5g Security Overview Mpirical

5g Security Overview By Mpirical Take a look with mpirical. in this video we consider 5g security on an end to end basis. starting with a high level overview followed by an exploration of mutual authentication, encryption. This course takes an end to end view of 5g security, first of all determining what assets are applicable to the 5g architecture and which threats are relevant.

5g Security Overview Mpirical Graeme Green This video looks at 5g security on an end to end basis. starting with a high level overview followed by an exploration of mutual authentication, encryption and integrity checking alongside the protection of service based interfaces, roaming and subscriber identity. This three day training session, ts 501, is designed to equip security and telecom professionals with a deep understanding of the key concepts of 5g, its security aspects, architecture implementation, and related risks. This mpirical course seeks to explore these areas by initially evaluating the end to end 5g system, in terms of architecture and overall operation, with emphasis on security roles. 5g aka. Designed for on the go learning or to supplement your regular training, these short, 'byte' sized videos cover a wide range of topics and are suited for telecoms professionals of all skill levels .

Mpirical On Linkedin 5g Security Course Mpirical This mpirical course seeks to explore these areas by initially evaluating the end to end 5g system, in terms of architecture and overall operation, with emphasis on security roles. 5g aka. Designed for on the go learning or to supplement your regular training, these short, 'byte' sized videos cover a wide range of topics and are suited for telecoms professionals of all skill levels . Description if you are involved in the troubleshooting of 5g networks, you will appreciate that having a good understanding of the protocols. is critical. this course, therefore, sets out to provide a detailed explanation of the key 5g protocols found in the ng ran. and 5g core. specifically focusing on 5g nas, rrc, ngap, service based interfac. This three day training session, ts 501, is designed to equip security and telecom professionals with a deep understanding of the key concepts of 5g, its security aspects, architecture implementation, and related risks. 