6 Access Via Api 2

Api 2 Pdf Configure access to apis in your azure api center inventory using api keys, oauth 2.0 authorization, or other http security schemes. authorized users can test apis in the api center portal. An api is a set of rules and protocols that allow one software application to interact with another. it defines the methods and data formats that applications can use to communicate.
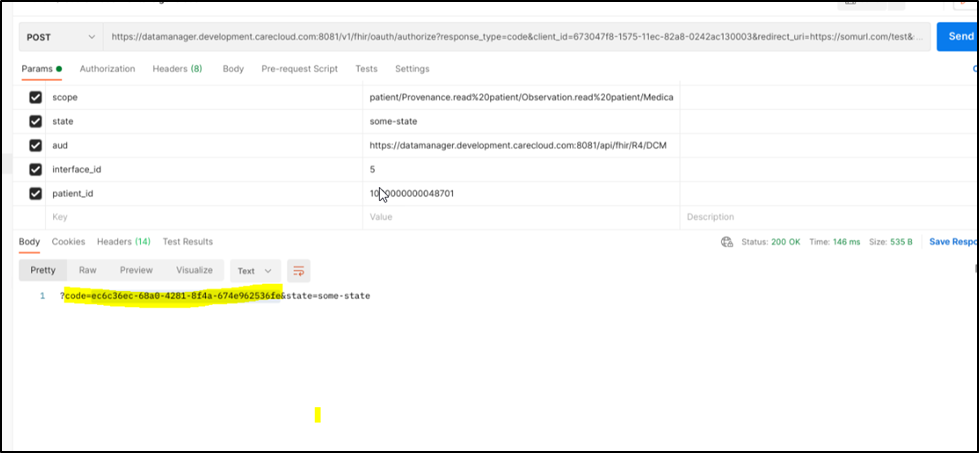
Connector Api Access Administrators can use api calls to a fortigate to: perform basic administrative actions, such as a reboot or shut down through programming scripts. fortigate supports only token based authentication for api calls. Learn oauth 2 fundamentals, how authorization works, and how to securely grant api access. covers roles, grant types, and when to use each flow. In this codelab you’ll learn how configure and validate ipv6 access to google apis from on premises hosts. This page shows you how rest clients can authenticate themselves using basic authentication with an atlassian account email address and api token. authentication using passwords has been deprecated.
What Is Api Access On The Example Of Ecommerce Platforms Api2cart In this codelab you’ll learn how configure and validate ipv6 access to google apis from on premises hosts. This page shows you how rest clients can authenticate themselves using basic authentication with an atlassian account email address and api token. authentication using passwords has been deprecated. In our api management instance, we need to create an oauth 2.0 service, which will interact with our app registrations to retrieve an access token. this service acts as the bridge between api management and azure active directory, enabling secure authentication and authorization for api requests. Oauth 2.0 offers a secure and flexible framework for accessing apis on behalf of users. by implementing best practices and leveraging available tools, developers can effectively utilize oauth 2.0 to ensure user security and a smooth experience when accessing resources. We’ve covered the basics of rest apis, creating api requests, understanding api endpoints, working with api responses, handling api errors, and using api authentication. Learn about authentication and authorization features in azure api management to secure access to apis, including options for oauth 2.0 authorization.
Api Access Setup In our api management instance, we need to create an oauth 2.0 service, which will interact with our app registrations to retrieve an access token. this service acts as the bridge between api management and azure active directory, enabling secure authentication and authorization for api requests. Oauth 2.0 offers a secure and flexible framework for accessing apis on behalf of users. by implementing best practices and leveraging available tools, developers can effectively utilize oauth 2.0 to ensure user security and a smooth experience when accessing resources. We’ve covered the basics of rest apis, creating api requests, understanding api endpoints, working with api responses, handling api errors, and using api authentication. Learn about authentication and authorization features in azure api management to secure access to apis, including options for oauth 2.0 authorization.

Api Access Management Making Api Access Easy And Secure We’ve covered the basics of rest apis, creating api requests, understanding api endpoints, working with api responses, handling api errors, and using api authentication. Learn about authentication and authorization features in azure api management to secure access to apis, including options for oauth 2.0 authorization.
Comments are closed.