5 Reasons To Keep Your Ot Network Safe Projectbinder

5 Reasons To Keep Your Ot Network Safe Projectbinder 5 reasons to keep your ot network secure an ot network out of date puts you at risk. modern industry equipment is obsolete at all levels, from production line machinery to computers and operating systems used at the office. all those devices represent a potential cyber security risk. that is why it…. 5 reasons to keep your ot network secure an ot network out of date puts you at risk. modern industry equipment is obsolete at all levels, from production line machinery to computers and operating systems used at the office.
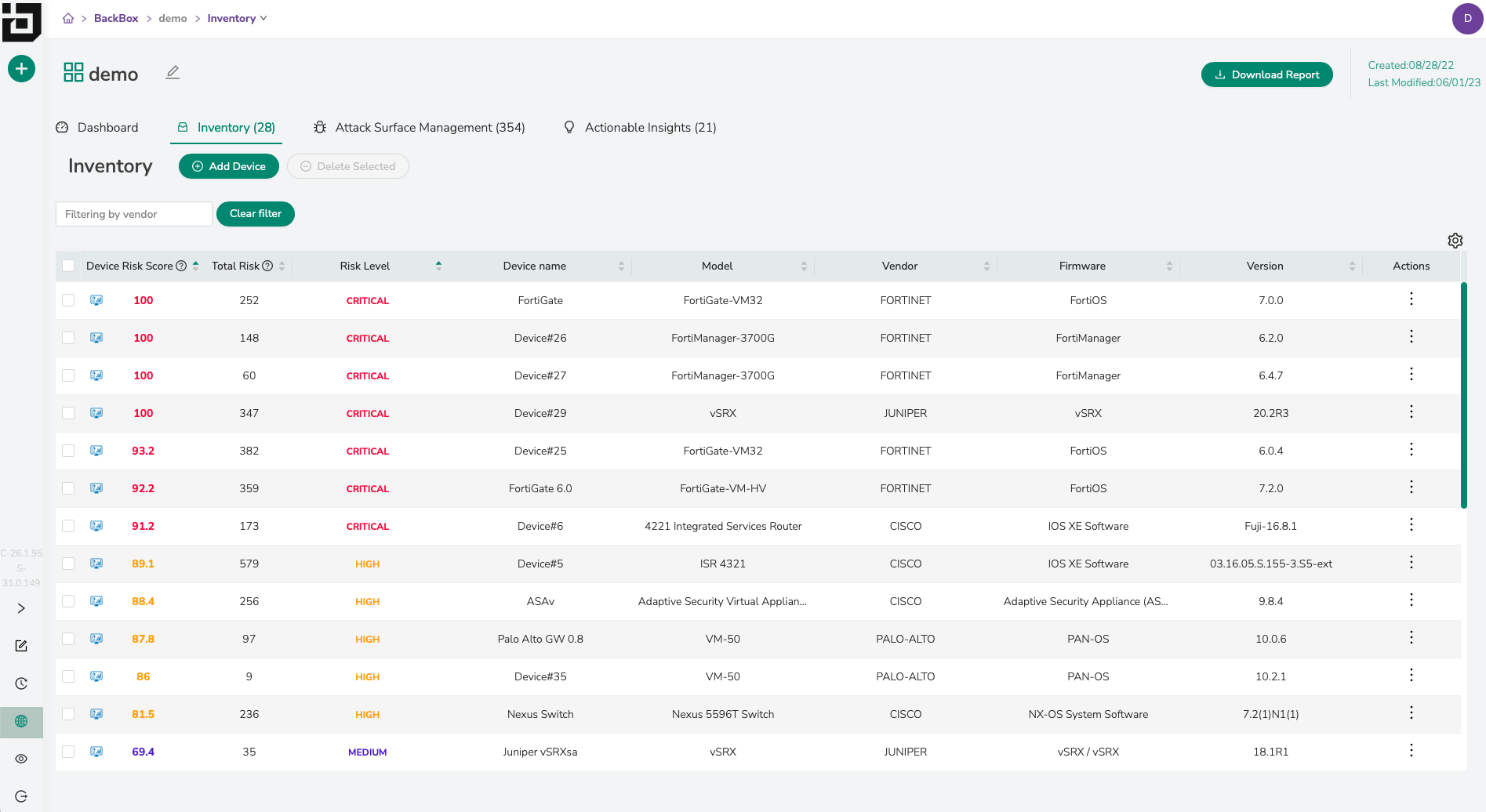
5 Questions To Help Keep Your Network Safe Backbox Software Cybercriminals are increasingly targeting ot networks. multiple recent attacks have shown that everyone is at risk and that the consequences for critical infrastructure are severe. at projectbinder, we aim to mitigate this risk by providing ot security services. An ot network contains many business critical components, such as plcs, hmis or dcs systems than can be exposed. now that we have an idea of how important it is to protect your ot network, here are all the benefits that monitoring can bring to your business. Without robust ot network security measures, several risks and consequences can unfold, posing substantial threats to industrial processes and critical infrastructure. Changing ot security in recent years, ot security has changed with the emergence of the connection between ot and it, also known as the ot it convergence. in this article, we briefly set out five tips to improve your ot security.

Five Ways To Keep Your Payment Network Safe In 2023 Without robust ot network security measures, several risks and consequences can unfold, posing substantial threats to industrial processes and critical infrastructure. Changing ot security in recent years, ot security has changed with the emergence of the connection between ot and it, also known as the ot it convergence. in this article, we briefly set out five tips to improve your ot security. By leveraging a cohesive, modular solution that integrates asset visibility, network protection, secure remote access, and safe data transfer, you gain the tools to secure ot and cps environments and confidently meet the evolving challenges of today’s threat landscape. Ot cyberattacks are no longer a distant threat—they're happening now. discover 5 urgent reasons why securing operational technology (ot) networks is critical to protect industries, communities, and lives. Get an in depth overview of ot network segmentation, learn how it works, and find out why it's key to securing industrial networks against ransomware as ot and it environments converge. Learn five best practices for operational technology (ot) security and which tools provide the most comprehensive protection. operational technology controls business devices, processes, and events.

5 Ways To Keep Your Network Safe Pcmag By leveraging a cohesive, modular solution that integrates asset visibility, network protection, secure remote access, and safe data transfer, you gain the tools to secure ot and cps environments and confidently meet the evolving challenges of today’s threat landscape. Ot cyberattacks are no longer a distant threat—they're happening now. discover 5 urgent reasons why securing operational technology (ot) networks is critical to protect industries, communities, and lives. Get an in depth overview of ot network segmentation, learn how it works, and find out why it's key to securing industrial networks against ransomware as ot and it environments converge. Learn five best practices for operational technology (ot) security and which tools provide the most comprehensive protection. operational technology controls business devices, processes, and events.

5 Ways To Keep Your Network Safe Pcmag Get an in depth overview of ot network segmentation, learn how it works, and find out why it's key to securing industrial networks against ransomware as ot and it environments converge. Learn five best practices for operational technology (ot) security and which tools provide the most comprehensive protection. operational technology controls business devices, processes, and events.
Comments are closed.