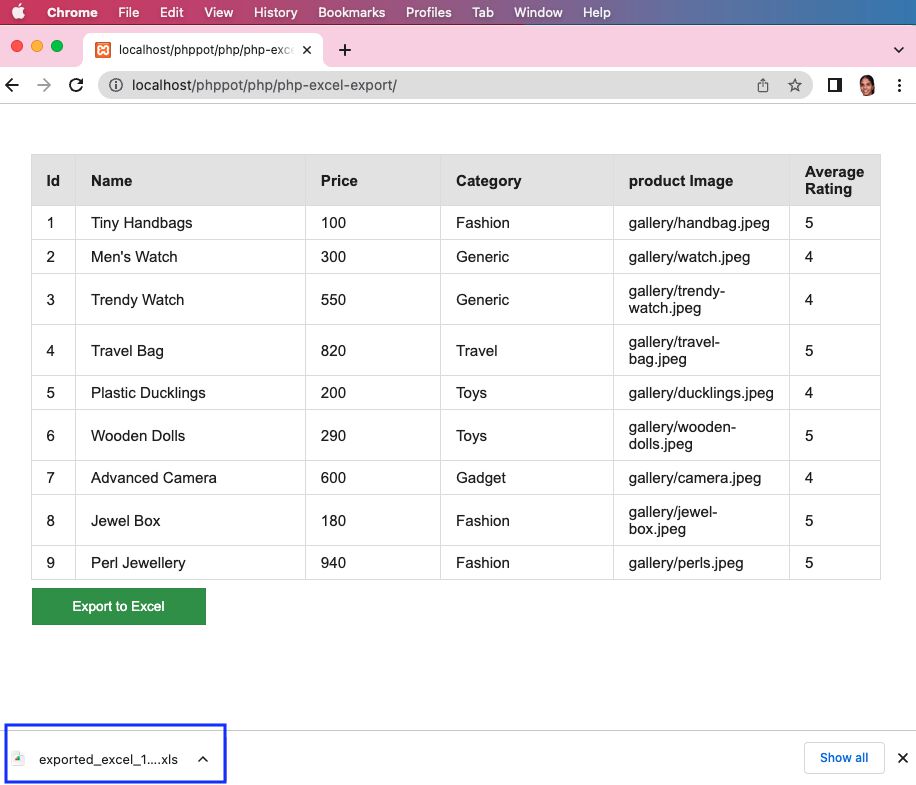
Script Php Export To Excel Tutorial 6 phishing 2 export php cehv7 by engineer momen hany arabic moamen hany مؤمن هاني 11.3k subscribers subscribe. Php script intdended to be used during phishing campaigns as a credentials collector linked to backdoored html
Comments are closed.