5 Ways Hackers Can Hack Cryptocurrency Wallets
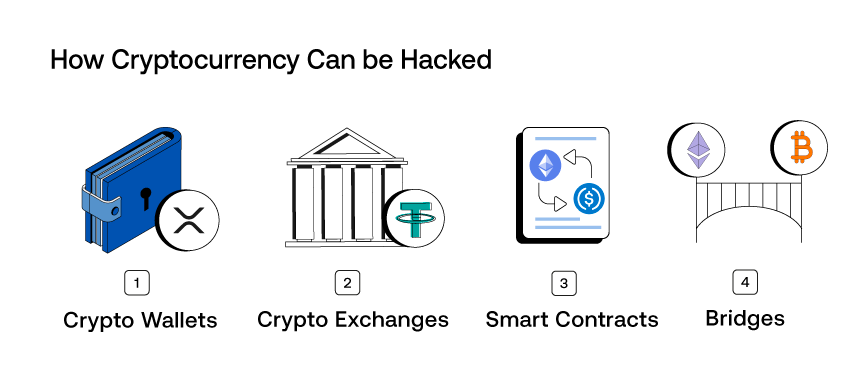
Can Crypto Wallets Be Hacked Secux Hardware Wallet This article provides a detailed analysis of common attack methods targeting cryptocurrency users, including phishing, malware, and social engineering attacks. it also reveals how these attacks operate and spread through real world case studies. A breakdown of how users get exploited in practice, and what to do about it. the report will focus on personal level exploits: phishing, wallet approvals, social engineering, malware. it will also briefly cover protocol level risks at the end to give a layout of the spectrum of exploits that happen in crypto. 2. the complete exploit playbook.
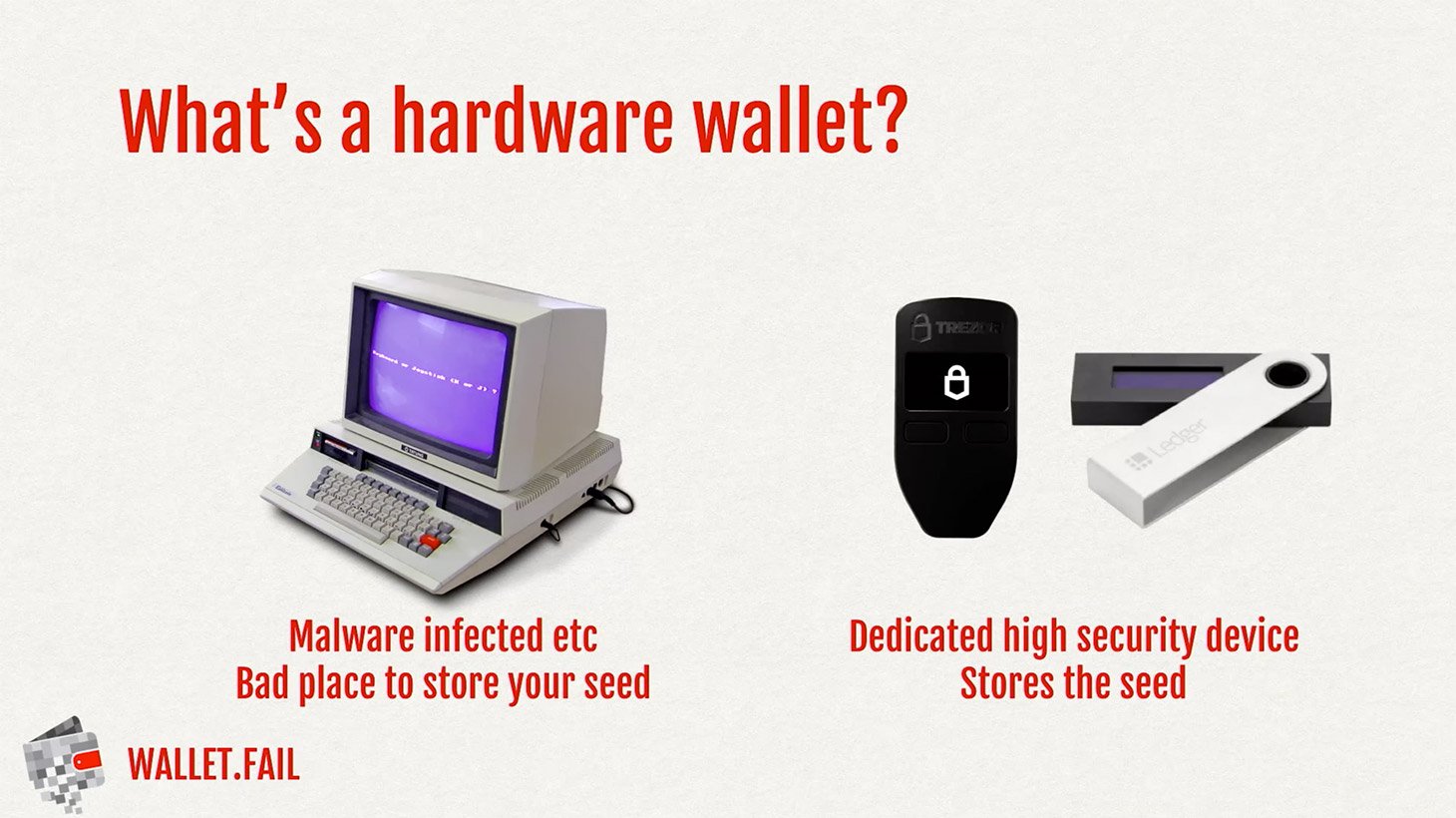
How To Hack A Hardware Cryptocurrency Wallet Kaspersky Official Blog The 5 largest crypto wallet hacks ever – how they happened and how to protect your assets from similar attacks. In this article, we’ll explore how crypto wallets can be hacked, the most common security risks to watch out for, and go over proper security measures to keep your crypto assets secure. Learn how hackers steal cryptocurrency wallets, the methods they use, and best practices to protect digital assets from theft and cyberattacks. In this article, we will explore the most common methods used by hackers to steal cryptocurrency and provide insights on how to protect your cryptocurrency from hackers.

