6 Essential Stages Of The Vulnerability Management Lifecycle Wiz
Vulnerability Management Lifecycle 5 Step Process Explained Learn the key stages of a modern vulnerability management lifecycle and find out how a unified approach to visibility can improve multi cloud security. The vulnerability management lifecycle is a structured approach to managing potential security weaknesses in information systems. it consists of several key stages, focusing on identifying, assessing, and mitigating vulnerabilities to protect organizational assets.
6 Essential Stages Of The Vulnerability Management Lifecycle Wiz What are the stages of the vulnerability management lifecycle? the vulnerability management lifecycle consists of six essential stages, each designed to ensure vulnerabilities are systematically identified, assessed, and mitigated before they can be exploited. The lifecycle typically consists of several key stages, including planning, asset discovery, vulnerability assessment, prioritization, remediation, and monitoring. Discover 6 key steps of the vm lifecycle, from asset discovery to remediation and continuous monitoring, for effective risk reduction. Each stage in the cycle secures software environments by reducing attack surfaces and maintaining security. this article breaks down each lifecycle stage, explores common security challenges, and highlights the importance of the vulnerability management lifecycle.
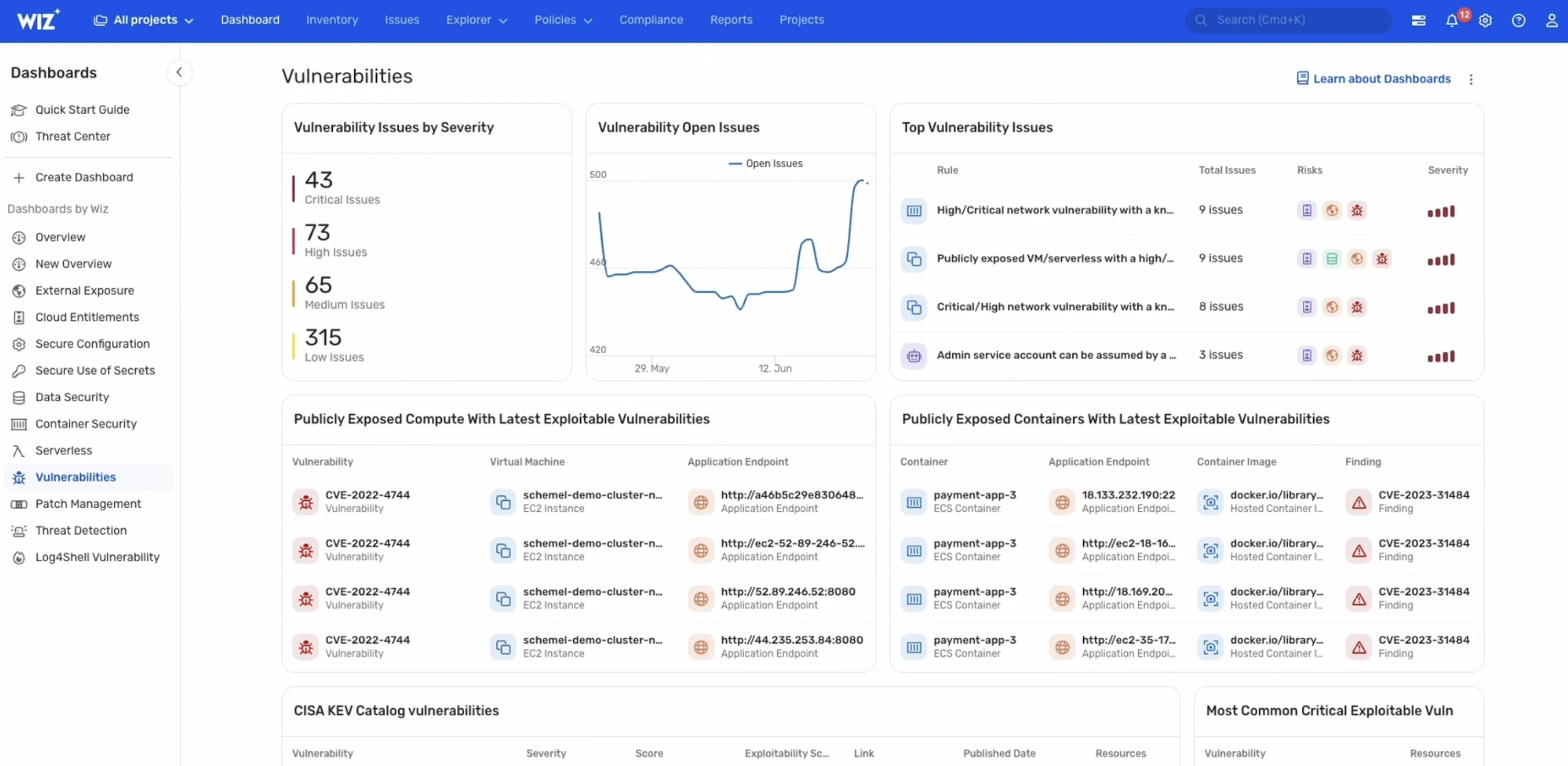
6 Essential Stages Of The Vulnerability Management Lifecycle Wiz Discover 6 key steps of the vm lifecycle, from asset discovery to remediation and continuous monitoring, for effective risk reduction. Each stage in the cycle secures software environments by reducing attack surfaces and maintaining security. this article breaks down each lifecycle stage, explores common security challenges, and highlights the importance of the vulnerability management lifecycle. This guide breaks down each stage of the lifecycle, explains how modern teams apply risk based decision making, and outlines best practices for building a scalable program. Learn the vulnerability management lifecycle and its five core phases. discover best practices, challenges, and how continuous vulnerability management prevents breaches and ensures compliance. The vulnerability management lifecycle comprises six essential steps that organizations must follow to effectively manage vulnerabilities and protect their systems. The guide provides in depth coverage of the full vulnerability management lifecycle including the preparation phase, the vulnerability identification scanning phase, the reporting phase, and remediation phase.
6 Essential Stages Of The Vulnerability Management Lifecycle Wiz This guide breaks down each stage of the lifecycle, explains how modern teams apply risk based decision making, and outlines best practices for building a scalable program. Learn the vulnerability management lifecycle and its five core phases. discover best practices, challenges, and how continuous vulnerability management prevents breaches and ensures compliance. The vulnerability management lifecycle comprises six essential steps that organizations must follow to effectively manage vulnerabilities and protect their systems. The guide provides in depth coverage of the full vulnerability management lifecycle including the preparation phase, the vulnerability identification scanning phase, the reporting phase, and remediation phase.
Comments are closed.