5g Security Architecture Download Scientific Diagram
Security Architecture Diagram This paper introduces a novel security framework for 5g networks, addressing these challenges with innovative cryptographic and authentication solutions. The present document specifies the security architecture, i.e., the security features and the security mechanisms for the 5g system and the 5g core, and the security procedures performed within the 5g system including the 5g core and the 5g new radio.

Security Architecture Diagram This work focuses on a multi layered 5g security architecture integrating device attestation, trust scoring, slice aware isolation, zero trust orchestration, and ai driven threat detection. This white paper describes the network infrastructure design principles that commercial and private 5g network operators are encouraged to use to improve cybersecurity and privacy. such a network infrastructure isolates types of 5g network trafic from each other: data plane, signaling, and operation and maintenance (o&m) trafic. 3gpp.org. With useful diagrams and clear explanations, it explains the fundamentals of modern 5g networks and then goes deeper into the security architecture of these networks.
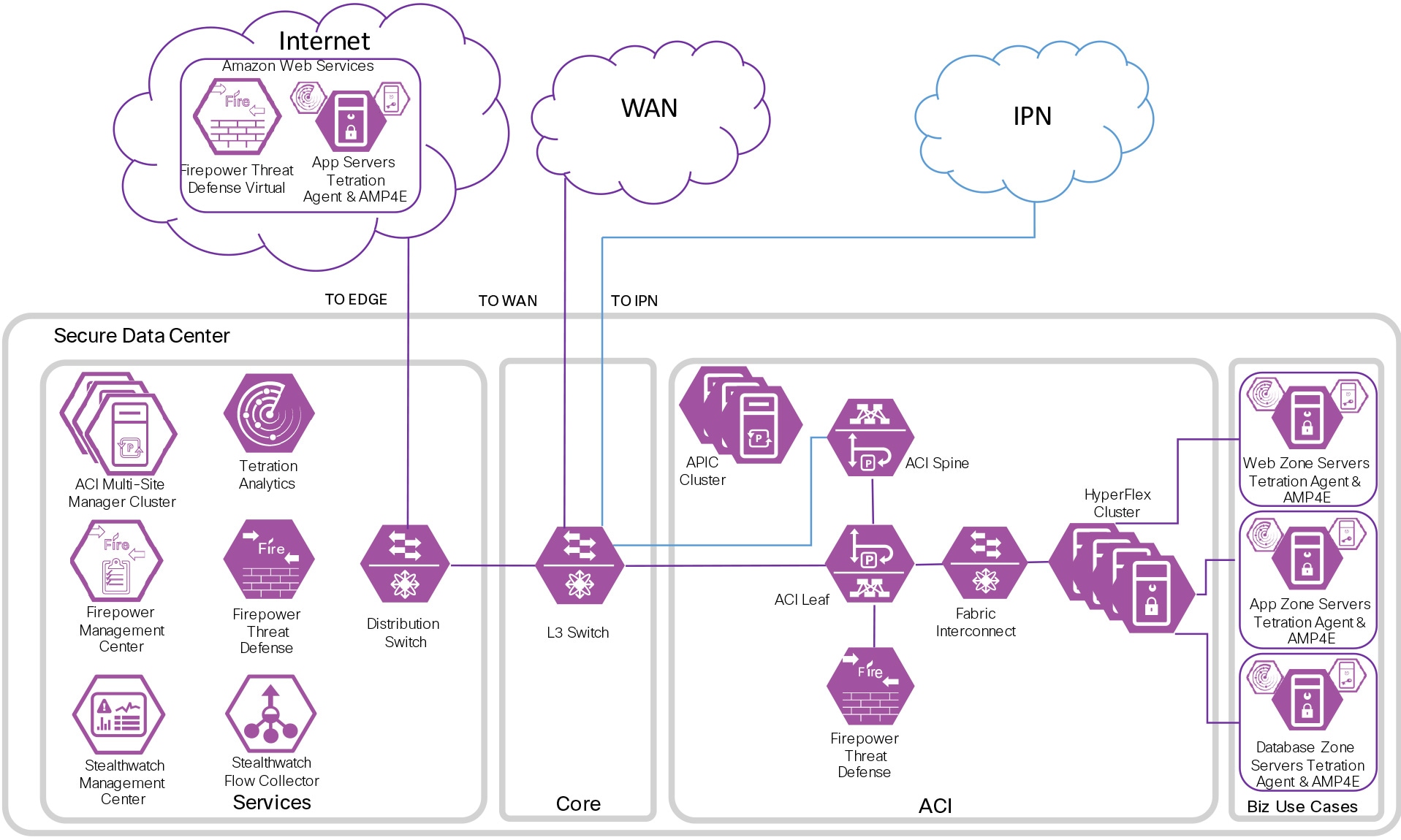
Network Security Architecture Diagram Sase Network Security That 3gpp.org. With useful diagrams and clear explanations, it explains the fundamentals of modern 5g networks and then goes deeper into the security architecture of these networks. The presented security architecture builds upon concepts from the 3g and 4g security architectures but extends and enhances them to cover the new 5g environment. The 5g network architecture accommodates the technical enablers and communication paradigms while considering existing and emerging network architectural trends. In this paper, we present a new access control architecture for the 5g mec network, which meets both security requirements in a flexible and lightweight way. first, we specify the architecture scheme and its central element, mec enabler, which manages access control security policies and generates access credentials (tokens). The following is a high level description of the process to secure a 5g network by applying our security architecture with its security realms and security control classes.

5g Network Architecture Diagram Download Scientific Diagram The presented security architecture builds upon concepts from the 3g and 4g security architectures but extends and enhances them to cover the new 5g environment. The 5g network architecture accommodates the technical enablers and communication paradigms while considering existing and emerging network architectural trends. In this paper, we present a new access control architecture for the 5g mec network, which meets both security requirements in a flexible and lightweight way. first, we specify the architecture scheme and its central element, mec enabler, which manages access control security policies and generates access credentials (tokens). The following is a high level description of the process to secure a 5g network by applying our security architecture with its security realms and security control classes.
Comments are closed.