3. 5g security analysis topic areas covered include: supporting security in 5g: 5g security overview. standards bodies. 5g cryptographic processes: 5g security algorithms. authentication and key agreement. In this blog post, we’ll take a closer look at the enhanced features and robust security measures that make 5g networks more resilient and secure.
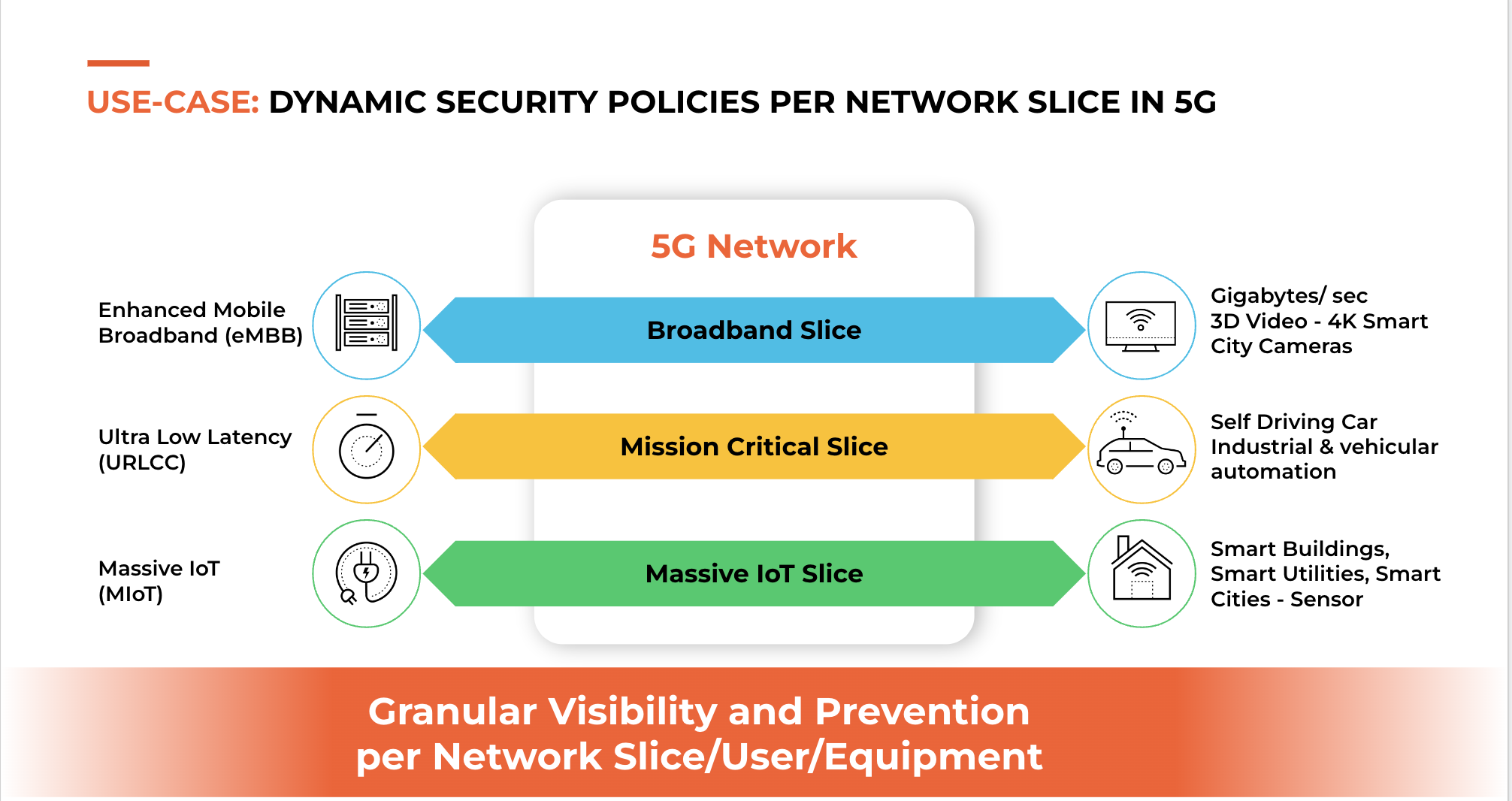
Enforce Zero Trust For 5g Security To Work Description if you are involved in the troubleshooting of 5g networks, you will appreciate that having a good understanding of the protocols. is critical. this course, therefore, sets out to provide a detailed explanation of the key 5g protocols found in the ng ran. and 5g core. specifically focusing on 5g nas, rrc, ngap, service based interfac. This three day training session, ts 501, is designed to equip security and telecom professionals with a deep understanding of the key concepts of 5g, its security aspects, architecture implementation, and related risks. 3. 5g security analysis topic areas covered include: supporting security in 5g: 5g security overview. standards bodies. 5g cryptographic processes: 5g security algorithms. authentication and key agreement. In this blog post, we’ll take a closer look at the enhanced features and robust security measures that make 5g networks more resilient and secure.
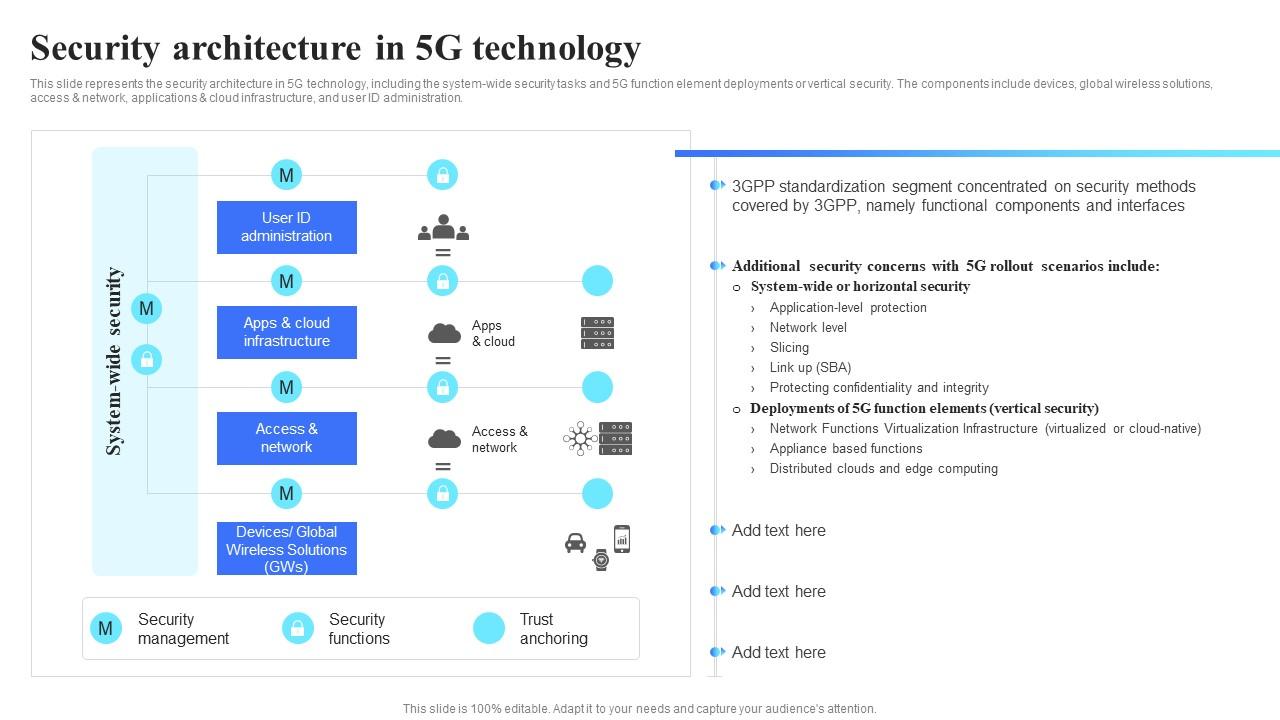
Security Architecture In 5g Technology Ppt Powerpoint Presentation 3. 5g security analysis topic areas covered include: supporting security in 5g: 5g security overview. standards bodies. 5g cryptographic processes: 5g security algorithms. authentication and key agreement. In this blog post, we’ll take a closer look at the enhanced features and robust security measures that make 5g networks more resilient and secure.

How 5g Is Enabling Resilient Communication For The Connected
Comments are closed.