5g Security Architecture With Mitigation Strategy Part 2
It Security Threat Mitigation Strategies Ppt Example Part 2 of ‘5g security architecture with mitigation strategies’ by taha sajid explores 5g network security and explains threats and challenges to network security. The design of 5g network technology shall be used in our research paper to fully indicate the vulnerabilities that arise in the network due to the reliance of the network on software defined networks, network function virtualisation, and network slicing technology.
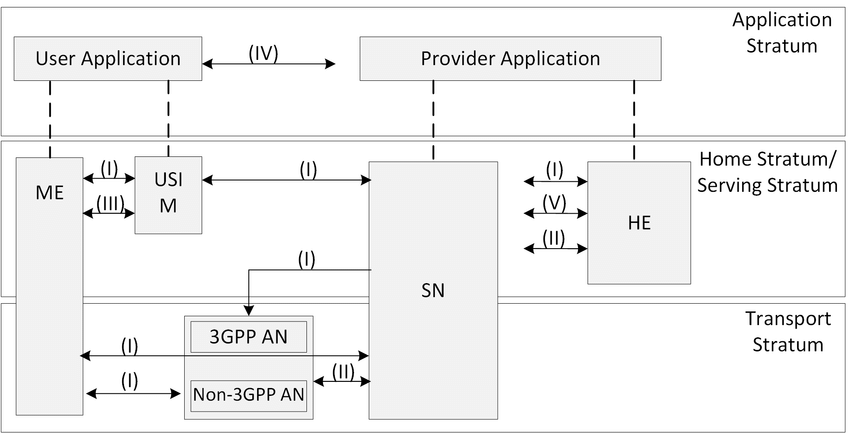
3gpp 5g Security Architecture Dr Moazzam Tiwana This paper critically evaluates network security concerning the features and architecture of 5g, identifying essential threats and vulnerabilities that are inherent in a software defined,. The present document specifies the security architecture, i.e., the security features and the security mechanisms for the 5g system and the 5g core, and the security procedures performed within the 5g system including the 5g core and the 5g new radio. In alignment with line of effort 2 in the national strategy to secure 5g, the enduring security framework (esf) was identified to assist with assessing risks and vulnerabilities to 5g infrastructure. this included building on existing capabilities in assessing and managing supply chain risk. Drawing inspiration from such approaches, this study applies a layered perspective to analyze threats in 5g slicing, with a focus on architectural alignment and practical mitigation strategies.

5g Security Architecture In alignment with line of effort 2 in the national strategy to secure 5g, the enduring security framework (esf) was identified to assist with assessing risks and vulnerabilities to 5g infrastructure. this included building on existing capabilities in assessing and managing supply chain risk. Drawing inspiration from such approaches, this study applies a layered perspective to analyze threats in 5g slicing, with a focus on architectural alignment and practical mitigation strategies. Because physical separation is not feasible, methods for logically separating 5g trafic from other trafic and further separating types of 5g trafic from each other are needed to improve 5g cybersecurity and privacy. This study proposes a comprehensive multi layered cybersecurity framework tailored for 5g infrastructures. Technical specification 5g; security architecture and procedures for 5g system (3gpp ts (standa 33.501 version ds.iteh.ai) 17.5.0 release 17). With this expansion comes an exponentially larger attack surface, necessitating a fundamentally reimagined security architecture to defend against new and evolving threats.

Ai Ml Security Attacks And Mitigation Strategies On 5g Network Because physical separation is not feasible, methods for logically separating 5g trafic from other trafic and further separating types of 5g trafic from each other are needed to improve 5g cybersecurity and privacy. This study proposes a comprehensive multi layered cybersecurity framework tailored for 5g infrastructures. Technical specification 5g; security architecture and procedures for 5g system (3gpp ts (standa 33.501 version ds.iteh.ai) 17.5.0 release 17). With this expansion comes an exponentially larger attack surface, necessitating a fundamentally reimagined security architecture to defend against new and evolving threats.

Mitigation Plan To Manage 5g Security Risks Ppt Example Technical specification 5g; security architecture and procedures for 5g system (3gpp ts (standa 33.501 version ds.iteh.ai) 17.5.0 release 17). With this expansion comes an exponentially larger attack surface, necessitating a fundamentally reimagined security architecture to defend against new and evolving threats.

5g Security Architecture Download Scientific Diagram
Comments are closed.