How To Hack A Hardware Cryptocurrency Wallet Kaspersky Official Blog Learn how hackers steal cryptocurrency wallets, the methods they use, and best practices to protect digital assets from theft and cyberattacks. In this article, we will explore the most common methods used by hackers to steal cryptocurrency and provide insights on how to protect your cryptocurrency from hackers. How can someone hack your crypto wallet? 6 real attack vectors in 2026 greta Šimonėlytė communications manager 10 views · 3 min read. In this blog, we’ll discuss the top 5 attacks aimed at crypto wallet apps and how to solve them. the conventional wisdom is that crypto wallets come in two forms: hot wallets and cold wallets. hot wallets, we’re told, offer greater convenience and flexibility but come with greater security risks. Using all standard wallet safety methods while dealing with cryptocurrency is advisable since hacker techniques have changed. after reading this post, you should now be more aware of what to watch out for and how to safeguard your money. Discover the full list of crypto hacks in 2025, from scams and exploits to vulnerabilities. learn about notable incidents, including cetus, and how to protect your digital assets.

Crypto Hack By North Korea Hackers Yields Massive Cash Haul How can someone hack your crypto wallet? 6 real attack vectors in 2026 greta Šimonėlytė communications manager 10 views · 3 min read. In this blog, we’ll discuss the top 5 attacks aimed at crypto wallet apps and how to solve them. the conventional wisdom is that crypto wallets come in two forms: hot wallets and cold wallets. hot wallets, we’re told, offer greater convenience and flexibility but come with greater security risks. Using all standard wallet safety methods while dealing with cryptocurrency is advisable since hacker techniques have changed. after reading this post, you should now be more aware of what to watch out for and how to safeguard your money. Discover the full list of crypto hacks in 2025, from scams and exploits to vulnerabilities. learn about notable incidents, including cetus, and how to protect your digital assets.

Kaspersky Uncovers New Malware Stealing Crypto Wallets Via Mobile Photos Using all standard wallet safety methods while dealing with cryptocurrency is advisable since hacker techniques have changed. after reading this post, you should now be more aware of what to watch out for and how to safeguard your money. Discover the full list of crypto hacks in 2025, from scams and exploits to vulnerabilities. learn about notable incidents, including cetus, and how to protect your digital assets.
How To Protect Crypto Wallet From Hackers
Comments are closed.