5g Security Pdf Electronics Computer Science

5g Security Pdf Cyberspace Computing Due to their complexity and large attack surface, 5g networks pose threats and potential for cybersecurity. this paper examines these issues. the study seeks to uncover 5g network design. 5g networks introduce significant security challenges that threaten data integrity and confidentiality. the paper analyzes various security threats, including man in the middle attacks and dos attacks, and proposes mitigation strategies.
4g And 5g Network Security Techniques And Algorithms 4g And 5g With its advanced software, cloud based architecture, and extensive connectivity, 5g technology introduces new security paradigms. it offers significant benefits but also brings new risks, necessitating robust cybersecurity measures to protect against threats. These recommendations inform a security architecture strategy that builds on inherent security services defined in the 5g standard. This nist cybersecurity practice guide explains how a combination of 5g security features and third party security controls can be used to implement the security capabilities organizations need to safeguard their 5g network usage. M. gilje jaatun, “improving smart grid security through 5g en abled iot and edge computing,” concurrency and computation: practice and experience, vol. 33, no. 18, p. e6466, 2021.
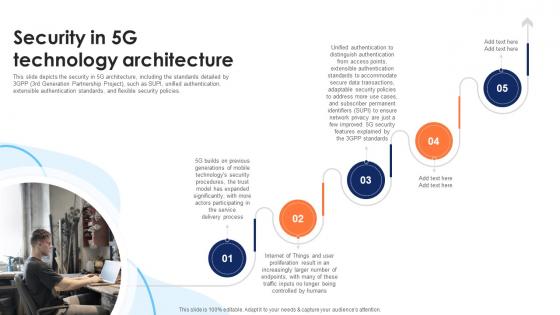
5g Security Slide Team This nist cybersecurity practice guide explains how a combination of 5g security features and third party security controls can be used to implement the security capabilities organizations need to safeguard their 5g network usage. M. gilje jaatun, “improving smart grid security through 5g en abled iot and edge computing,” concurrency and computation: practice and experience, vol. 33, no. 18, p. e6466, 2021. In the preparation of the material for the report we have conducted an analysis of publically available information on security in 5g specifications in collaboration with plum consulting, under the tender enisa s cod 20 t14. This paper focuses on the security aspects of 5g technology in the network and discusses the pros and cons of security in this area. through the research in this paper, people will be able to understand more about the security of 5g living and be more confident and reassured about it. This paper will summarize the research done in the 5g security space and will provide an overview of the technologies used in 5g, the security built into 5g, and the vulnerabilities of. We explore the architecture of the 5g architecture and give an overview of the types of attack vectors and how to possibly mitigate the attacks. through our research, we found that vulnerabilities must be addressed at every level within the infrastructure of 5g network.

5g Security Pdf Mobile Technology Service Industries In the preparation of the material for the report we have conducted an analysis of publically available information on security in 5g specifications in collaboration with plum consulting, under the tender enisa s cod 20 t14. This paper focuses on the security aspects of 5g technology in the network and discusses the pros and cons of security in this area. through the research in this paper, people will be able to understand more about the security of 5g living and be more confident and reassured about it. This paper will summarize the research done in the 5g security space and will provide an overview of the technologies used in 5g, the security built into 5g, and the vulnerabilities of. We explore the architecture of the 5g architecture and give an overview of the types of attack vectors and how to possibly mitigate the attacks. through our research, we found that vulnerabilities must be addressed at every level within the infrastructure of 5g network.

5g Scenarios And Security Design Pdf Computer Network Security This paper will summarize the research done in the 5g security space and will provide an overview of the technologies used in 5g, the security built into 5g, and the vulnerabilities of. We explore the architecture of the 5g architecture and give an overview of the types of attack vectors and how to possibly mitigate the attacks. through our research, we found that vulnerabilities must be addressed at every level within the infrastructure of 5g network.
Comments are closed.