6 Cryptographic Primitives Encryption Ciphers

Cryptographic Primitives Pdf Cryptography Time Complexity When creating cryptographic systems, designers use cryptographic primitives as their most basic building blocks. because of this, cryptographic primitives are designed to do one very specific task in a precisely defined and highly reliable fashion. Learn about the fundamental components that make up cryptographic systems and how they are used to secure data and communications.
Cryptographic Primitives In Blockchain Pdf Cryptography Key The first step is the cryptographic algorithms—ciphers and cryptographic hashes—that are introduced in this chapter. such algorithms are not a solution in themselves, but provide building blocks from which a solution can be built. Where each arrow means that we can construct one primitive from the other one. the other direction is also true (and is much easier to show), so each of these primitives is in fact sufficient and necessary for symmetric key cryptography. Cryptographic primitives are fundamental building blocks of cryptographic systems that provide security, privacy, and reliability for transactions. they include public key cryptography, hash functions, and merkle trees. Cipher suites define the cryptographic algorithms used for key exchange, bulk encryption, and message authentication, while the primitives provide the actual implementations of symmetric ciphers, hash functions, and authenticated encryption modes.

Cryptographic Primitives In Blockchain Technology Cryptographic primitives are fundamental building blocks of cryptographic systems that provide security, privacy, and reliability for transactions. they include public key cryptography, hash functions, and merkle trees. Cipher suites define the cryptographic algorithms used for key exchange, bulk encryption, and message authentication, while the primitives provide the actual implementations of symmetric ciphers, hash functions, and authenticated encryption modes. Asymmetric ciphers encrypt and decrypt with two different keys. one key generally is designated as the private key and the other is designated as the public key. Cryptography is based on the use of the mathematical principles in storing and transmitting data in a particular form so that only those whom it is intended can read and process it. Examples of primitives include encryption schemes, hash functions, and digital signature schemes. the figure in below provides a schematic listing of the primitives considered and how they relate. A cryptographic framework defines: engine classes (and possibly algorithm classes) transparent key and parameter classes interfaces for opaque keys and parameters.
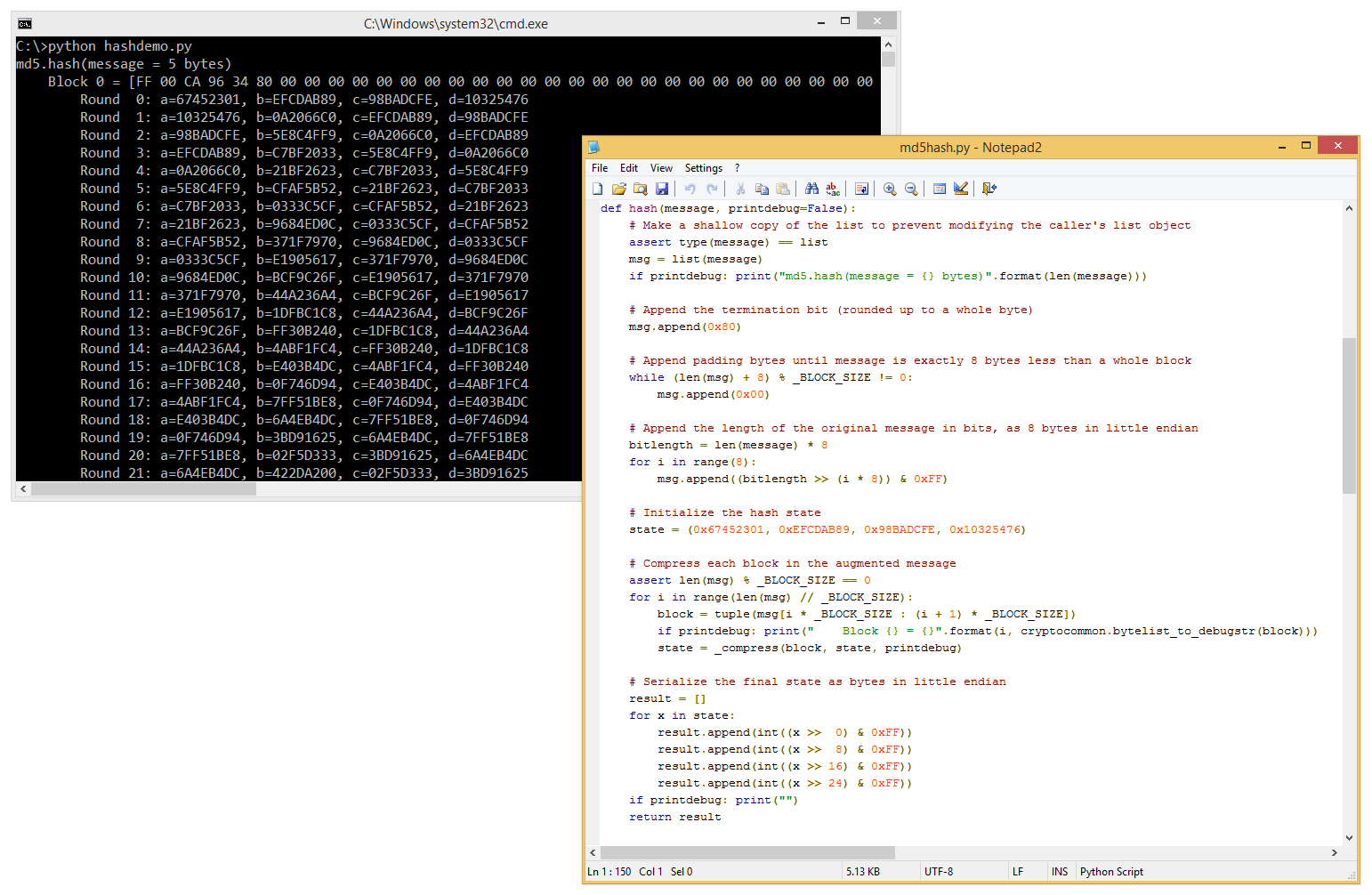
Cryptographic Primitives In Plain Python Asymmetric ciphers encrypt and decrypt with two different keys. one key generally is designated as the private key and the other is designated as the public key. Cryptography is based on the use of the mathematical principles in storing and transmitting data in a particular form so that only those whom it is intended can read and process it. Examples of primitives include encryption schemes, hash functions, and digital signature schemes. the figure in below provides a schematic listing of the primitives considered and how they relate. A cryptographic framework defines: engine classes (and possibly algorithm classes) transparent key and parameter classes interfaces for opaque keys and parameters.

Cryptographic Primitives In Blockchain Pdf Cryptography Ellipse Examples of primitives include encryption schemes, hash functions, and digital signature schemes. the figure in below provides a schematic listing of the primitives considered and how they relate. A cryptographic framework defines: engine classes (and possibly algorithm classes) transparent key and parameter classes interfaces for opaque keys and parameters.
Comments are closed.